Manufacturing overtook financial services and healthcare to become the single most-attacked industry in the world — and it has held that position for three consecutive years. If you are a CISO or CIO at a manufacturing company and you are still relying on VPNs, jump servers, and perimeter firewalls to protect your operational technology, you are operating with a security architecture that was designed for a different era.
This article explains why manufacturing is under such intense attack, what makes traditional defenses insufficient, and how a Zero Trust approach provides a practical, achievable path to protecting both your IT infrastructure and your shop floor — without halting production.
Manufacturing: The Most-Targeted Sector in the World
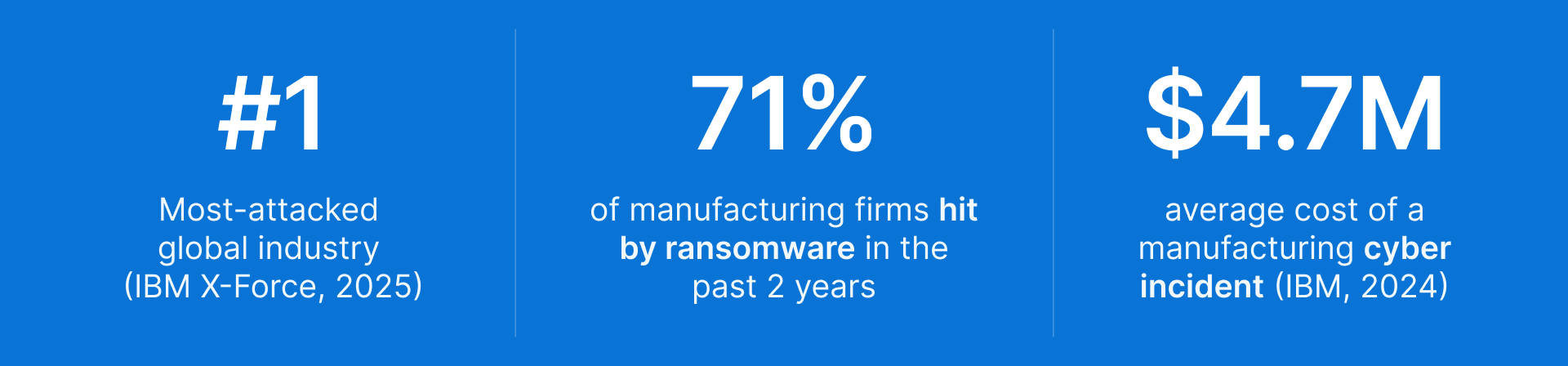
IBM’s X-Force Threat Intelligence Index has ranked manufacturing as the top targeted industry for three years running. The 2025 edition confirmed the trend: manufacturing accounted for more cyberattacks than any other sector globally, surpassing finance, healthcare, and energy.
The numbers are stark — but understanding why manufacturing is targeted is what makes a strategic response possible.
Why Attackers Specifically Target Manufacturing Environments
1. Legacy OT Systems Were Never Designed With Security in Mind
The vast majority of operational technology in the world — PLCs, SCADA systems, HMI panels, DCS controllers — was engineered for reliability, not security. Many of these systems were installed 15 to 25 years ago, run on embedded operating systems that cannot be patched, and communicate over industrial protocols (Modbus, DNP3, OPC-UA) that have no built-in authentication.
Attackers know this. Once they reach the OT network, they encounter systems that are essentially open by design.
