TL;DR
- Banks spend roughly $160B annually maintaining mainframe-dependent legacy systems — and 95% of US ATM transactions still run on IBM z/OS or AS/400 platforms. The mainframe isn’t the problem; the access layer is.
- The standard “dual-stack” model (Citrix or VMware/Omnissa Horizon for VDI + Attachmate, Rocket BlueZone, or IBM PCOMM for terminal emulation) creates fragmented licensing, infrastructure, MFA, session recording, and audit trails — adding up to $20M+ over five years for a 5,000-user bank.
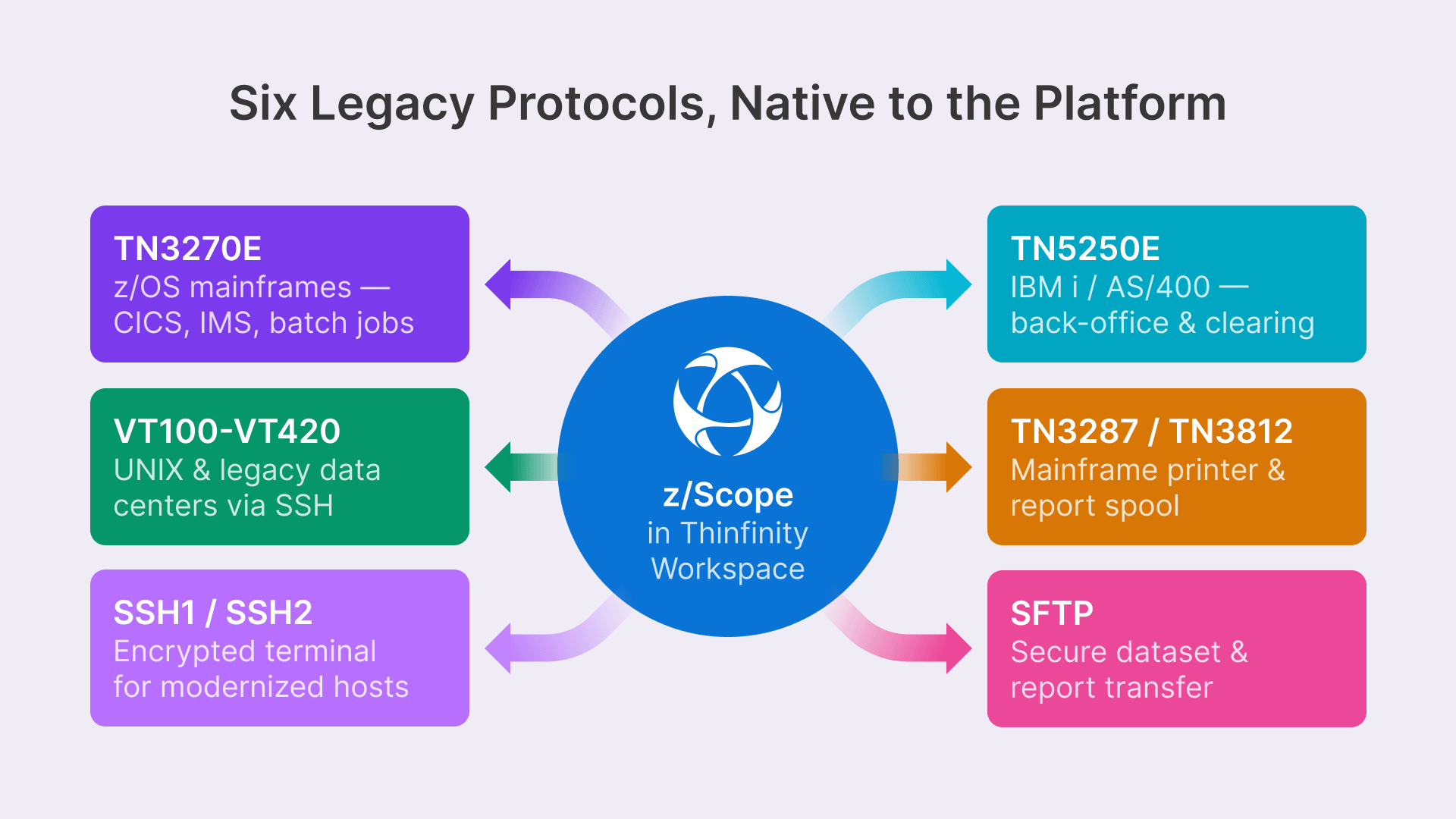
- Thinfinity Workspace is the only VDI platform with terminal emulation (TN3270E, TN5250E, VT, SSH, SFTP) architected natively into the platform via z/Scope — single authentication, single session recording, single management console.
- A 2,000-user bank moving from a Citrix + BlueZone dual-stack to Thinfinity unified on OCI saves $10.2M over 5 years (50% TCO reduction), with payback in 18–24 months.
- Typical migration runs 8–12 weeks across four phases: protocol assessment + z/Scope pilot, unified VDI deployment, parallel-operation department rollout, then legacy emulator decommission.
