Executive Summary
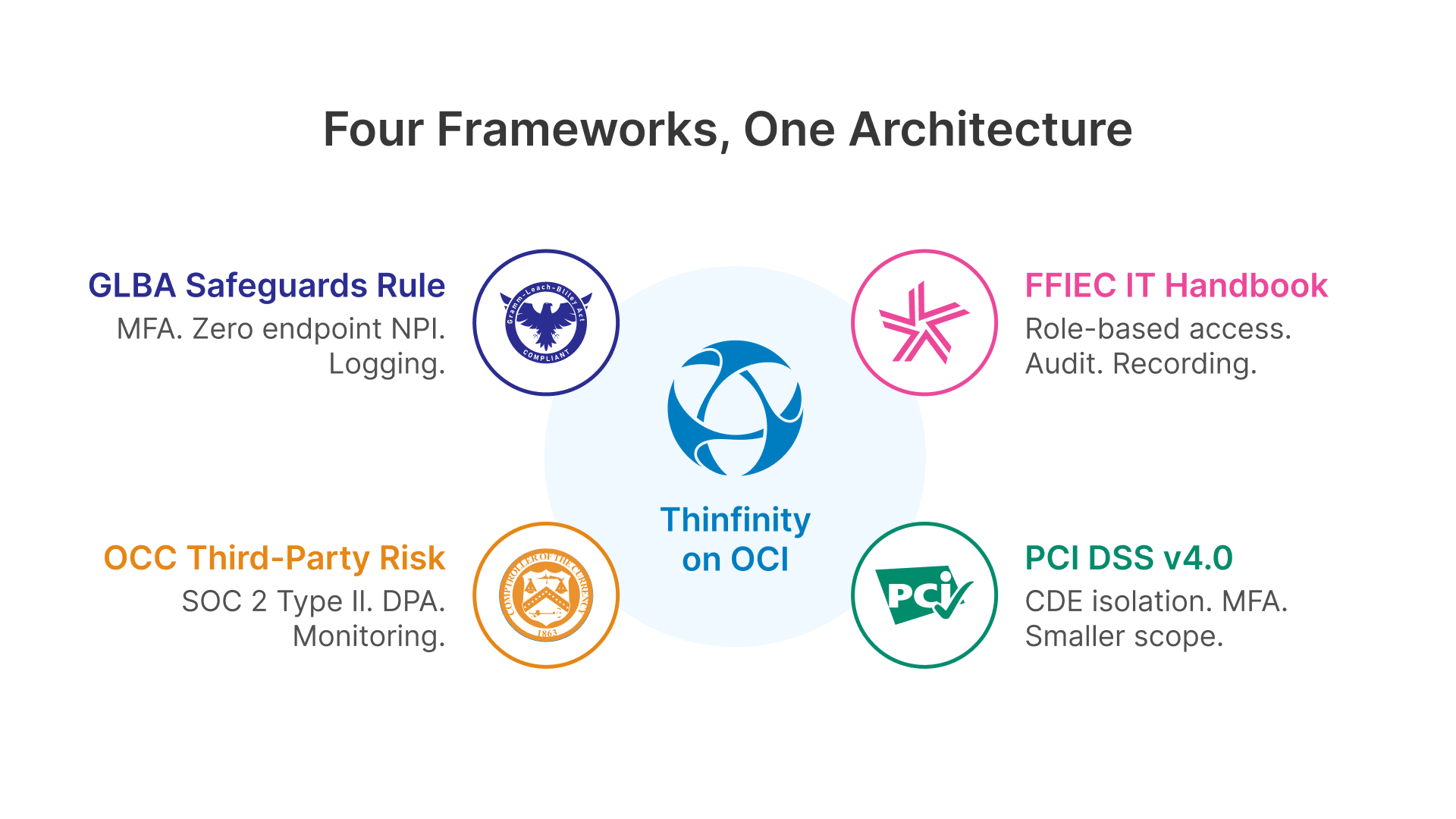
The regulatory environment for US financial institutions has undergone a fundamental shift in the past three years. The FTC’s 2023 Safeguards Rule amendments introduced prescriptive cybersecurity mandates in place of the previous principles-based approach. PCI DSS v4.0 enforcement became fully mandatory on March 31, 2025. The OCC and FDIC issued comprehensive third-party risk management guidance requiring detailed vendor due diligence and contractual controls. And FFIEC examination procedures have evolved to include increasingly granular assessments of endpoint security, access controls, and incident response capabilities.