2. IT/OT Convergence Has Created a Massive New Attack Surface
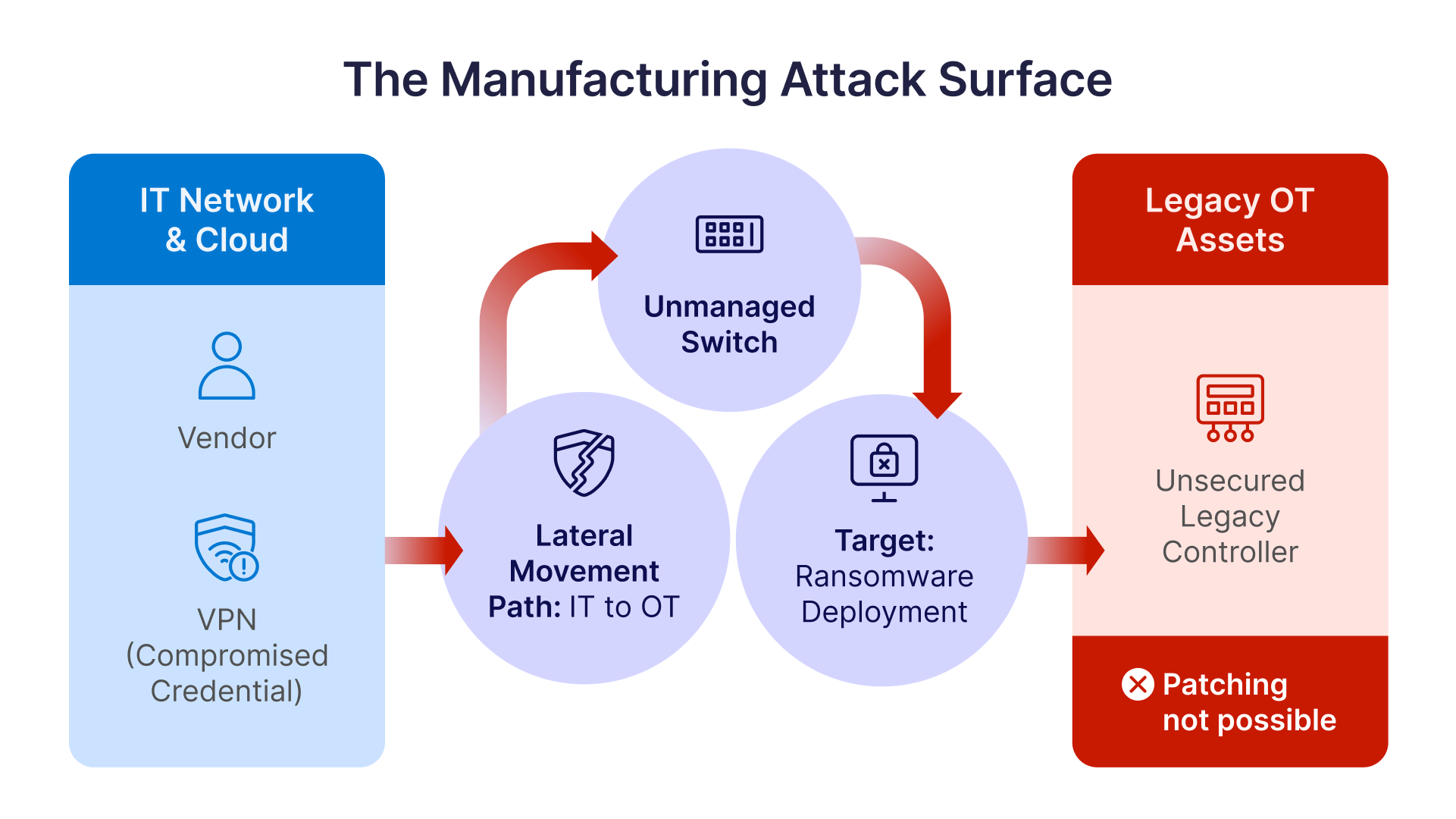
The Industry 4.0 revolution — IIoT sensors, cloud-connected machines, remote diagnostics, digital twins — has been transformative for productivity. It has also connected plant floor systems to corporate IT networks and, increasingly, to the public internet. Every new connection between IT and OT is a potential lateral movement path for an attacker who has compromised a corporate credential or a vendor’s laptop.
The Purdue model that historically separated OT from IT has been eroded in most manufacturing environments, often without a compensating security architecture to replace it.
