Keycloak OAuth 2.0 authentication with Thinfinity represents a powerful convergence of enterprise identity management and secure virtual desktop infrastructure, enabling organizations to implement zero-trust authentication frameworks while maintaining seamless user access to remote desktops and applications. This integration leverages modern, token-based authentication protocols—specifically OAuth 2.0 and OpenID Connect—to eliminate password-sharing vulnerabilities and establish cryptographically secure, delegated access to virtualized resources. By combining Keycloak’s centralized identity and access management capabilities with Thinfinity’s reverse-gateway VDI technology, organizations gain granular control over user provisioning, session management, and compliance enforcement while dramatically reducing attack surface exposure and operational complexity.
Understanding Keycloak: The Foundation of Modern Identity Management
Keycloak is an open-source identity and access management (IAM) platform developed by Red Hat that serves as a centralized authentication and authorization server for web applications, mobile apps, and RESTful services. Rather than implementing authentication logic in every individual application, organizations deploy Keycloak as a dedicated identity provider (IdP) that all applications trust for user verification and credential validation. This architectural approach fundamentally transforms how enterprises manage identity at scale, shifting from distributed, fragmented security implementations to a cohesive, policy-driven identity fabric.
At its core, Keycloak provides Single Sign-On (SSO) capabilities that allow users to authenticate once and seamlessly access multiple applications without re-entering credentials. The platform supports modern authentication protocols including OAuth 2.0, OpenID Connect (OIDC), and SAML 2.0, ensuring compatibility with contemporary security standards and industry best practices. Keycloak’s architecture revolves around the concept of “realms”—isolated security domains that contain users, roles, clients (applications), and authentication policies. This multi-tenancy design allows organizations to manage authentication for diverse business units or customer segments within a single Keycloak deployment.
The importance of Keycloak in modern VDI deployments cannot be overstated. Organizations face escalating authentication challenges in remote-access scenarios, where users may connect from untrusted networks, unmanaged devices, or geographically distributed locations. Traditional username/password authentication creates substantial security liabilities: credentials are exposed during transit, stored in multiple systems, and vulnerable to phishing attacks. Keycloak addresses these challenges by implementing token-based authentication frameworks that never expose user credentials to resource applications—the tokens themselves become the sole authorization mechanism.