For the 4,500+ community banks and 4,800+ credit unions in the United States—most managing these compliance obligations with lean IT staffs and constrained budgets—Virtual Desktop Infrastructure on Oracle Cloud Infrastructure offers a structural compliance advantage. Thinfinity Workspace on OCI centralizes the endpoint security controls that the GLBA Safeguards Rule now mandates, provides the automated audit logging that FFIEC examiners require as examination evidence, and eliminates the endpoint data residency risks that drive regulatory findings in IT examinations.
This article provides a compliance-mapped implementation guide for US financial institutions evaluating VDI on OCI as a modernization and risk-reduction strategy.
The 2026 US Banking Compliance Landscape
US bank IT teams operate within a multi-regulator compliance ecosystem where FFIEC examination procedures, FTC Safeguards Rule requirements, OCC guidance, FDIC directives, and PCI DSS standards all apply simultaneously. Each framework addresses endpoint security, access controls, and data protection from slightly different regulatory angles. Understanding how VDI architecture maps to each framework—and how these frameworks overlap—is essential for building an examination-ready deployment that satisfies all regulators with a single architecture.
GLBA Safeguards Rule 2023 Amendments: Prescriptive Requirements
The FTC’s 2023 amendments to the GLBA Safeguards Rule fundamentally changed how financial institutions approach cybersecurity compliance. The prior framework was principles-based, allowing institutions broad discretion in how they implemented security. The 2023 amendments—effective June 2023 and now fully deployed across all regulated institutions—introduced specific, prescriptive requirements that apply to all financial institutions handling nonpublic personal information (NPI).
The amendments that most directly impact endpoint and application architecture are:
- Multi-Factor Authentication (MFA): Now mandatory for any individual accessing customer NPI, including bank employees accessing core banking applications from workstations. VDI enforces MFA at session initiation—the user must authenticate twice (once to their directory service via MFA, once to the VDI Gateway) before gaining access to any desktop session. This provides a single MFA enforcement point that covers access from any device or location—branch workstation, remote laptop, or personal device on a branch network.
- Encryption in Transit and at Rest: NPI must be encrypted in both transit and at rest without exception. In a VDI architecture, customer data never reaches the endpoint device. The endpoint receives only a compressed screen stream encoded over TLS 1.3. All customer data remains on OCI Block Volume or Object Storage with encryption at rest enforced by OCI. This architectural isolation eliminates a critical compliance risk that distributed thick-client environments cannot easily address.
- Annual Penetration Testing and Semi-Annual Vulnerability Assessments: All systems processing or storing NPI must be tested annually. VDI centralizes NPI processing onto OCI-hosted session hosts—reducing the pentesting scope compared to a distributed thick-client environment where every workstation is a potential test target. A bank with 300 user endpoints can reduce annual pentesting scope to the OCI VCN, the Thinfinity Gateway, and the session host pool.
- Designated Qualified Individual: Every institution must designate a Qualified Individual (effectively a CISO) responsible for oversight of the information security program. VDI’s centralized session logging and policy enforcement simplifies the documentation this role must produce for annual board reporting and FTC audits.
- 30-Day Breach Notification: Effective May 2024, institutions must notify the FTC within 30 days of discovering a security event affecting NPI of 500+ consumers. Thinfinity’s session recording capability provides the forensic evidence required to characterize the scope of any incident—which user accessed what data, when, and for how long—supporting rapid breach notification decisions.
GLBA Safeguards Rule 2023 Control Mapping
VDI centralizes MFA enforcement at the Gateway layer, eliminates endpoint storage of NPI, provides centralized session logging for audit compliance, and reduces the scope of systems requiring annual penetration testing. All five core Safeguards Rule controls are satisfied at the architecture layer.
FFIEC IT Examination Handbook and Examination Procedures
FFIEC examination procedures—applied by OCC, FDIC, Federal Reserve, and NCUA examiners—evaluate bank IT programs against the NIST Cybersecurity Framework 2.0 and FFIEC IT Handbook’s detailed standards. Since 2023, examination procedures have become increasingly granular in their assessment of endpoint security, access controls, and incident response capabilities. Examiners now specifically look for evidence of centralized access logging, MFA enforcement, remote access encryption, and role-based access control implementation.
The VDI architecture directly satisfies the examination focus areas that examiners most commonly assess:
- Access Control and Least-Privilege Enforcement: FFIEC examiners assess whether access to sensitive systems is restricted to authorized users with documented business need. VDI’s role-based session policies enforce least-privilege at the session layer—users access only the applications assigned to their role, and session policies prevent clipboard sharing and USB transfers. This provides clear, auditable evidence of least-privilege control.
- Audit Trail Completeness and Tamper Evidence: Examiners review whether access logs are complete, tamper-evident, and retained per policy. Thinfinity session logs provide complete access records exportable to institutional audit infrastructure or SIEM systems—user identity, session timestamps, source IP, device type, and session duration captured for every connection. With OCI Object Storage object lock enabled, session recording files are tamper-evident.
