In this quick tutorial, we will show how to properly configure Okta SAML for Thinfinity Workspace v6.5 and Thinfinity VirtualUI v3.1
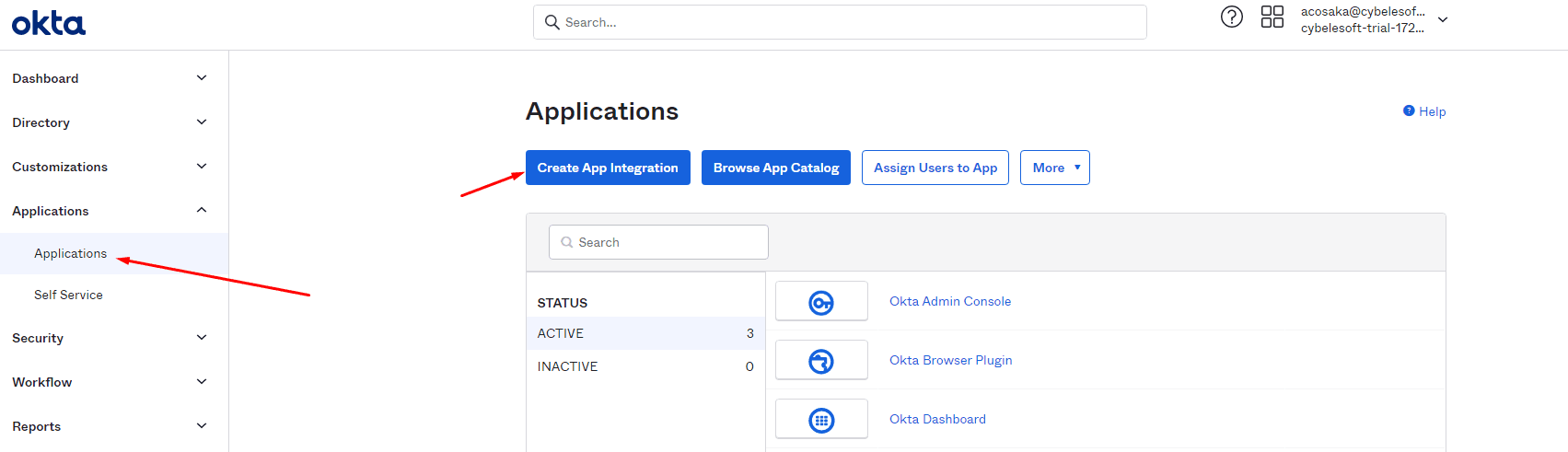
1) Navigate to your Okta space (or start a free trial to test this feature), go to the Applications tab, and create a new application using the “Create New App” button:
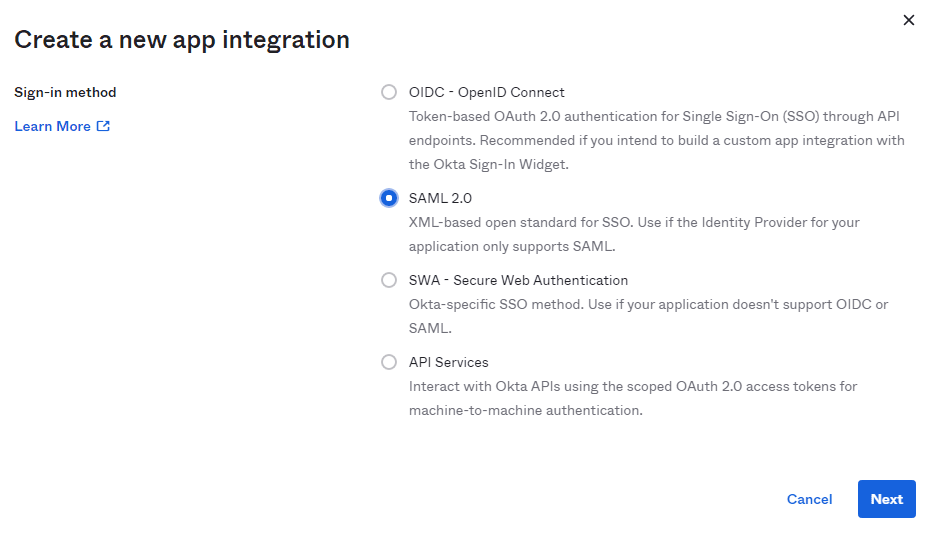
2) Select OpenID Connect as the Authentication Method:
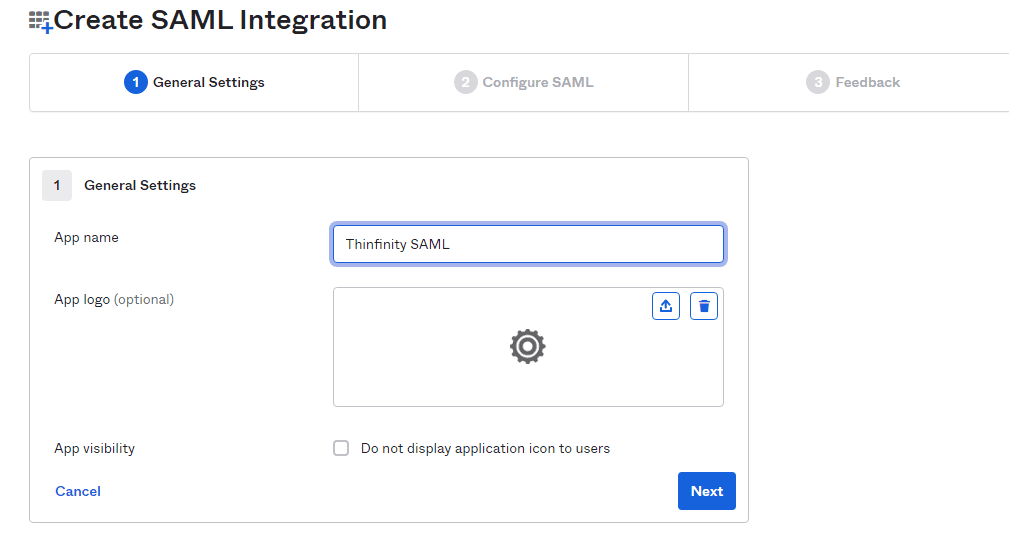
3) Assign a name to the application.
4) Configure the “Single sign-on URL” and “Audience URI”.
-
- The “Single Sign-on URL” address should be the following:
-
- https://[MyThinfinityWebSite]/SAMLAssertionConsumerService
-
- The Audience URI should be the URI used to connect to Thinfinity:
- https://[MyThinfinityWebSite]/
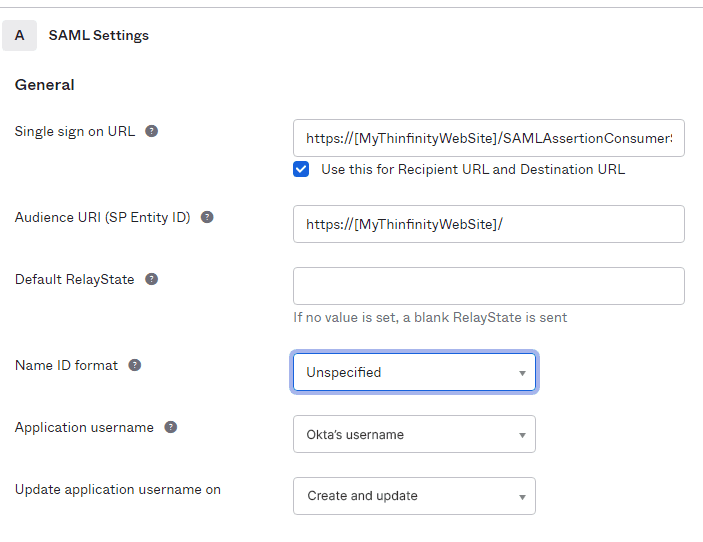
Leave everything else by default and click Next below.