OAuth 2.0 and OpenID Connect: Protocols Powering Secure Delegation
OAuth 2.0 is an authorization framework that allows users to grant limited, delegated access to their resources without exposing credentials to the requesting application. Unlike traditional authentication where a user shares their password with an application, OAuth 2.0 introduces an authorization server (in this case, Keycloak) that handles credential verification and issues time-limited access tokens. The critical security distinction is that applications never see the user’s password—they only receive a token that grants access to specific resources for a defined duration.
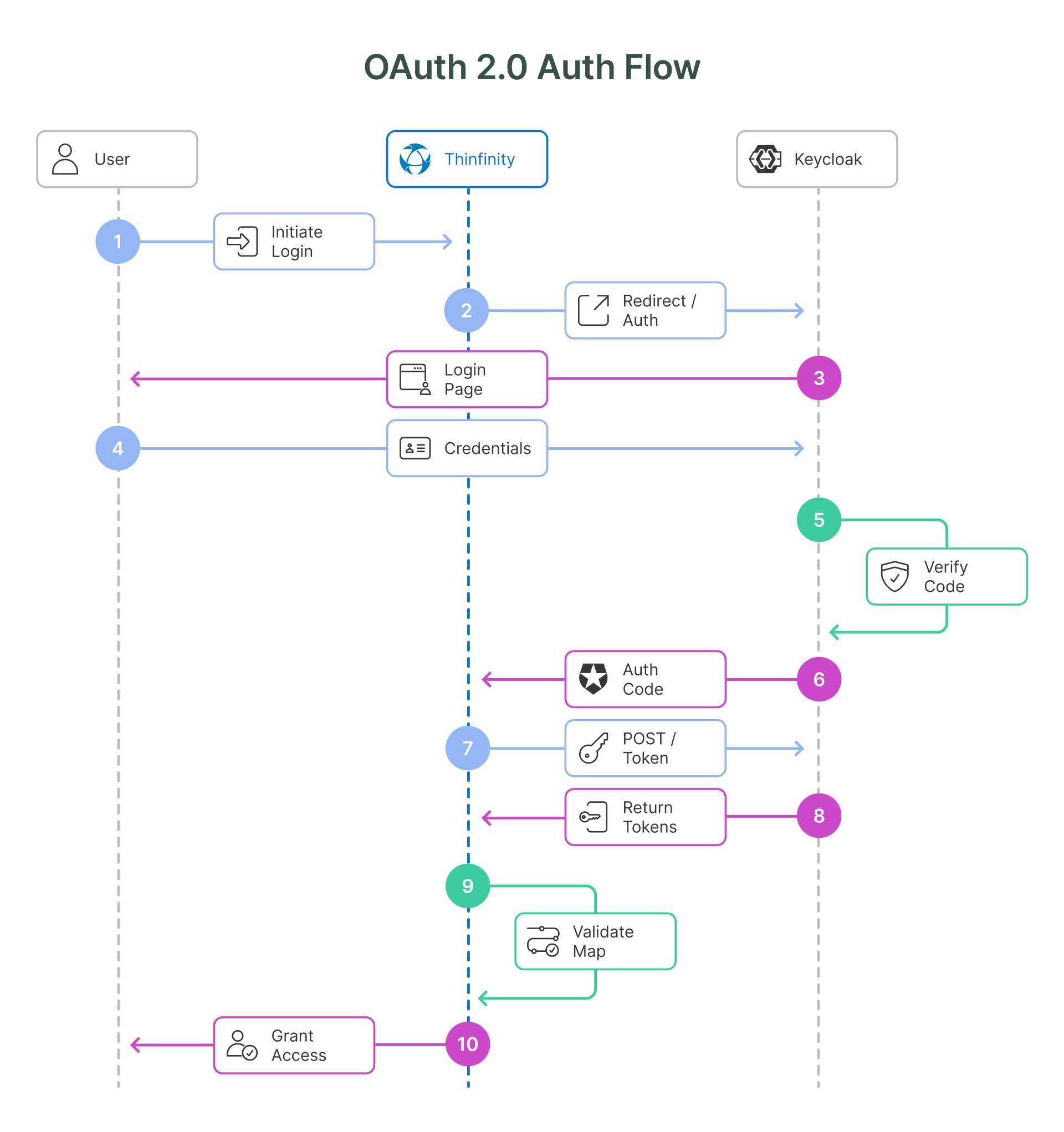
The OAuth 2.0 Authorization Code Flow, which Keycloak uses with Thinfinity, operates through a precisely choreographed sequence of steps. When a user attempts to access a Thinfinity virtual desktop, they are redirected to Keycloak’s authorization endpoint rather than providing credentials directly to Thinfinity. Keycloak authenticates the user, presents consent screens listing the permissions (scopes) the application is requesting, and—upon user approval—issues a short-lived authorization code. Thinfinity’s backend then exchanges this authorization code for an access token through a secure server-to-server communication channel, preventing interception attacks that might target client-side token exchanges.
OpenID Connect (OIDC) extends OAuth 2.0 by adding an authentication layer specifically designed for identity verification. While OAuth 2.0 focuses on authorization (what resources can a user access), OIDC adds authentication (verifying who the user is). In the OAuth 2.0 + OIDC model that Keycloak implements, the authorization server returns not just an access token but also an ID token—a JSON Web Token (JWT) containing cryptographically signed claims about the user’s identity. The ID token includes information such as the user’s unique identifier, email address, name, and authentication context, all protected by digital signatures that prevent tampering.
JWT (JSON Web Tokens) form the cryptographic foundation of both access and ID tokens in the OIDC flow. A JWT consists of three base64-encoded components: a header (describing the token type and signing algorithm), a payload (containing the claims), and a signature (proving the token came from the trusted authorization server and hasn’t been modified). When Thinfinity receives a JWT from Keycloak, it can validate the signature using Keycloak’s public key, confirming that the token was genuinely issued by the identity provider and hasn’t been altered.