- Remote Access Security: FFIEC guidance now explicitly addresses remote access controls, requiring encrypted sessions, MFA, and continuous monitoring. VDI provides all three natively: TLS 1.3 encrypted sessions, Gateway-enforced MFA, and optional session recording for remote user roles.
- Endpoint Risk Management: Examiners assess the security posture of endpoint devices used to access bank systems. VDI eliminates this risk entirely—the endpoint is a thin client receiving only screen updates, with no NPI storage and limited local processing. This is a structural compliance advantage over distributed architectures.
We know well that cyber threats pose real risks to the banking system. We also recognize that community banks may have unique needs in preventing, remediating, and responding to cyber threats.
FFIEC Examination Readiness
Prepare your institution for examination by documenting access control policies, exporting sample session logs, and preparing OCI vendor risk assessment documentation (SOC 2 Type II, ISO 27001 certifications). These materials will address 70% of FFIEC IT examination questions on access control, audit, and remote access.
OCC Third-Party Risk Management Guidance (June 2023)
The OCC, FDIC, and Federal Reserve’s joint guidance on third-party risk management introduced more prescriptive requirements for institutions’ assessment and ongoing monitoring of cloud vendors. This guidance requires institutions to conduct due diligence on cloud providers before deployment, establish contracts with specific data handling provisions, and implement ongoing vendor performance monitoring.
For a bank deploying VDI on OCI, the guidance requires documentation of:
- Vendor due diligence: SOC 2 Type II certification, SOC 1 Type II audit reports, ISO 27001 certification, penetration test reports, and incident response procedures available under NDA
- Contractual provisions: Data processing agreement (DPA) with audit rights, incident notification requirements, data location guarantees, and vendor exit strategy
- Ongoing monitoring: Quarterly vendor compliance reports, annual security assessments, and incident notification processes
Oracle’s OCI maintains current SOC 2 Type II and SOC 1 Type II certifications available to regulated institutions under NDA. OCI’s standard Data Processing Agreement includes contractual provisions required by OCC guidance. OCI operations maintain incident response procedures with 24/7 support for regulated institution customers. Institutions should engage their compliance and legal teams to complete the formal OCC-required vendor risk assessment before production deployment.
PCI DSS v4.0: MFA, Access Control, and Cardholder Data Environment Scope
For banks that process, store, or transmit cardholder data—which includes virtually all institutions offering debit cards, credit cards, or merchant services—PCI DSS v4.0 introduced new controls that VDI directly addresses. Version 4.0, fully enforceable since March 31, 2025, includes mandatory MFA for all access to the Cardholder Data Environment (CDE), new Requirement 2 controls on secure configurations, and enhanced Requirement 7 controls on access management.
In a VDI environment, MFA is enforced at the Thinfinity Broker for all CDE access. Cardholder data processing occurs on centralized OCI session hosts, not on endpoint devices. Endpoints receive only an encoded screen stream with zero cardholder data storage. This allows institutions to reduce their PCI DSS pentesting scope from potentially hundreds of distributed workstations to the controlled scope of the OCI VCN, Gateway, and session host pool.
While fundamental security controls addressed throughout the maturity levels of the CAT are sound, several new and updated government and industry resources are available that financial institutions can leverage to better manage cybersecurity risks.