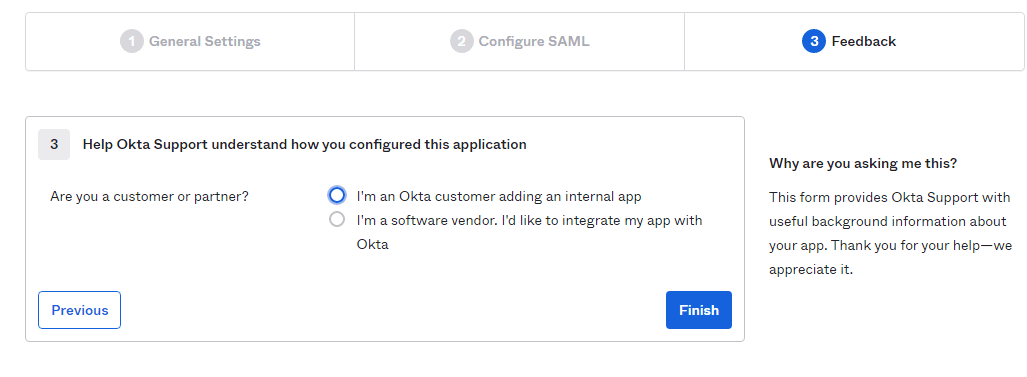
5) Choose the Feedback options that apply to your application:
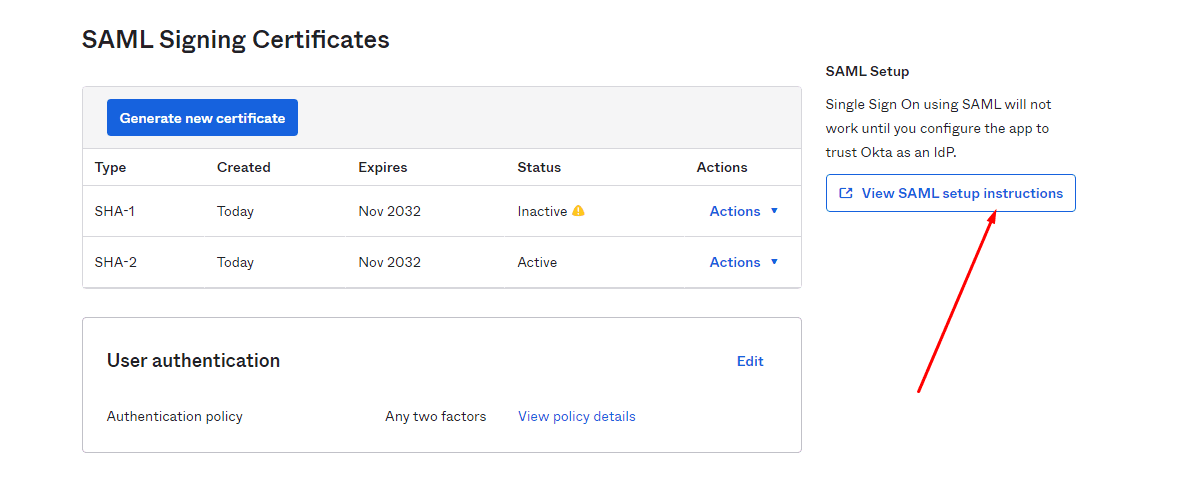
6) Now that the application is created, it should redirect you to the “Settings” window. Scroll to the bottom and click on “View SAML setup instructions”
In here you will get the “Identity Provider Single Sign-on URL”, the Identity Provider Issuer, and the Certificate provided by Okta.