Key Security Technologies and Protocols in the Keycloak-Thinfinity Integration
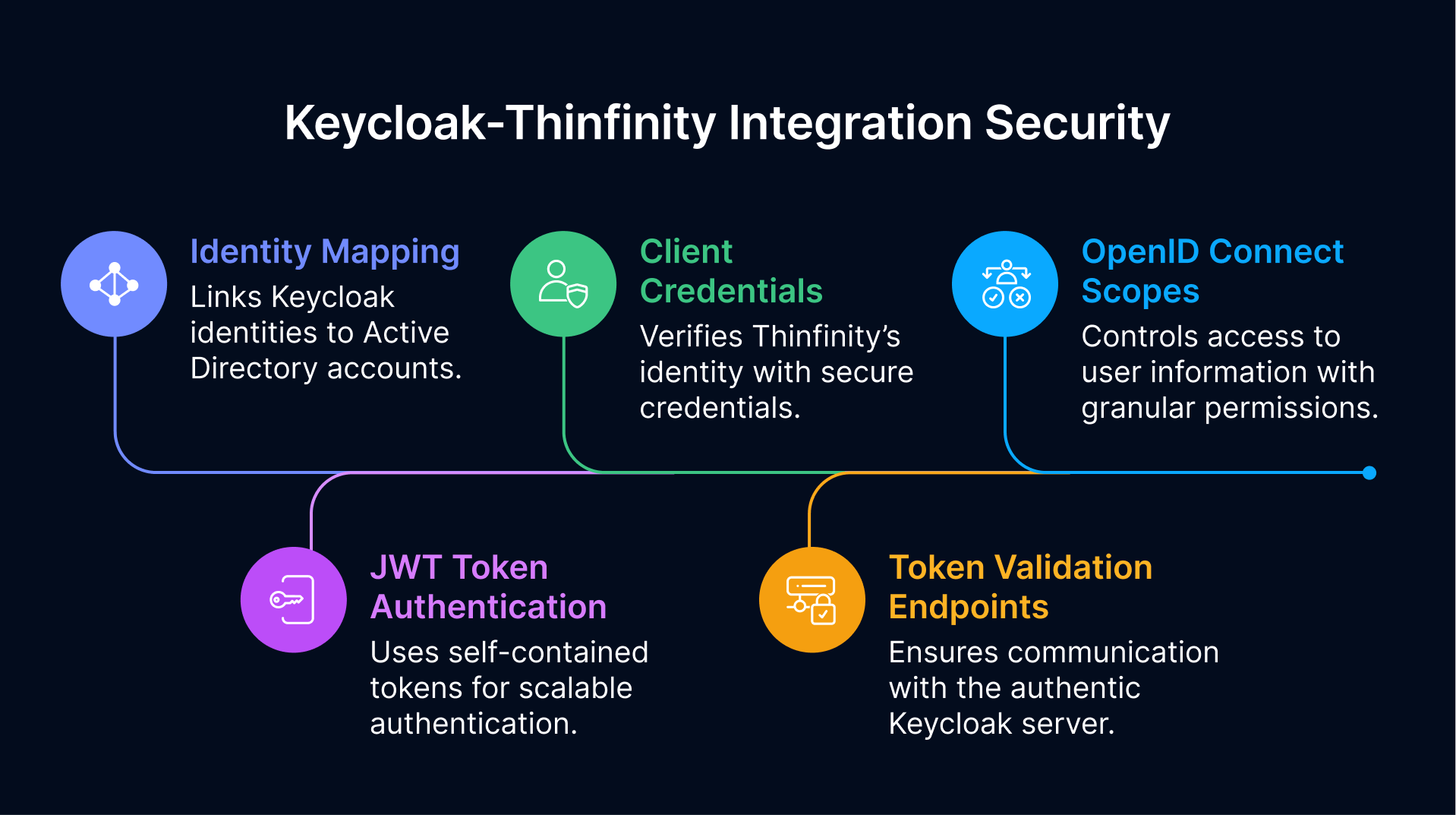
The integration between Keycloak and Thinfinity leverages several complementary security technologies that work in concert to protect virtual desktop access:
JWT Token-Based Authentication: The tutorial configuration demonstrates that Keycloak generates JWT tokens containing the user’s authentication context and identity claims. Thinfinity validates these tokens using Keycloak’s public keys, ensuring tokens originated from the legitimate identity provider. Unlike session cookies that require server-side storage and comparison, JWTs are self-contained—the token itself contains all information needed for validation, making them highly scalable across distributed infrastructure. The tutorial specifies that user information is extracted from the token itself (rather than fetching it from an external URL), enabling stateless, efficient authentication validation.