Regulatory Framework Comparison: VDI Control Alignment
| Regulation/Standard | Key Requirement | Thinfinity on OCI Implementation |
|---|---|---|
| GLBA Safeguards Rule 2023 | MFA for NPI access | Gateway enforces MFA at session initiation |
| GLBA Safeguards Rule 2023 | Encryption in transit and at rest | TLS 1.3 transport; no data at endpoint; OCI encryption at rest |
| GLBA Safeguards Rule 2023 | Annual penetration testing | Reduced scope: OCI VCN, Gateway, session hosts only |
| FFIEC IT Handbook | Least-privilege access control | Role-based session policies + application access restriction |
| FFIEC IT Handbook | Complete audit trail | Thinfinity session logs + OCI Object Storage with object lock |
| FFIEC IT Handbook | Remote access encryption & MFA | TLS 1.3 encrypted sessions + Gateway MFA + optional recording |
| OCC Third-Party Risk (2023) | Vendor SOC 2 certification | OCI SOC 2 Type II + SOC 1 Type II + ISO 27001 |
| OCC Third-Party Risk (2023) | Data processing agreement | OCI DPA includes audit rights and incident notification |
| PCI DSS v4.0 | MFA for CDE access | Gateway MFA + session isolation for cardholder data processing |
| PCI DSS v4.0 | Requirement 7 access controls | Role-based policies + session policies enforce principle of least privilege |
Reference Architecture: Banking VDI on OCI
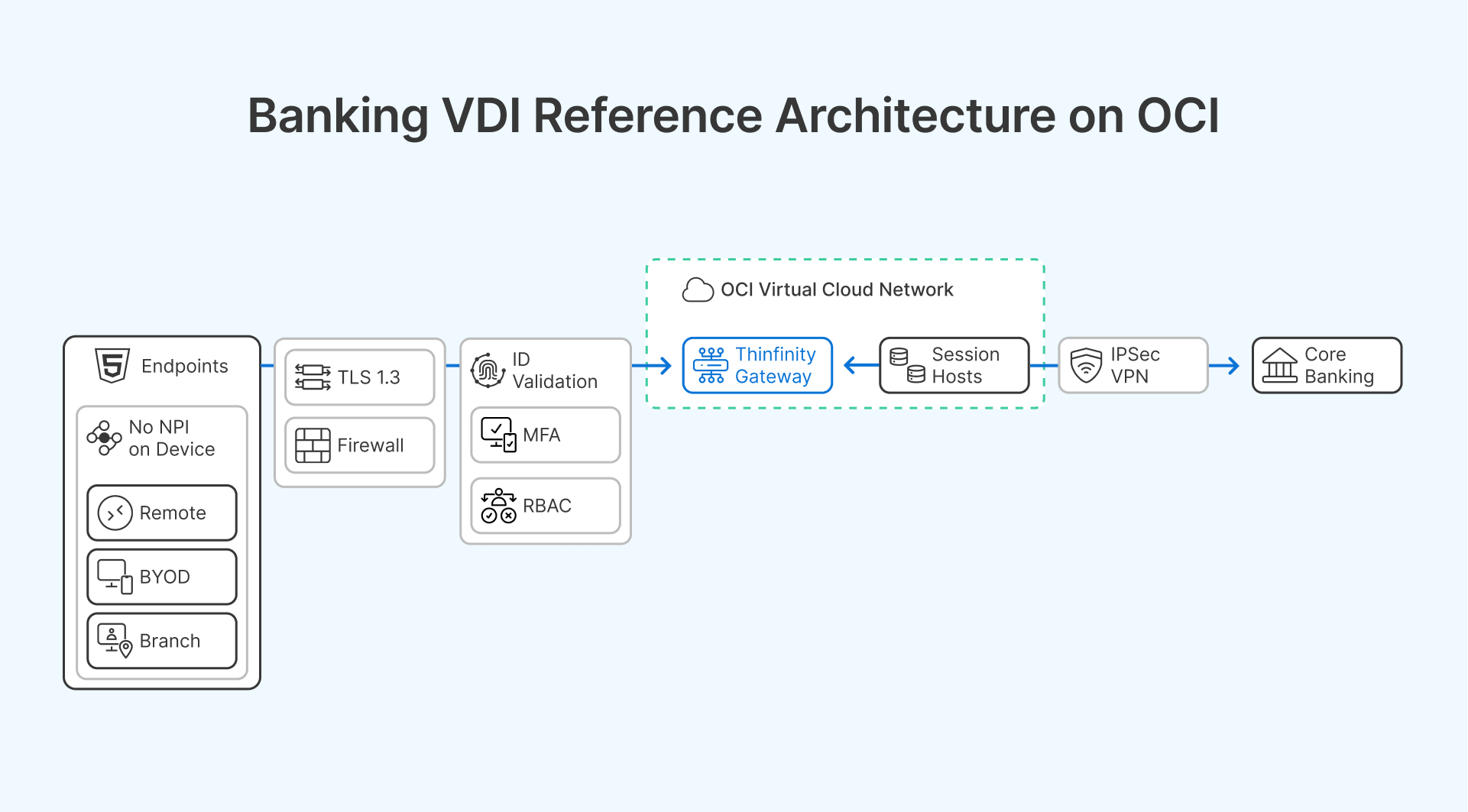
The following architecture targets a community or regional bank with 200–2,000 users, primary OCI region in the continental US, branch network, and remote or hybrid workforce. It is sized and scoped for community bank IT budgets and staff capacity.
OCI Region Selection for US Banking Compliance
OCI operates commercial cloud regions in Ashburn, VA (US East), Chicago, IL (US Midwest), and Phoenix, AZ (US West). For community banks with most users in the Northeast and Midwest, the Ashburn and Chicago regions provide the lowest latency. For institutions with FedRAMP requirements or government banking relationships, OCI’s US Government cloud regions (also in Ashburn and Chicago) provide FedRAMP High authorization.