The $200 Billion Legacy Problem: Why Banks Can’t Escape the Mainframe
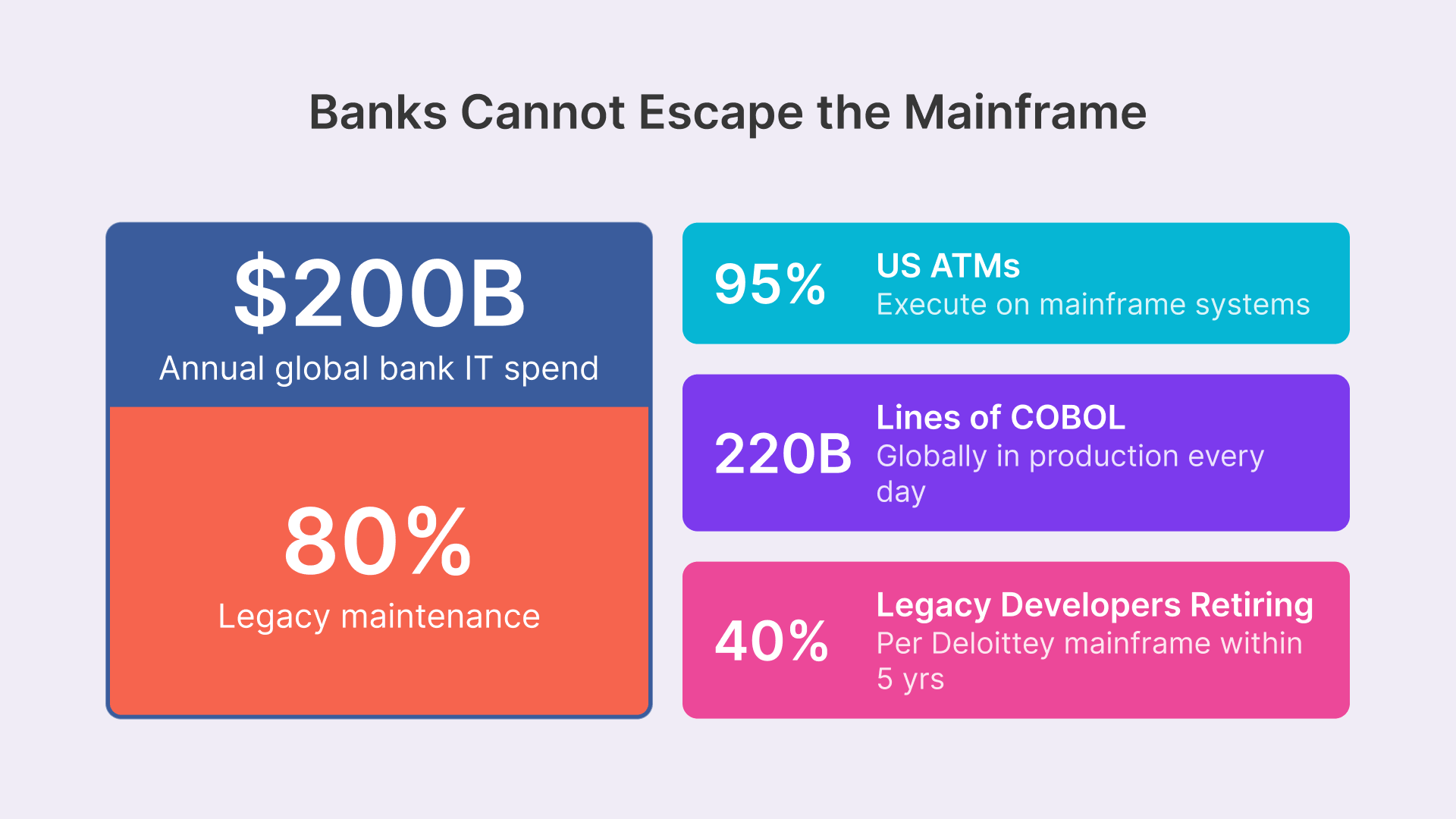
The global banking industry faces a paradox that no amount of cloud migration can resolve: the mainframe is simultaneously mission-critical and increasingly difficult to support. Banks collectively spend approximately $200 billion annually on information technology, and roughly 80% of that expenditure—some $160 billion—is devoted to maintaining mainframe-dependent legacy systems. This isn’t a legacy technology that will fade; it’s the foundation of modern banking itself. Consider the scale: 220 billion lines of COBOL code run in production daily across global financial institutions. Approximately 95% of ATM transactions in the United States execute on mainframe systems. Globally, 43% of all banking systems—transaction processing, account management, clearing and settlement—still operate on IBM z/OS or comparable mainframe platforms. The mainframe is not going away.
Yet the workforce sustaining these systems is aging rapidly and shrinking. The average COBOL programmer is approximately 60 years old. Deloitte’s latest workforce analysis estimates that 40% of legacy mainframe developers will retire within the next five years. In the interim, 79% of companies report difficulty finding qualified mainframe talent. Universities no longer teach COBOL; the language has become a specialized, high-value skill concentrated among aging practitioners. When a senior COBOL developer retires, banks cannot simply hire a replacement. The result is a perfect storm: mission-critical systems that must run indefinitely, underpinned by code that few new developers understand, supported by a workforce that is diminishing by the year.
The challenge, however, is not whether banks need to replace the mainframe. They don’t. The mainframe itself is not the problem; it’s extraordinarily reliable, scalable, and secure for the use cases it was designed for. The real problem is the access layer—how employees, partners, contractors, and distributed teams access mainframe and AS/400 systems. Legacy terminal emulation solutions designed in the 1990s and early 2000s were built for corporate networks where every employee had a thick-client terminal emulator installed on their workstation. In 2026, that architecture is untenable. Banking is global, decentralized, and distributed. Employees work from home, from branch offices, from partner networks, and increasingly from anywhere. Legacy emulators cannot support this. They are incompatible with modern security frameworks, they impose massive license costs at scale, and they fragment the user experience when combined with Windows desktop virtualization. The mainframe isn’t the problem. The access layer is.