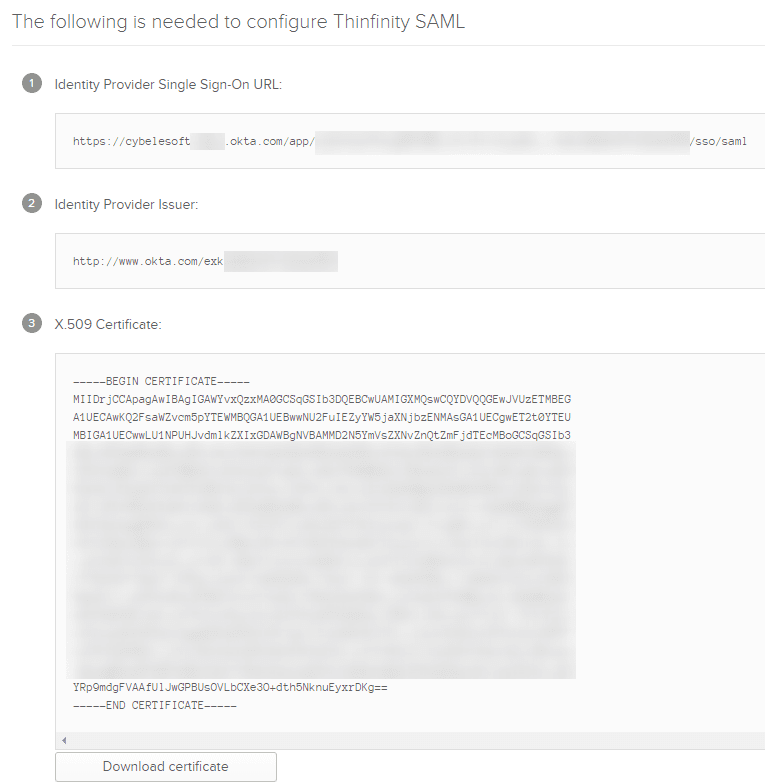
You will need to copy the first two text fields for the next step, we suggest you paste them in a text file for now.
Also, click the “Download certificate” button and save the resulting file in any folder inside the VirtualUI server.
We’re going to use the route “C:\temp\okta.cert” as an example.
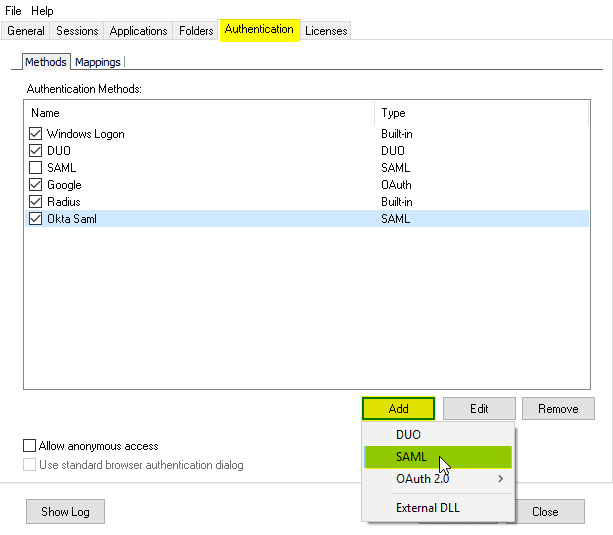
7) Now, open the Thinfinity Remote Desktop Server Manager or Thinfinity VirtualUI Server manager, navigate to the “Authentication” tab, press the “Add” option and click on “SAML”:
8) In here, you will have to add the different values provided by Okta in order to enable SAML:
- Service Identifier = Audience URI (SP Entity ID)
- Service Certificate File = Your certificate’s file. (This certificate is created after this step, this is where we give it a name)
- Service Certificate Password = Password of your choice for the certificate created above
- Identification Entity ID = Identity Provider Issuer
- Single Sign-On Service URL = Identity Provider Single Sign-On URL
- Sign-Out URL = This value is optional.
- Partner Certificate File = X.509 Certificate provided by Okta.
Below you’ll find an example on how it should look like :
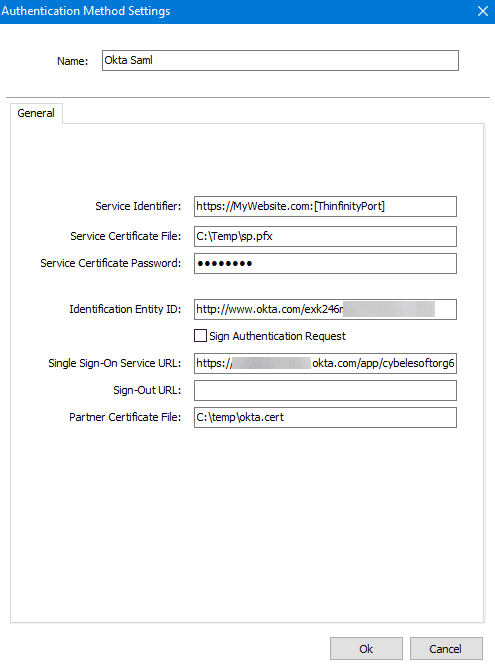
After you finish adding all those values, press “Ok”.