- Ashburn, VA (US East): Recommended for Northeast and Mid-Atlantic banks. Lowest latency to Boston, New York, Philadelphia, and Washington DC corridors.
- Chicago, IL (US Midwest): Recommended for Midwest and Central banks. Optimal latency to Minneapolis, St. Louis, Kansas City, and Chicago markets.
- Phoenix, AZ (US West): Recommended for Western regional banks. Serves customers in Mountain West and Pacific time zones.
Infrastructure Layer: Compute, Network, and Storage
The following infrastructure components form the foundation of a banking-grade VDI deployment:
- Compute Shapes for Community Bank Scale: VM.Standard.E4.Flex (4 vCPU, 16 GB RAM) session hosts support 10-12 concurrent users per host. A 200-user bank requires 18-20 session host VMs for full concurrent load; a 500-user bank requires 45-50 VMs. OCI’s per-second billing makes dynamic provisioning cost-effective.
- Network Design: OCI VCN for VDI workloads, connected to the bank’s core banking infrastructure via IPSec VPN (256-bit encryption) or FastConnect dedicated interconnect. For community banks using Jack Henry, Fiserv, or FIS hosted core banking, connectivity to those environments is established from the OCI VCN via the banking network’s existing private interconnects—no customer data traverses the public internet.
- Storage Architecture: OCI Block Volume for session host OS (typically 100 GB, mirrored across availability domains); OCI File Storage for FSLogix Profile Containers (user documents, settings, app data); OCI Object Storage for session recording archives with retention policies (minimum 12 months recommended for FFIEC examination readiness).
Core Banking Application Compatibility Table
| Banking Platform | Provider | Deployment Model | Compatibility Notes |
|---|---|---|---|
| SilverLake System | Jack Henry & Associates | Windows client | Fully compatible. No modification required. Connects to Jack Henry hosted environment over existing bank network. |
| Episys | Jack Henry & Associates | Browser + Windows client | Compatible via Thinfinity browser delivery and Windows client in session host. |
| Premier / Precision / Signature | Fiserv | Windows client | Fully compatible. Windows client installed on session hosts; connects to Fiserv environment over existing bank network. |
| Profile / IBS | FIS (formerly Fiserv) | Windows + browser | Fully compatible. Both Windows and browser access supported in VDI environment. |
| D3 Banking System | NCR Voyix | Browser-based | Fully compatible. Delivered via Thinfinity RBI (Rich Browser Interface). |
| nCino | Salesforce-based | Browser application | Fully compatible. Accessed through Thinfinity virtual desktop browser. |
Security and Compliance Controls Layer
- MFA Enforcement at Gateway: Thinfinity Gateway enforces MFA at session initiation for all users accessing NPI through virtual desktops. Compatible with Microsoft Authenticator, Duo Security, Okta Verify, RSA SecurID, and FIDO2 hardware tokens. If the institution already uses one of these MFA providers, no additional MFA infrastructure deployment is required—Gateway integrates directly with existing SAML endpoints.
- Session Recording and Forensics: Configurable per user role. Recommended for roles with access to NPI (tellers, loan officers, BSA/AML analysts, compliance staff). Session recordings stored in OCI Object Storage with object lock enabled to prevent tampering—supporting the audit evidence requirements of FFIEC examinations and GLBA Safeguards Rule incident response investigation.
- Endpoint Isolation Controls: Clipboard, USB, and local file transfer restrictions configurable per role policy. For users accessing the PCI DSS Cardholder Data Environment, clipboard isolation and USB block are enforced by default—eliminating a common PCI DSS scope expansion risk.
- Access Logging and SIEM Integration: All session events exported to the institution’s SIEM (Splunk, Microsoft Sentinel, IBM QRadar, others) via syslog or REST API. Session logs provide the user access records required for FFIEC examination evidence, GLBA annual board reporting, and incident response analysis.