OpenID Connect Scope Framework: The configuration demonstrates the use of OpenID Connect scopes, particularly the openid scope which signals the use of OIDC for authentication rather than plain OAuth 2.0 authorization. Additional scopes like email, profile, address, and phone provide granular control over what user information Thinfinity can access. This implements the principle of least privilege—Thinfinity requests only the user attributes necessary for its operations, and Keycloak only issues tokens containing those specific claims. This scoping mechanism reduces the blast radius if a token is compromised; an attacker cannot use the token to access user information beyond the authorized scopes.
Client Credentials and Authentication Flow Configuration: The tutorial specifies that Thinfinity must be registered as an OpenID Connect client in Keycloak with Client Authentication enabled and using the “Standard flow + Direct access grants” authentication flow. Client Authentication means Thinfinity must prove its identity to Keycloak when exchanging authorization codes for tokens by providing a Client ID and Client Secret—credentials stored securely on Thinfinity’s server and never exposed to users. This ensures that only legitimate instances of Thinfinity can exchange authorization codes for tokens; a malicious actor cannot intercept an authorization code and exchange it for tokens without the Client Secret.
Token Validation Endpoints: The configuration requires three critical Keycloak endpoints:
- The authorization endpoint (where users authenticate and grant consent)
- The token endpoint (where authorization codes are exchanged for tokens)
- The end_session endpoint (for logout operations)
These endpoints are obtained from Keycloak’s OpenID Endpoint Configuration, ensuring Thinfinity communicates with the authentic Keycloak server and not a spoofed identity provider.
Identity Mapping and User Federation: Perhaps the most critical security feature for VDI deployments is identity mapping—the mechanism through which Keycloak-verified identities are linked to Active Directory user accounts that control actual resource access. The tutorial demonstrates this process: after Keycloak authenticates a user, Thinfinity’s identity mapping rules evaluate the Keycloak user identifier against patterns and link that user to internal AD objects. For example, a pattern like myKeycloakUser (the Keycloak user) is mapped to myWindowsUser (the local or domain AD user). This mapping is critical because it bridges the gap between the centralized, internet-facing identity provider (Keycloak) and the Windows infrastructure that actually governs file access, application permissions, and desktop configurations.