The Dual-Stack Problem: VDI + Terminal Emulation as Separate Silos
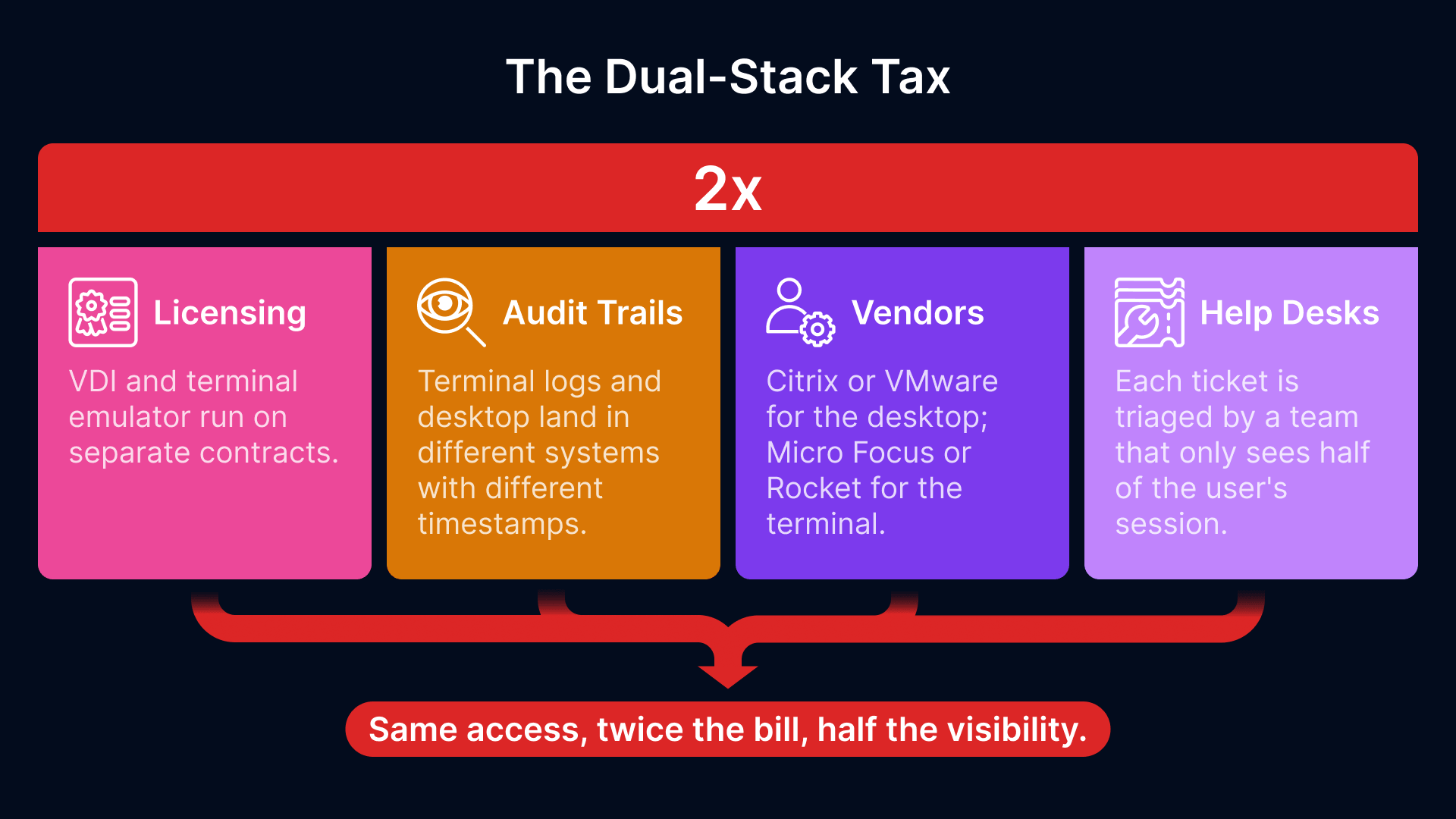
How Banks Access Mainframes Today
The typical architecture at a mid-sized bank or large financial institution is a dual-stack system: one system for Windows desktop virtualization (usually Citrix Citrix Virtual Apps and Desktops, or VMware Horizon) and a completely separate system for mainframe and AS/400 terminal emulation (typically Attachmate, Rocket BlueZone, IBM PCOMM, or Micro Focus Reflection).
These two systems are independently licensed, independently managed, independently secured, and independently audited. When a user logs in, they authenticate into VDI, receive a Windows desktop session running on Citrix or VMware infrastructure, and then launch a separate terminal emulator application. If they need to access the mainframe or AS/400, they click that icon, launch a separate emulator session (often requiring a second set of credentials), and establish a separate TN3270 or TN5250 connection. If the VDI session is on-premises and the terminal emulator is on-premises, the architecture is simple but inflexible. If one or both move to the cloud, the complexity multiplies: separate licensing agreements with different vendors, separate infrastructure deployments across cloud regions, separate identity management integrations, separate session recording and audit trail systems.