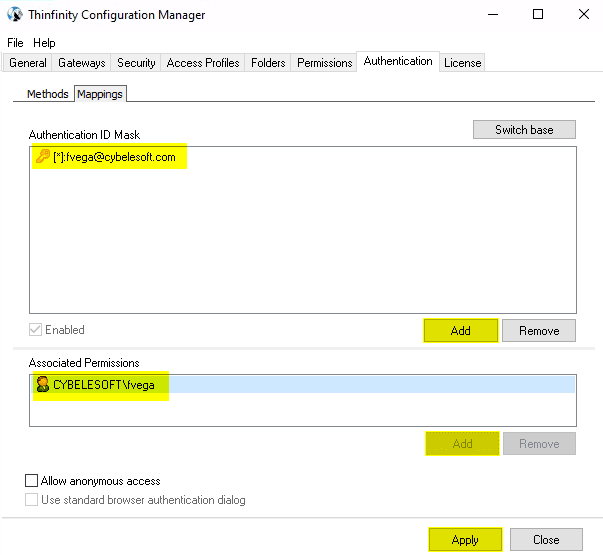
10) Click on the “Mappings” tab and then press “Add” under the Authentication ID Mask.
Add the email address of the Okta user you want to validate and press “Ok”.
Then, under the “Associated Permissions” field, press on the “Add” button and search for the Active Directory User.
Thinfinity Remote Workspace:
Thinfinity VirtualUI:
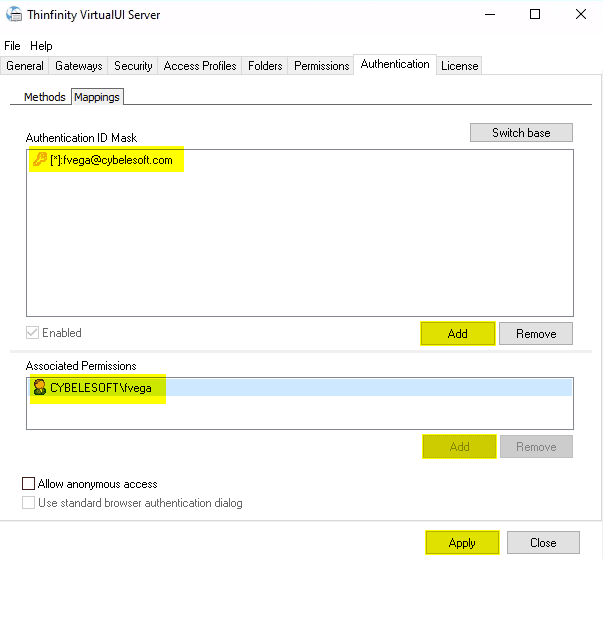
11) After you add the appropriate mappings, click on the “Apply” button.