Cryptographic Security and Transport Layer Protection
The Keycloak-Thinfinity integration operates over HTTPS with TLS 1.3 encryption, as specified in the Thinfinity documentation noting “secure reverse connections over SSL with TLS 1.3 encryption”. This protects authorization codes, access tokens, and client secrets in transit from interception. The cryptographic protections include:
- Token Signing: All JWTs from Keycloak are digitally signed using RS256 (RSA with SHA-256), allowing Thinfinity to verify token authenticity using Keycloak’s public key
- Secure Code Exchange: The authorization code exchanged between Keycloak and Thinfinity during the OAuth flow is short-lived (typically 10 minutes) and single-use, preventing replay attacks even if intercepted
- State Parameter Validation: The OAuth 2.0 flow includes a state parameter that prevents cross-site request forgery (CSRF) attacks by ensuring that authorization responses match the authorization requests that triggered them
VDI-Specific Benefits and Security Enhancements
Integrating Keycloak OAuth 2.0 authentication with Thinfinity VDI delivers several strategic security and operational advantages specific to virtual desktop infrastructure:
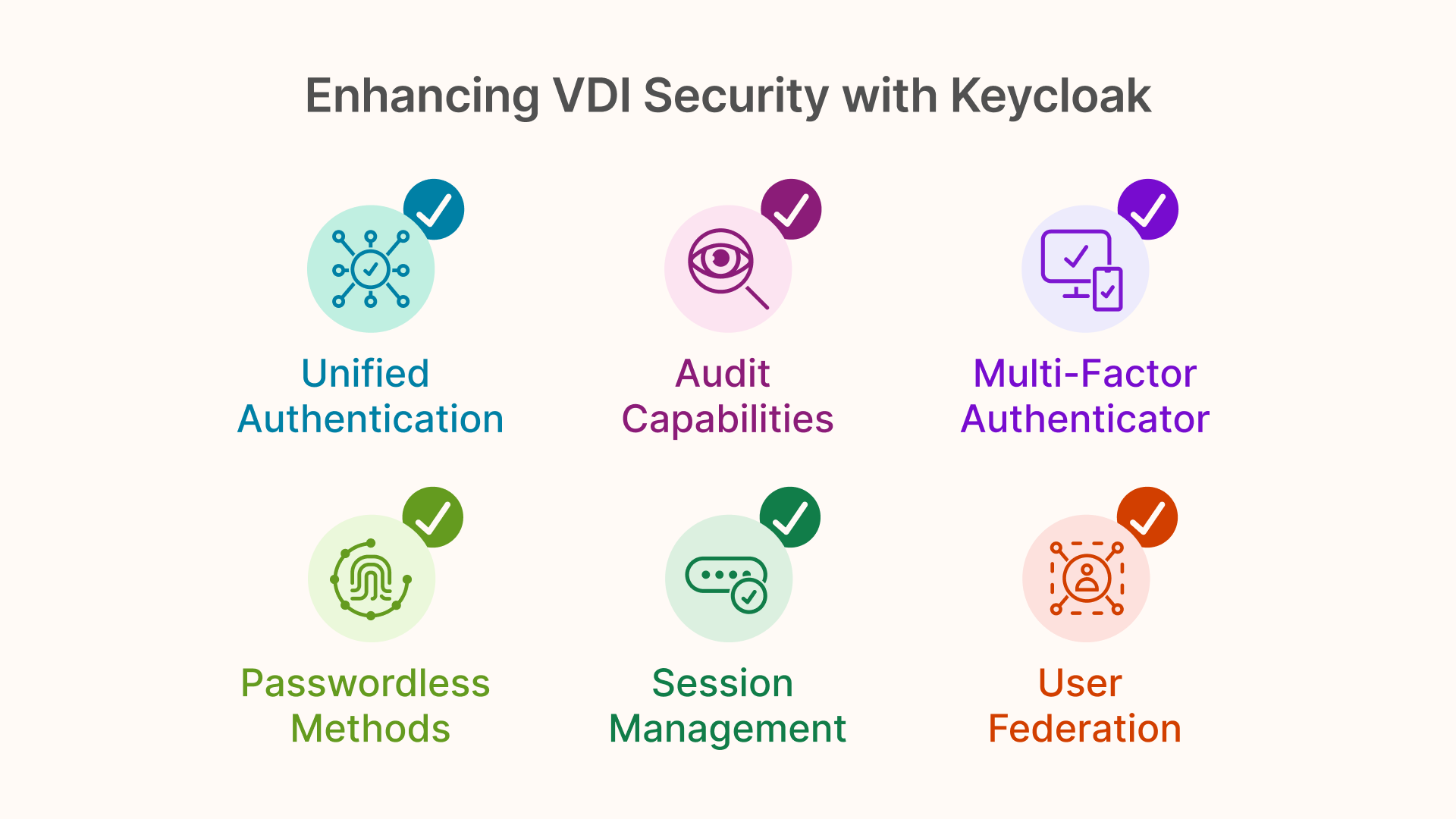
Centralized Authentication Policy Enforcement: Rather than embedding authentication logic in each virtualized application or desktop gateway, organizations enforce authentication policies in a single, auditable location—Keycloak. Multi-factor authentication (MFA) requirements, password policies, session timeouts, and adaptive authentication rules can be configured once and apply immediately to all Thinfinity-connected users. This eliminates configuration drift and ensures that every access attempt adheres to the organization’s current security baseline.