The terminal emulator is frequently thick-client software installed on each endpoint or published via Citrix AppStream or VMware App Volumes. This approach creates license sprawl: if you have 2,000 employees who need mainframe access, you purchase 2,000 licenses of Rocket BlueZone or IBM PCOMM at roughly $100-150 per license, per year. But this is merely one cost center among many. You must also manage the emulator deployment across thousands of endpoints, patch security vulnerabilities promptly, enforce macro policies (most emulators support keystroke automation macros, which are frequently stored in plaintext), and ensure compliance with centralized session recording. Every component of this stack—licensing, management, security, compliance—is fragmented.
The TCO of Running Parallel Stacks
To understand why the dual-stack approach is financially indefensible at scale, examine a typical cost model for a 1,000-user banking environment:
| Cost Category | Dual-Stack (VDI + Separate Emulator) | Thinfinity Unified Platform |
|---|---|---|
| VDI licensing (per user/year) | $350–500 | Included |
| Terminal emulator licensing (per user/year) | $100–150 | Included |
| Infrastructure (servers, load balancers, storage) | $500K–800K annually | $300K–450K annually |
| Endpoint management (MDM, patch management, AV) | $80–120/user/year | Reduced 70% (stateless sessions) |
| Security & compliance (separate audit, integration) | $200K–400K annually | $100K–150K annually |
| IT admin overhead (provisioning, support, licensing) | $300K–600K annually | $100K–200K annually |
| Total Year 1 (1,000 users) | $1.65M–2.15M | $900K–1.2M |
| Total 5-year cost | $8.25M–10.75M | $4.5M–6M |
| 5-year savings | — | $3.75M–4.75M (40-60% reduction) |
These numbers reveal the financial leverage of a unified platform. By consolidating VDI and terminal emulation into a single system with unified licensing, unified infrastructure, and unified management, banks eliminate redundant cost centers and dramatically reduce operational overhead. The annual savings per 1,000-user cohort is approximately $750K–950K, or $3.75M–4.75M over five years. For a 5,000-user enterprise (typical for a mid-sized regional bank), the five-year savings exceed $20 million.
Security Gaps in the Dual-Stack Model
Beyond cost, the dual-stack approach creates critical security and compliance gaps:
- Credential fragmentation: Users maintain separate credentials for VDI (Windows domain) and terminal emulation (mainframe/AS400). If either system is compromised, the other remains exposed. Multi-factor authentication (MFA) is frequently enforced only at the VDI layer, leaving the terminal emulation system vulnerable to brute-force attacks. A compromised mainframe credential is difficult to revoke immediately across all emulator instances.
- Plaintext macro storage: Terminal emulators frequently store keystroke macros—automation sequences for common mainframe operations—in plaintext files. These files often contain hardcoded credentials, screen coordinates, and navigational commands. An attacker gaining access to a trader’s or back-office staff member’s endpoint can extract these macro files and replay them to perform unauthorized mainframe transactions.
- Inconsistent session recording: VDI systems typically provide comprehensive session recording and playback. Terminal emulation systems do not. A trader using Citrix VDI might have their Windows desktop fully recorded, but their concurrent mainframe session (where they execute trades on legacy AS/400 systems) is unrecorded. Financial regulators (SEC, FCA, BaFin) increasingly expect immutable session recordings of all system access, including terminal sessions. Firms audited on this find themselves unable to produce recordings.
- No unified audit trail: When a user logs out, their VDI session and terminal emulation session are logged separately, in different systems, with different timestamps and different metadata. Reconstructing a complete user journey—”Show me everything this user accessed in a 30-minute window”—requires manually correlating logs from two systems, introducing the risk of gaps or inconsistencies. FFIEC auditors and DORA compliance officers flag this as a single point of failure.
Thinfinity Workspace: The Only VDI Platform with Native Terminal Emulation
Thinfinity Workspace is the only VDI solution that natively integrates terminal emulation protocols directly into the platform. No other VDI vendor—Citrix CVAD, VMware/Omnissa Horizon, Microsoft Azure Virtual Desktop—offers this capability. Citrix and VMware focus exclusively on Windows desktop virtualization and have repeatedly stated they will not integrate terminal emulation, viewing it as outside their core market. Thinfinity’s differentiation is that terminal emulation is not a bolt-on feature or a third-party add-on; it is architected into the platform through z/Scope, a terminal emulation engine built and maintained by the Thinfinity engineering team.
The key architectural insight is this: a modern VDI session is already a browser-delivered desktop environment. Instead of launching a terminal emulator application within that desktop, why not deliver terminal emulation as a native protocol handler in the same browser session? When a user opens Thinfinity Workspace, they receive a unified HTML5 desktop environment in the browser. They can open Windows applications (Outlook, Excel, Bloomberg Terminal), and they can simultaneously open terminal sessions (TN3270 for mainframe, TN5250 for AS/400) in the same browser window—side-by-side, in tabs, or in resizable panes. Single authentication event. Single MFA challenge. Single session recording. Single audit trail. Single management console.
According to one survey, 91% of IT leaders report that expanding their mainframes is a moderate or critical priority over the next year. But 71% say mainframe teams are understaffed, and 54% say they are underfunded.
z/Scope Terminal Emulation Capabilities
z/Scope is a comprehensive terminal emulation engine supporting the full range of legacy banking protocols:
- TN3270E protocol: IBM mainframe protocol for z/OS systems, supporting 80×24 and 132×27 screen formats, structured fields, and 3270 data stream extensions. TN3270E is the standard protocol for accessing IBM z/Series mainframes running CICS, IMS, and batch job processing.