3. Third-Party Vendor Access Is an Uncontrolled Open Door
Modern manufacturing depends on OEM vendors, systems integrators, and equipment suppliers who need remote access to PLCs and machines for maintenance, troubleshooting, and firmware updates. In most plants, this access is provided via a shared VPN account, a TeamViewer link, or — in the worst cases — an always-on remote desktop port exposed to the internet.
The 2021 Oldsmar water treatment facility attack entered through a remote access tool. The 2023 Clorox attack used compromised vendor credentials. The pattern repeats because the underlying architecture — broad, always-on, minimally authenticated vendor access — remains unchanged in most industrial environments.
4. Downtime Cost Makes Manufacturers Ideal Ransomware Victims
Manufacturing has an Achilles heel that most other industries do not: every minute of production downtime has a direct, quantifiable dollar cost. An automotive assembly plant losing one hour of production may lose hundreds of thousands of dollars. A food processing facility facing a multi-day shutdown risks product spoilage and contract penalties on top of recovery costs.
Ransomware operators know that manufacturers are far more likely to pay quickly than a law firm or a retailer. Production pressure is the lever — and attackers pull it deliberately.
The Regulatory Pressure Is Mounting — and Non-Compliance Is No Longer an Option
Cybersecurity in manufacturing is no longer just an operational risk — it is a legal and contractual liability. Three major frameworks are converging to make Zero Trust adoption a compliance requirement:
- NIS2 Directive (EU): In force since October 2024, NIS2 extends mandatory cybersecurity obligations to manufacturers of critical products. Medium and large manufacturers must implement risk management measures, incident reporting, and supply chain security controls — or face fines of up to €10 million or 2% of global annual turnover.
- IEC 62443: The international standard for industrial cybersecurity defines a security level framework (SL-1 to SL-4) for ICS/SCADA environments. An increasing number of enterprise customers and government contracts now require IEC 62443 compliance from manufacturing suppliers.