FFIEC Examination Readiness: What Examiners Look For
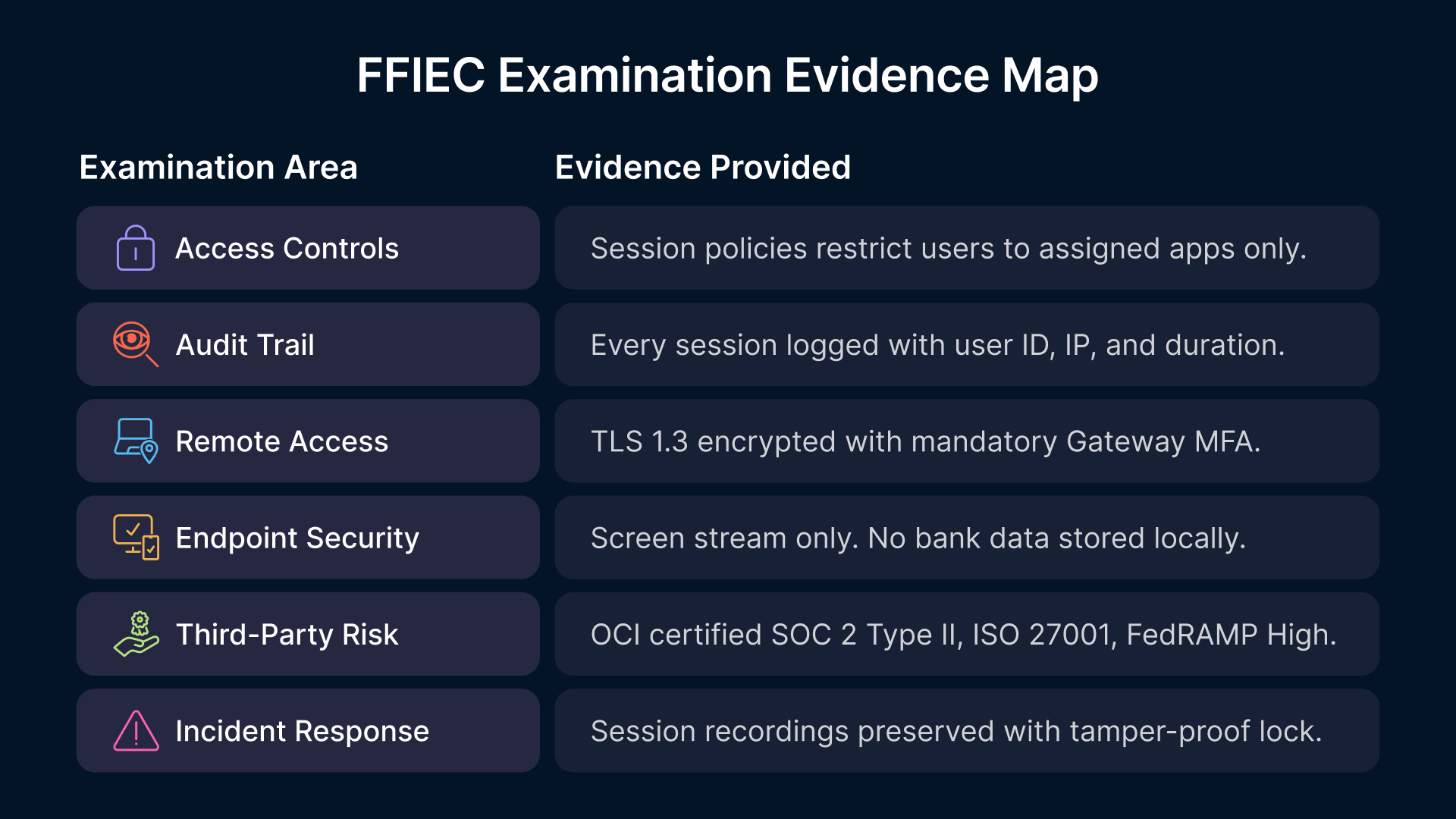
FFIEC examiners assess bank IT programs against detailed IT Handbook standards using examination procedures that have become increasingly prescriptive since 2023. Examiners evaluate cybersecurity programs across seven primary domains: access controls, audit trails, remote access security, endpoint security, third-party risk management, incident response capability, and regulatory compliance mapping.
The following table maps the most common FFIEC examination focus areas to the controls provided by Thinfinity on OCI:
| FFIEC Examination Area | What Examiners Assess | Thinfinity on OCI Provides |
|---|---|---|
| Access Controls | Role-based access + least privilege; MFA for sensitive systems; segregation of duties | Session policies enforce role-based app access; Gateway MFA; policy prevents unauthorized system access |
| Audit Trail | Complete, tamper-evident logs; retention per policy; exportability to external audit systems | Thinfinity logs + OCI Object Storage with object lock; exported to SIEM; retention policies configured |
| Remote Access | Encrypted sessions; MFA enforcement; monitoring of remote connections; geo-location logging | TLS 1.3 encrypted; Gateway MFA required; session recording for remote users; source IP logged per session |
| Endpoint Security | Controls on endpoint devices accessing sensitive systems; endpoint encryption; device compliance | Endpoint receives screen stream only—no NPI stored locally; policy prevents USB/clipboard transfers; no local data risk |
| Third-Party Risk | Vendor SOC 2/ISO certifications; contracts with DPA; audit rights; incident response SLAs | OCI SOC 2 Type II + ISO 27001 + FedRAMP High; DPA included; 24/7 support for breach notification |
| Incident Response | Forensic capability; breach scope determination; evidence preservation; notification procedures | Session recording provides forensic evidence; logs support breach scope analysis; evidence preservation via object lock |
| Compliance Mapping | Documentation of how controls address specific regulatory requirements; board reporting; annual updates | Centralized logging simplifies GLBA Qualified Individual annual board report; documentation generated automatically |
Deployment Model: Right-Sized for Community Bank IT Teams
Community banks face a VDI adoption barrier that regional and money-center banks do not: limited in-house IT capacity to deploy, configure, and operate complex VDI infrastructure. The Thinfinity on OCI deployment model is specifically designed to minimize operational overhead and fit within the constraints of lean IT teams managing 2-3 staff members.