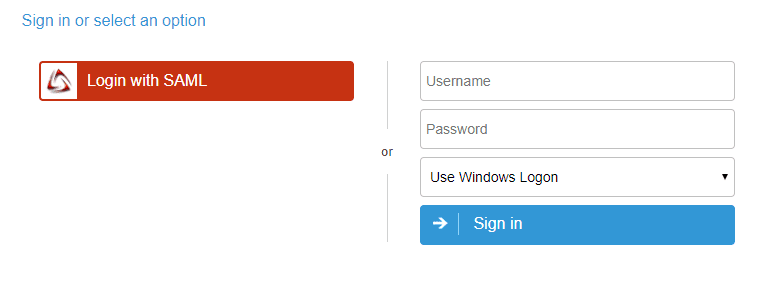
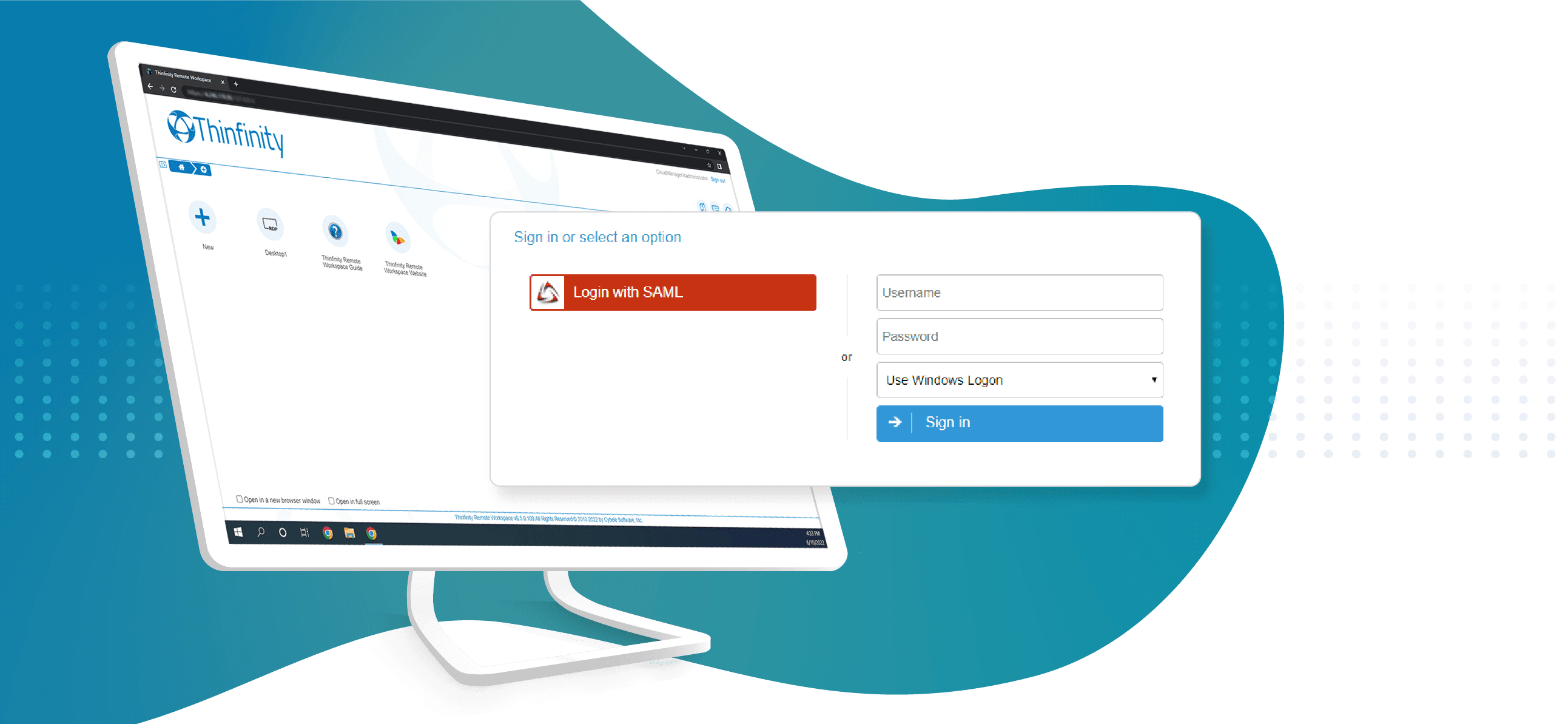
12) Navigate to the Thinfinity’s landing page, and you should see the “Login With SAML” option listed as an Authentication Method.
Quick Tip: Learn how to configure Duo 2FA and how to configure Okta with OpenID Connect as the Authentication Method.


1 Comments
Hii
Thank you for the informative article. This is a high-level overview, and the actual steps might vary depending on the specifics of the service provider and Okta’s interface. Here is sharing some Data Science training with Python information may be its helpful to you.
Data Science training with Python