- TN5250E protocol: IBM midrange protocol for System i (formerly AS/400), supporting 80×24 and 132×27 displays, function keys, and advanced screen attributes. TN5250E is universal in financial institutions running legacy back-office, clearing, and settlement systems on AS/400 platforms.
- VT100-VT420 terminal emulation: UNIX/Linux terminal protocols for SSH-based systems, supporting color, mouse, and modern terminal features. Enables access to UNIX-based banking systems and legacy data centers.
- TN3287 and TN3812 protocols: Printer redirection protocols for mainframe-attached printers, enabling remote print spooling and batch report retrieval.
- SSH1 and SSH2 support: Encrypted terminal access for legacy systems that have been modernized to support SSH (a gateway from TN3270 to SSH is common in cloud-native transitions).
- SFTP support: Secure file transfer for moving mainframe datasets, reports, and configuration files without requiring separate FTP or SFTP client applications.
All protocols are delivered HTML5 browser-native—zero client installation required. This is the critical difference from Attachmate, BlueZone, and Reflection, all of which require thick-client installation. A user can access a mainframe session from any device (laptop, tablet, workstation, BYOD phone) simply by opening a browser and logging into Thinfinity. No deployment, no client version management, no compatibility troubleshooting.
z/Scope supports modern security requirements that legacy emulators do not:
- TLS 1.3 encryption: All host connections are encrypted with TLS 1.3 or stronger, ensuring no one can sniff mainframe credentials or session data in transit.
- Multi-factor authentication (MFA) integration: Duos 2FA, SAML, Okta OAuth 2.0, ForgeRock, and other modern identity providers are seamlessly integrated. A user authenticates once with MFA at the Thinfinity gateway; subsequent terminal sessions inherit that authentication context.
- Session recording for terminal sessions: Every keystroke, screen change, and output from a terminal session is recorded in real-time and stored in Oracle Object Storage with WORM (Write-Once-Read-Many) protection. This is the compliance foundation for FFIEC, DORA, and SEC audits.
- Macro management: z/Scope allows administrators to centrally manage keystroke macros, removing the risk of plaintext credential storage on endpoints. Macros are stored in the Thinfinity infrastructure and executed server-side, never exposed to the user’s local device.
- Keyboard remapping and custom layouts: Terminal sessions support fully customizable keyboard mappings, enabling legacy keyboard shortcuts to work across modern devices (e.g., translating old IBM terminal function keys to modern keyboard layouts).
- Multi-session grid display: Users can display multiple terminal sessions in a grid view, monitoring multiple mainframe systems simultaneously—a critical capability for operations centers, trading floors, and batch job monitoring.
Architecture: Unified Access on OCI
The architectural elegance of Thinfinity + z/Scope on Oracle Cloud Infrastructure is that a single gateway serves both VDI desktops and terminal sessions. Here’s how it works:
- A user authenticates to the Thinfinity gateway with MFA and receives a session token valid for 8 hours.
- The token grants access to a dedicated VDI desktop session running on OCI compute (based on role and entitlements).
- Within the same session, the user can establish terminal connections to z/Scope-connected mainframes/AS400s.
- z/Scope maintains persistent, pooled connections to mainframe and AS/400 systems (e.g., CICS regions, IMS subsystems, QSYS on AS/400), multiplexing user sessions over a smaller number of host connections to reduce mainframe licensing (most mainframe vendors license by concurrent connections).
- All keystrokes, screen outputs, and mouse movements are recorded in a unified audit trail streamed to Oracle Object Storage.
- When the user logs out or the 8-hour session expires, both the VDI desktop and all terminal sessions are terminated, all session data is purged from compute, and the recordings are sealed in WORM storage for compliance.
This unified architecture eliminates every pain point of the dual-stack model: no separate authentication, no separate licensing, no separate infrastructure, no separate audit trails, no fragmentation.
Competitive Comparison: Why No Other VDI Vendor Can Do This
A direct comparison between Thinfinity + z/Scope and competing VDI platforms clarifies why this is a category-defining differentiation:
| Capability | Thinfinity + z/Scope | Citrix CVAD | VMware/Omnissa Horizon | Microsoft AVD |
|---|---|---|---|---|
| Native TN3270E emulation | Yes | No (third-party required) | No (third-party required) | No (third-party required) |
| Native TN5250E emulation | Yes | No (third-party required) | No (third-party required) | No (third-party required) |
| Native VT emulation | Yes | No (third-party required) | No (third-party required) | No (third-party required) |
| HTML5 browser-native terminal | Yes | No (Citrix app required) | No (VMware app required) | No (separate RDP) |
| Unified licensing (VDI + terminal) | Yes | No (separate licenses) | No (separate licenses) | No (separate licenses) |
| Single authentication for both VDI and terminal | Yes | No (separate logins) | No (separate logins) | No (separate logins) |
| Unified session recording | Yes | Partial (desktop only) | Partial (desktop only) | Partial (desktop only) |
| Session recording for terminal sessions | Yes, WORM-protected | No | No | No |
| MFA integrated into terminal sessions | Yes (DUO, SAML, Okta, ForgeRock) | No (emulator handles auth) | No (emulator handles auth) | No |
| (modernize green screens) | Yes, included | No | No | No |
| Air-gapped deployment support | Yes (z/Scope on private network) | Limited | Limited | Limited |
| Mainframe license optimization (connection pooling) | Yes (z/Scope pools reduce mainframe licensing) | No | No | No |
This comparison is unambiguous: Citrix, VMware, and Microsoft all treat terminal emulation as outside their product roadmap. When a customer needs both VDI and terminal access, the vendors recommend purchasing terminal emulation separately from companies like Attachmate or Micro Focus. This creates the dual-stack problem. Thinfinity eliminates it entirely by architecting terminal emulation into the platform from the ground up.