Typical Deployment Timeline: 200–500 User Bank
- Week 1–2: OCI Tenancy Setup and Network Connectivity (2-3 days active IT time). OCI account creation, VCN configuration, IPSec VPN to the bank’s existing network, initial Thinfinity Workspace Broker and Gateway deployment.
- Week 3–4: Application Validation and Compliance Mapping (3-4 days). Install core banking applications on the session host pool, run UAT with 5–10 pilot users, document GLBA Safeguards Rule controls at each architecture layer for the Qualified Individual’s annual board report.
- Week 5–8: Pilot with FFIEC Documentation (ongoing). Expand to 25–50 users across one branch or department. Generate first month’s session logs, verify audit evidence completeness. Complete OCC third-party risk assessment documentation for OCI.
- Week 9–14: Full Rollout (department-by-department). Maintain physical workstations as fallback for two weeks post-cutover per department. Conduct helpdesk training before each department transition.
Annual Operational Overhead for Lean IT Teams
For a community bank with 200–500 users, the ongoing operational overhead is designed to fit within 2–3 staff members managing the infrastructure:
- Patch Management: OCI session host VMs patched via standard Windows Update or WSUS—identical process to physical workstations. Gold image updates applied to the session host pool via Thinfinity’s pool management console. No endpoint patch management required.
- GLBA Safeguards Rule Annual Review: Thinfinity session logs and OCI access reports provide input data for the Qualified Individual’s annual board report. Reporting is largely automated—no additional manual documentation burden.
- FFIEC Examination Preparation: Session log exports and OCI compliance reports (SOC 2, ISO 27001) provide the documentation package for examiner review. Timeline: 1-2 weeks of IT staff time to organize materials before examination.
- Penetration Testing Scope: GLBA-required annual pentesting scope covers the OCI VCN, the Thinfinity Gateway, and the session host pool—substantially smaller and more defensible than testing hundreds of distributed workstations. Cost and resource requirements typically 30-40% lower than thick-client pentesting.
- User Support and Helpdesk: Session host infrastructure managed similarly to physical workstations. User experience is familiar—Windows desktop with standard applications. Helpdesk training typically requires 1-2 weeks before initial rollout.
Map Your Bank’s Compliance Requirements to OCI
Thinfinity’s delivery team works with community and regional bank IT teams to design VDI deployments that satisfy GLBA Safeguards Rule, FFIEC examination expectations, and OCC third-party risk requirements. Schedule a 30-minute compliance consultation and receive a GLBA control mapping document specific to your institution.
Frequently Asked Questions
Does Thinfinity on OCI satisfy the GLBA Safeguards Rule MFA requirement?
Yes. The Thinfinity Gateway enforces MFA at session initiation for all users accessing NPI through virtual desktops, integrating natively with Microsoft Authenticator, Duo Security, Okta Verify, RSA SecurID, and FIDO2 hardware tokens. This satisfies the GLBA Safeguards Rule MFA requirement at a single enforcement point, covering access from any device—branch workstations, remote laptops, and personal devices—without requiring per-device MFA configuration.
How does FFIEC examine VDI deployments during IT examinations?
FFIEC examiners evaluate VDI deployments under the access controls, remote access security, and third-party risk management sections of the IT Handbook. Examiners will request access control policies, sample session logs, MFA configuration documentation, and vendor risk assessment documentation for OCI (SOC 2 Type II reports, DPA copies). Institutions should prepare these materials as part of their examination readiness package, typically requiring 2-3 weeks of IT staff time.
Is OCI FedRAMP authorized for regulated banking workloads?
OCI holds FedRAMP High authorization for its US Government cloud regions (Ashburn, VA and Chicago, IL). Commercial OCI regions are used by numerous federally regulated financial institutions and are covered by OCI’s SOC 2 Type II and ISO 27001 certifications, satisfying OCC 2023 third-party risk management guidance requirements. For institutions with government banking relationships, FedRAMP regions are recommended.