Session Management and Zero-Trust Principles: VDI access inherently requires robust session management since users are accessing sensitive enterprise resources from untrusted networks. Keycloak issues short-lived access tokens (typically with 5-15 minute lifespans) that must be continuously refreshed, forcing re-validation of user identity and authorization status. If a user’s permissions change—for example, they transfer to a different department and their AD group memberships change—those changes are reflected on the next token refresh rather than requiring session termination and re-authentication. This implements the zero-trust principle of continuous verification rather than one-time trust establishment.
Multi-Factor Authentication Support: Keycloak natively supports multiple MFA methods including TOTP (Time-based One-Time Password), WebAuthn, and FIDO2 hardware keys. When configured for MFA, users cannot access Thinfinity virtual desktops without successfully completing the second factor, even if their password is compromised. The MFA interaction occurs entirely within Keycloak before the authorization code is returned, meaning Thinfinity never processes users who haven’t passed MFA verification.
User Federation and Identity Brokering: Keycloak can integrate with external user directories including Active Directory, LDAP, and cloud identity providers. Rather than managing separate user databases, organizations can configure Keycloak to federate with their existing Active Directory deployment. This ensures that user creation, modification, and deletion in Active Directory automatically propagate to Keycloak without manual intervention. The tutorial’s identity mapping feature then links these federated identities to specific Active Directory groups and organizational units (OUs) that control VDI resource access.
Audit and Compliance Capabilities: Keycloak maintains comprehensive authentication logs including successful logins, failed attempts, MFA challenges, and token issuance events. These logs can be streamed to security information and event management (SIEM) systems for real-time anomaly detection. For regulated industries, this audit trail demonstrates compliance with requirements like those in SOX, HIPAA, or PCI-DSS that mandate detailed access logging and review.
Passwordless Authentication Path: While our first integration focuses on OAuth 2.0 token exchange, Keycloak supports passwordless authentication methods including FIDO2 biometric authentication and Windows Hello integration. Organizations can gradually transition from password-based authentication to phishing-resistant passwordless methods without architectural changes—Keycloak abstracts the authentication method from the downstream application (Thinfinity), meaning Thinfinity can support passwordless access simply by deploying the new authentication method in Keycloak.
Implementation Architecture and Configuration Workflow
A successful deployment relies on a specific sequence designed to ensure secure token exchange and accurate user mapping between your identity provider and the workspace. To learn in detail how to configure Keycloak integration, explore our deep dive into the Implementation Architecture and Configuration Workflow.
Conclusion
The integration of Keycloak with Thinfinity Workspace represents a strategic shift from traditional perimeter-based defense to a robust, identity-centric security posture. By decoupling authentication from the application layer, organizations effectively modernize their VDI infrastructure without the need to overhaul their existing Active Directory environments.
This architecture delivers a “best-of-breed” solution: Keycloak handles the complexities of identity verification, MFA, and compliance, while Thinfinity focuses on high-performance desktop and application delivery. The result is a Zero Trust environment where credentials are never exposed to the endpoint, access is granted via cryptographically signed tokens, and security policies are enforced centrally. For enterprises facing the dual challenges of remote work scalability and escalating cyber threats, this integration offers a path to secure, seamless, and compliant virtualization.
Frequently Asked Questions (FAQ)
Does Thinfinity store or see the user's password when using Keycloak?
No. One of the primary security benefits of this integration is that it utilizes the OAuth 2.0 protocol. The user enters their credentials directly into Keycloak’s secure interface. Keycloak then issues an encrypted access token (JWT) to Thinfinity. Thinfinity validates the token to grant access, meaning the user’s actual password never passes through or resides on the Thinfinity server.
How does this integration support Zero Trust principles?
It supports Zero Trust through “continuous verification.” Unlike traditional setups that might trust a user for the duration of a long session, Keycloak issues short-lived access tokens (typically 5–15 minutes).