TCO Deep Dive: Unified vs. Dual-Stack for a 2,000-User Bank
To demonstrate the financial impact of consolidating to a unified platform, let’s model a realistic five-year cost projection for a 2,000-user regional bank transitioning from a dual-stack (Citrix CVAD + Rocket BlueZone) to Thinfinity Workspace with z/Scope on OCI.
| Cost Component | Dual-Stack (Citrix + BlueZone) Year 1 | Thinfinity Unified Year 1 | Dual-Stack 5-Year | Thinfinity 5-Year |
|---|---|---|---|---|
| VDI licensing (2,000 users @ $400/user/year) | $800,000 | Included | $4,000,000 | Included |
| Terminal emulator licensing (2,000 users @ $120/user/year) | $240,000 | Included | $1,200,000 | Included |
| Infrastructure (servers, storage, HA) | $1,200,000 | $700,000 | $6,000,000 | $3,500,000 |
| Network & connectivity (Citrix Gateway + dedicated circuits) | $400,000 | $250,000 | $2,000,000 | $1,250,000 |
| Endpoint management & MDM | $160,000 | $50,000 | $800,000 | $250,000 |
| Compliance & session recording (separate systems) | $300,000 | $100,000 | $1,500,000 | $500,000 |
| IT admin overhead (provisioning, patching, support) | $600,000 | $200,000 | $3,000,000 | $1,000,000 |
| Training & change management | $100,000 | $50,000 | $500,000 | $250,000 |
| Vendor support & maintenance | $250,000 | $150,000 | $1,250,000 | $750,000 |
| Hosting on OCI (estimated compute + storage) | On-premises | $400,000 | On-premises | $2,000,000 |
| TOTAL YEAR 1 | $4,050,000 | $1,900,000 | — | — |
| TOTAL 5-YEAR | — | — | $20,250,000 | $10,050,000 |
| 5-YEAR SAVINGS | — | — | — | $10,200,000 (50% reduction) |
The financial case is compelling: a 2,000-user bank moving to Thinfinity realizes $10.2 million in five-year savings compared to maintaining a dual-stack architecture. This translates to a payback period of approximately 18–24 months, after which all incremental cost is pure operational savings. For larger institutions (5,000+ users), the absolute savings exceed $25 million over five years, with even faster payback.