What does the OCC 2023 third-party risk management guidance require for a cloud deployment?
The guidance requires due diligence on cloud vendors (financial condition, operational resilience, data handling, security), contracts with specific provisions (data access, audit rights, exit strategy, incident notification), and ongoing monitoring. OCI provides SOC 2 Type II and SOC 1 Type II reports under NDA, and its standard DPA includes required contractual provisions. Typical timeline for a formal vendor risk assessment: 4-6 weeks.
How does VDI reduce the scope of our annual PCI DSS penetration test?
In a VDI environment, cardholder data processing occurs on centralized OCI session hosts, not on endpoint devices. Endpoints receive only an encoded screen stream with no cardholder data stored locally. The PCI DSS pentest scope is reduced to the OCI VCN, the Thinfinity Gateway, and the session host pool—a much smaller, more defensible scope with typical cost reductions of 30-40% compared to thick-client pentesting.
Can Thinfinity on OCI work with Jack Henry's hosted SilverLake environment?
Yes. Thinfinity Workspace session hosts in OCI connect to Jack Henry’s hosted SilverLake environment over the bank’s existing private network interconnect. SilverLake’s Windows client application runs on the OCI session hosts as a standard installation, with zero changes to SilverLake configuration. The same connectivity pattern applies to Fiserv Premier/Precision/Signature and FIS IBS hosted environments.
What happens if the OCI connection to a branch fails? Is there failover?
Thinfinity supports redundant Gateway deployments across multiple OCI availability domains and regions. For branch offices, institutions typically maintain one fallback physical workstation per branch connected to a separate network path. For institutions with high availability requirements, multi-region deployment in Ashburn and Chicago provides automatic failover with less than 1 minute RTO.
How does Thinfinity Workspace handle high-latency or unstable connections (rural branches)?
Thinfinity uses adaptive protocol compression that adjusts encoding based on connection quality. At 20 Mbps: excellent user experience with 50-60ms latency tolerance. At 5 Mbps: acceptable experience with adaptive compression suitable for rural branches. For branches with challenging network conditions, bandwidth optimization and packet loss recovery are configured per location.
What are the typical monthly costs for Thinfinity on OCI for a 300-user community bank?
Typical monthly costs are: OCI compute $8,000-12,000/month; Thinfinity licensing $3,000-4,000/month; OCI storage $1,500-2,000/month; network/connectivity $500-1,000/month. Total: approximately $13,000-19,000/month. Compared to equivalent thick-client infrastructure, this typically represents a 20-30% cost reduction when factoring in eliminated endpoint hardware replacement cycles, reduced helpdesk overhead, and reduced pentesting scope.
Can we migrate existing user profiles and data to the OCI VDI environment?
Yes. Thinfinity supports FSLogix Profile Containers that store user documents, desktop settings, and application configurations in OCI File Storage. Migration tools allow bulk import from existing virtual desktop environments or physical workstations. Timeline: 2-3 weeks for a 300-user migration, with per-user validation during pilot phase.
Conclusion: Compliance-Driven Modernization for US Banking
The regulatory landscape for US financial institutions has fundamentally shifted from principles-based compliance to prescriptive control requirements. The GLBA Safeguards Rule 2023, PCI DSS v4.0, OCC third-party risk guidance, and FFIEC examination procedures all demand specific technical controls that VDI architecture directly satisfies. For community and regional banks, Virtual Desktop Infrastructure on Oracle Cloud Infrastructure offers a structural compliance advantage: centralized security controls, reduced examination scope, and demonstrated alignment with every major regulatory framework.
Thinfinity Workspace on OCI is purpose-built for US banking compliance requirements. It centralizes MFA enforcement, eliminates endpoint data storage, provides complete session logging for examination readiness, and simplifies GLBA compliance documentation. The deployment model is designed for lean IT teams, with full rollout in 12-14 weeks and ongoing operational overhead that fits within typical 2-3 person bank IT staffs.
For institutions evaluating VDI as a modernization and risk-reduction strategy, Thinfinity on OCI eliminates architectural uncertainty. It is built for banking compliance, scaled for community bank budgets, and proven in production deployments across the US financial services sector.
See Thinfinity for US Banking
Request a 30-minute walkthrough of Thinfinity on OCI for US financial institutions. We’ll cover GLBA Safeguards Rule alignment, FFIEC examination evidence, core banking application compatibility, and show a live demo of access controls and session recording. Get your questions answered by Thinfinity’s banking compliance experts.