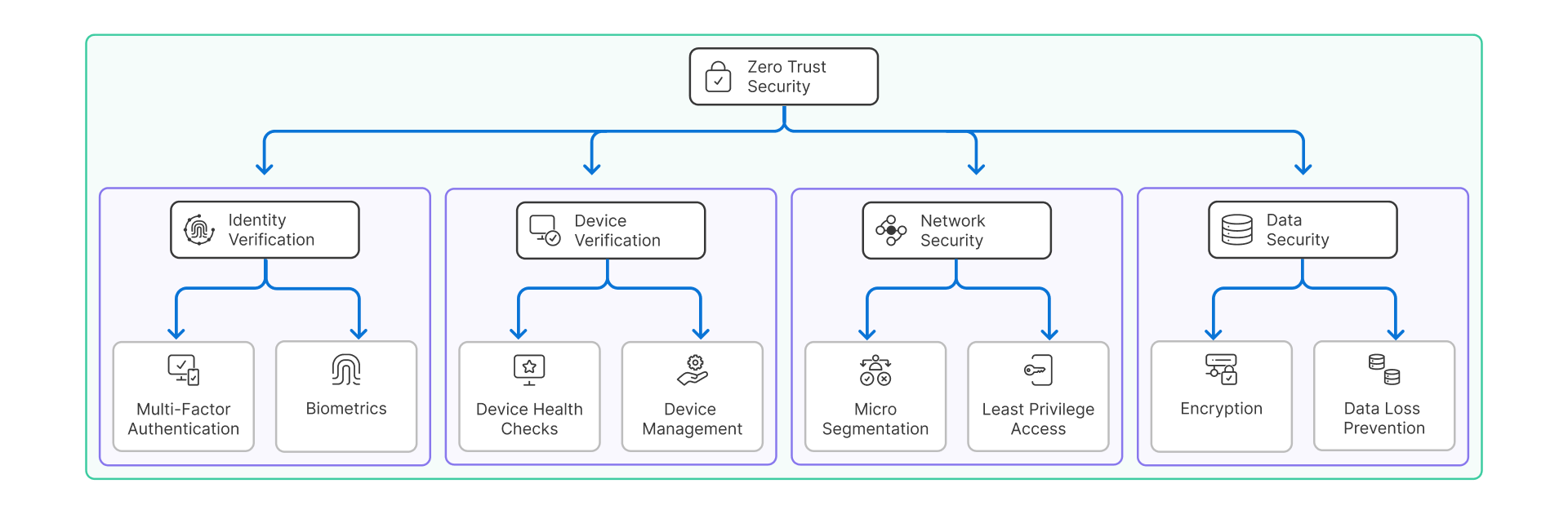
These tokens must be continuously refreshed. If a user’s permissions are revoked or their risk profile changes in Keycloak, access can be denied at the next token refresh interval, rather than waiting for the user to log out.
Can I use Multi-Factor Authentication (MFA) with this setup?
How does Thinfinity know which Windows user to log in as if it only receives a token?
This is handled through Identity Mapping. When Keycloak sends the ID Token, Thinfinity reads the user claims (such as email or username) and matches them against pre-configured rules. It links the federated identity from Keycloak (e.g., [email protected]) to the internal Active Directory user (e.g., DOMAIN\User), ensuring the user gets the correct file permissions and desktop profile.
What happens if I have users in different departments or business units?
Keycloak uses a concept called Realms and Scopes. You can manage different user groups within Keycloak and use OpenID Connect scopes (like profile, email, groups) to pass specific user attributes to Thinfinity. This allows Thinfinity to assign different desktop pools or application sets based on the user’s role defined in Keycloak.
Is the communication between Thinfinity and Keycloak secure?
Yes. The integration requires HTTPS with TLS 1.3 encryption for all traffic. Furthermore, the JSON Web Tokens (JWTs) passed between the systems are digitally signed using RS256 (RSA signature with SHA-256). Thinfinity uses Keycloak’s public key to verify that the token is authentic and has not been tampered with during transit.