These projections are conservative and assume no change in user count or infrastructure requirements. In reality, banks often realize additional savings through reduced downtime (unified platform has fewer failure points), faster incident response (single pane of glass for troubleshooting), and reduced compliance audit costs (unified audit trail requires less manual correlation and review).
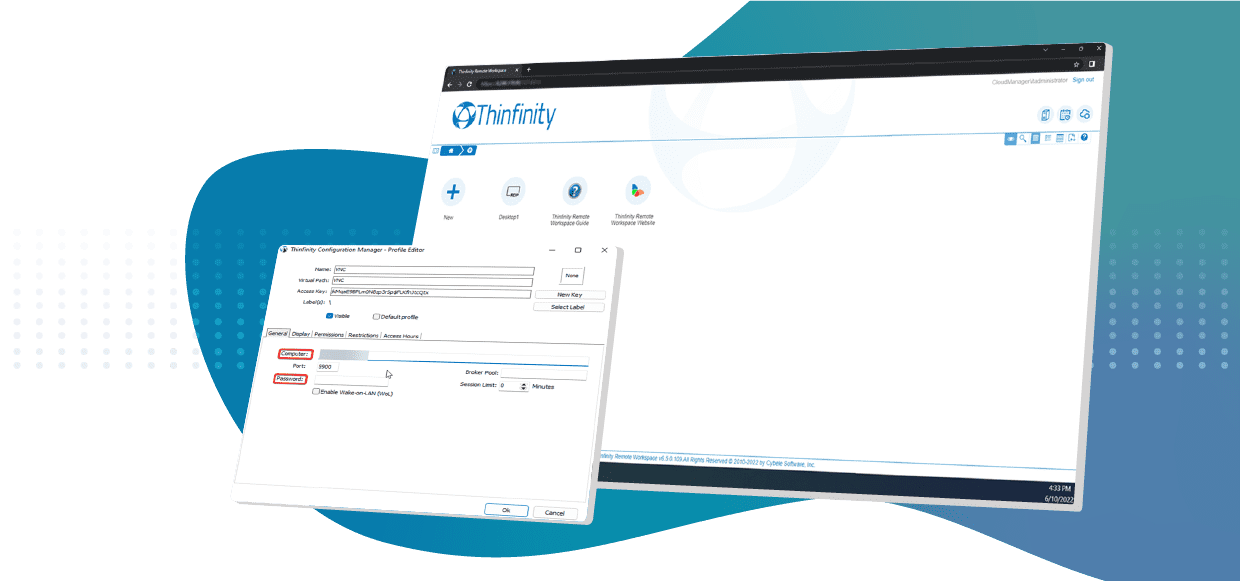
Implementation: From Dual-Stack to Unified in 8-12 Weeks
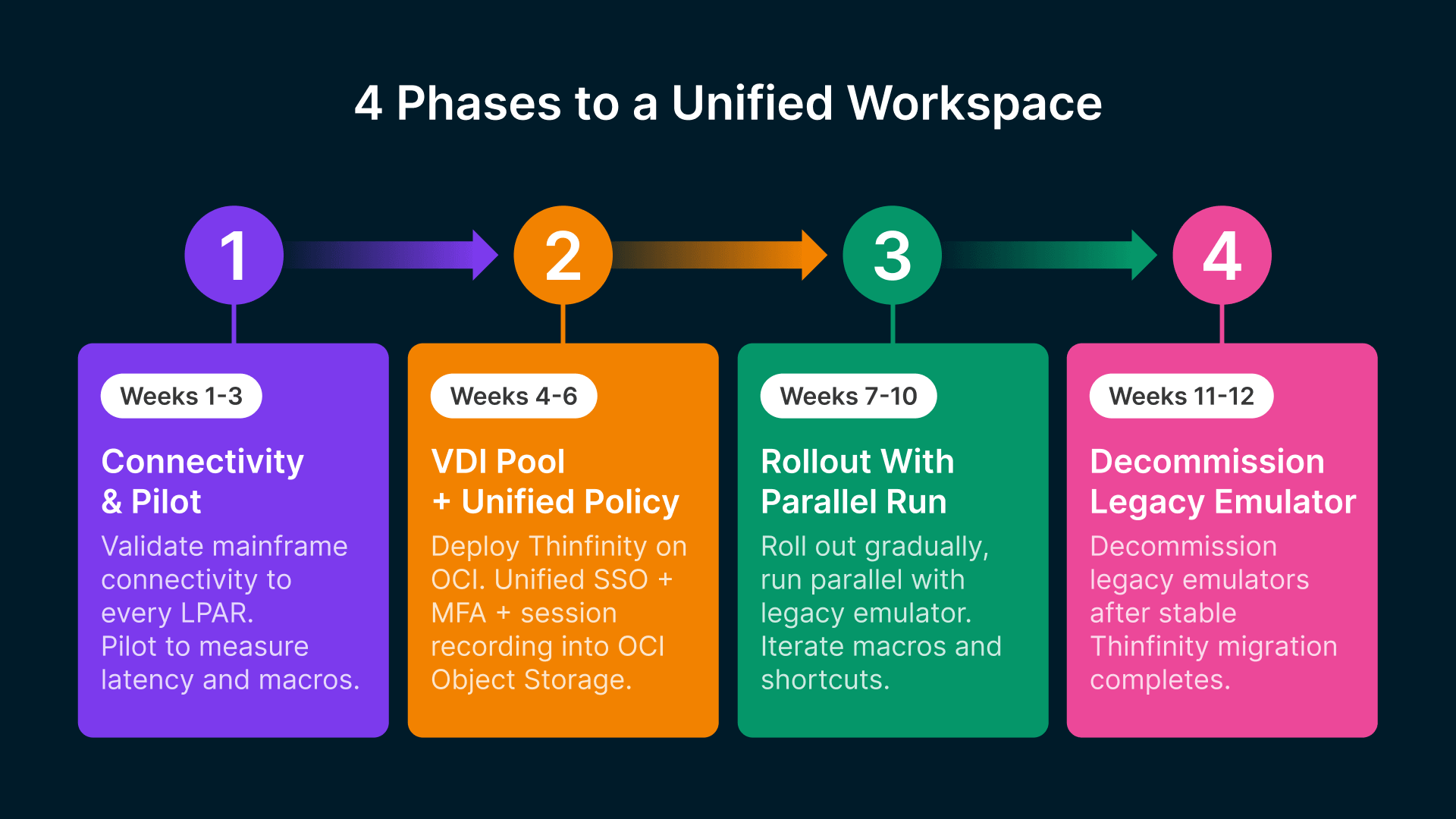
A typical transition from a dual-stack architecture (Citrix + separate terminal emulator) to Thinfinity Workspace with z/Scope follows a phased approach that minimizes disruption and maintains parallel operation during the transition period:
Phase 1: Mainframe Connectivity Assessment & z/Scope Pilot (Weeks 1–3)
Before deploying Thinfinity at scale, validate mainframe connectivity and z/Scope protocol support. Establish a dedicated z/Scope appliance (either on-premises or on OCI) and conduct protocol validation: verify TN3270E connectivity to each mainframe LPAR (logical partition), test TN5250E against all AS/400 systems, validate CICS region accessibility, and test IMS subsystem connections. Run z/Scope emulation against a small cohort of users (50–100) representing each business function (trading, operations, back-office). Measure latency, stability, and screen rendering fidelity. Collect feedback on keystroke lag (should be <100ms), screen update speed, and macro functionality. This phase validates architectural assumptions before large-scale deployment.
Phase 2: VDI Pool Deployment & Unified Session Policy (Weeks 4–6)
Deploy Thinfinity Workspace on OCI with initial compute capacity for 500 users. Configure single sign-on (SSO) with the organization’s identity provider (Active Directory, Okta, Azure AD). Set up unified authentication policies that apply MFA to both VDI sessions and terminal sessions. Configure session recording and route recordings to Oracle Object Storage. Define baseline security groups and network ACLs ensuring terminal connections egress only to designated mainframe/AS400 systems. Test failover and load balancing. Validate audit trail recording for both VDI and terminal activities.
Phase 3: Department Rollout with Parallel Operation (Weeks 7–10)
Begin controlled rollout to business units. Start with operations and back-office (lower risk profile) before trading or customer-facing teams. Run Thinfinity VDI and existing terminal emulator in parallel—users can access both systems during the transition. Measure adoption rates, collect feedback, identify missing macros or customizations. Make iterative adjustments to session policies, macro definitions, and terminal screen renderings. Scale compute capacity as adoption increases. This phase typically completes with 1,500–2,000 users active in Thinfinity and the legacy system in use for remaining users.
Phase 4: Legacy Emulator Decommission & License Termination (Weeks 11–12)
Once >90% of users have transitioned to Thinfinity and stability is verified (zero critical incidents over 2 weeks), begin decommissioning the legacy terminal emulator infrastructure. Revoke licenses for Attachmate, BlueZone, or Reflection. Decommission legacy emulator servers and storage. Document lessons learned and update disaster recovery procedures. Formally transition support responsibility to Thinfinity.
Throughout this process, it’s critical to involve end-users early, collect feedback, and iterate on keyboard macros, screen customizations, and user experience. Technical success is necessary but not sufficient; user adoption determines the overall project success. Thinfinity’s customer success team typically provides dedicated support during transitions, including custom macro development, keyboard mapping refinement, and troubleshooting. Most customers complete this transition with minimal business disruption and high user satisfaction.
Frequently Asked Questions
Does z/Scope support all IBM mainframe screen types and keyboard mappings?
Yes. z/Scope supports all 3270 data stream types including extended attributes, colors, and input method fields. Keyboard mapping is fully customizable; administrators can map legacy function keys (PF1-PF24) to modern keyboards, and z/Scope includes predefined profiles for IBM 3270, IBM 5250, and modern US/QWERTY layouts. The macro system supports full keyboard redefinition, replaying complex sequences identically across any layout.
Can we run green screen and Windows desktop applications in the same browser session?
Yes. Thinfinity delivers a unified HTML5 desktop environment in the browser. Users can open Windows applications (Outlook, Excel, Bloomberg Terminal, custom trading apps) and simultaneously open TN3270 or TN5250 terminal sessions in tabs, panes, or side-by-side windows. Single authentication covers all sessions; clipboard copy-paste and file transfer work across VDI desktop and terminal.
How does session recording work for terminal sessions?
z/Scope captures the full TN3270/TN5250 data stream in real time and streams it to Oracle Object Storage with WORM retention. Every keystroke, screen output, function key press, and host response is recorded; metadata (session ID, user, timestamp, host, applications, macros) is indexed in Oracle Autonomous Data Warehouse. Compliance teams can replay sessions at variable speed for forensic-grade audit, and FFIEC and SEC auditors can verify immutable recording of all mainframe access.
What happens to our existing Attachmate/BlueZone macros?
z/Scope has a macro migration engine that converts legacy emulator macros to z/Scope native format with roughly 95% fidelity—standard navigation, input, and function-key sequences convert transparently. Macros involving vendor-specific extensions or custom DLLs (typically the remaining 5%) may need manual rewriting. Thinfinity provides macro migration as part of implementation support, and post-migration all macros are stored centrally rather than on user devices.
Can Thinfinity connect to mainframes in air-gapped environments?
Yes. The z/Scope appliance is deployed inside the air-gapped network and maintains direct connectivity to mainframes and AS/400s, while the Thinfinity HTML5 client connects through a secured demarcation point (firewall, bastion host, or VPN concentrator). All terminal session traffic is encrypted end-to-end. Regulatory-grade deployments (government agencies, highly classified financial institutions) frequently use this architecture to maintain strict network segmentation.
How does MFA work for terminal sessions vs. desktop sessions?
Thinfinity’s unified authentication model applies MFA once at the gateway, regardless of whether the user accesses VDI desktops, terminal sessions, or both. The gateway issues an 8-hour session token after MFA validation (DUO, SAML, Okta OAuth 2.0, ForgeRock); both VDI and terminal sessions inherit it without a secondary challenge. This is more secure and more user-friendly than dual-stack architectures, where the terminal emulator typically has its own (often weaker) authentication.
What is the typical ROI timeline for consolidating to a unified platform?
Payback typically lands at 18–24 months. For a 2,000-user bank, annual savings are around $2M ($10.2M / 5 years), and transition cost (hardware, professional services, training) is typically $1.5M–2.5M. Larger institutions (5,000+ users) reach payback faster due to economies of scale, and non-financial benefits—reduced audit burden, easier onboarding—are realized immediately.
Conclusion: Mainframe Modernization Is a Business Imperative
The mainframe is not going away, but the access layer must modernize. Banks cannot afford to maintain dual-stack architectures that fragment licensing, infrastructure, management, and compliance. The $160 billion annual spend on legacy IT will not decrease; it will only increase if banks fail to modernize the access layer. The challenge is not replacing the mainframe—it’s making mainframe access sustainable for a decentralized, global workforce working from home, remote offices, and anywhere else.
Thinfinity Workspace with native z/Scope terminal emulation is the only VDI platform that directly addresses this challenge. By consolidating VDI and terminal access into a single platform with unified licensing, unified management, and unified compliance, banks achieve 40-60% reduction in TCO, eliminate the fragmentation that creates security and compliance gaps, and provide a modern user experience that appeals to younger staff entering the industry.
For CTOs evaluating mainframe access modernization, the choice is clear: either maintain a dual-stack architecture with all its attendant complexity and cost, or consolidate to Thinfinity and realize immediate financial and operational benefits. The mainframe is here to stay. The question is whether your access layer will be a source of cost and compliance risk, or a strategic advantage.