- NIST CSF 2.0: The updated framework released in 2024 expands its scope to include OT environments explicitly and adds a Govern function that makes cybersecurity a board-level accountability. Many US federal contractors in manufacturing are subject to it.
Key Insight for Decision-Makers
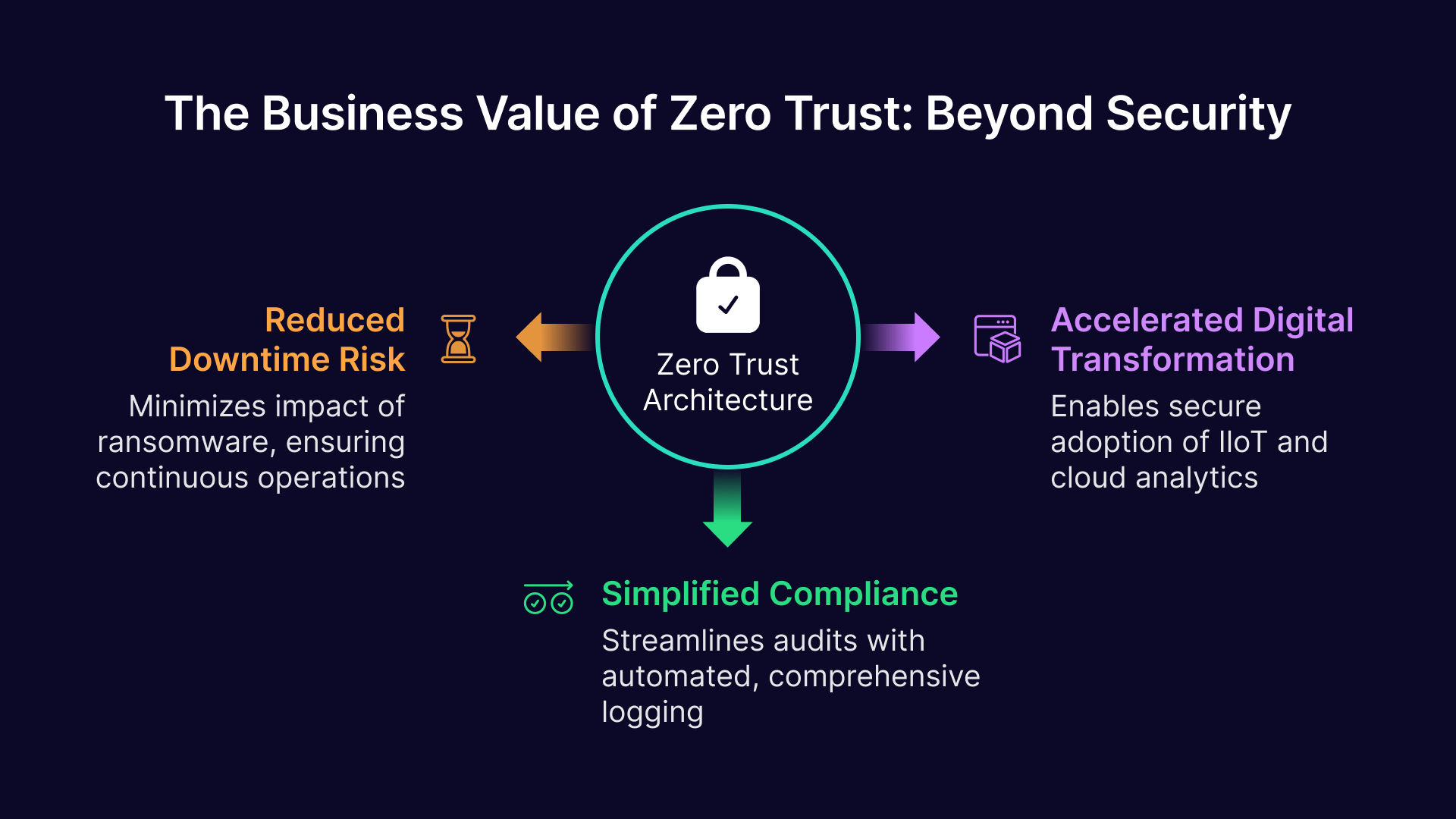
Compliance frameworks are increasingly converging on Zero Trust principles: least-privilege access, continuous authentication, and micro-segmentation. Implementing Zero Trust is not just a security decision — it is the most efficient path to satisfying NIS2, IEC 62443, and NIST CSF simultaneously.
Why Traditional Security Architecture Is Failing Manufacturing
VPNs Expose Your Entire Network to Anyone Who Authenticates
A VPN grants network-level access. When a vendor authenticates to your VPN to service a PLC in Cell 3, they get adjacency to every other device on the OT subnet — and often to portions of the IT network as well. A single compromised VPN credential becomes an unrestricted pass to your production environment. VPNs were designed for remote employees accessing corporate resources; they were never designed for the granular, device-specific access that OT security requires.
Jump Servers Are a Single Point of Failure and an Audit Nightmare
Jump servers (or bastion hosts) were the standard answer to OT remote access for a decade. The problem is structural: a compromised jump server gives an attacker access to every system it connects to, often without session recording or real-time monitoring. Jump servers also create operational friction — IT must manually manage credentials, coordinate sessions, and maintain detailed logs by hand. In practice, most organizations do the last part poorly.
Perimeter Security Assumes the Attacker Is Always Outside
The perimeter model — strong firewall at the edge, trusted traffic inside — breaks down completely when the attacker is already inside, which is the case in most modern attacks. Phishing compromises an employee’s laptop. A vendor’s compromised credentials authenticate successfully through the VPN. A rogue contractor device brought on-site connects to the Wi-Fi. In all of these scenarios, the perimeter has been bypassed before a single alarm is triggered.
Zero Trust: The Framework That Actually Works for Manufacturing
Zero Trust Is Not a Product — It Is an Architecture
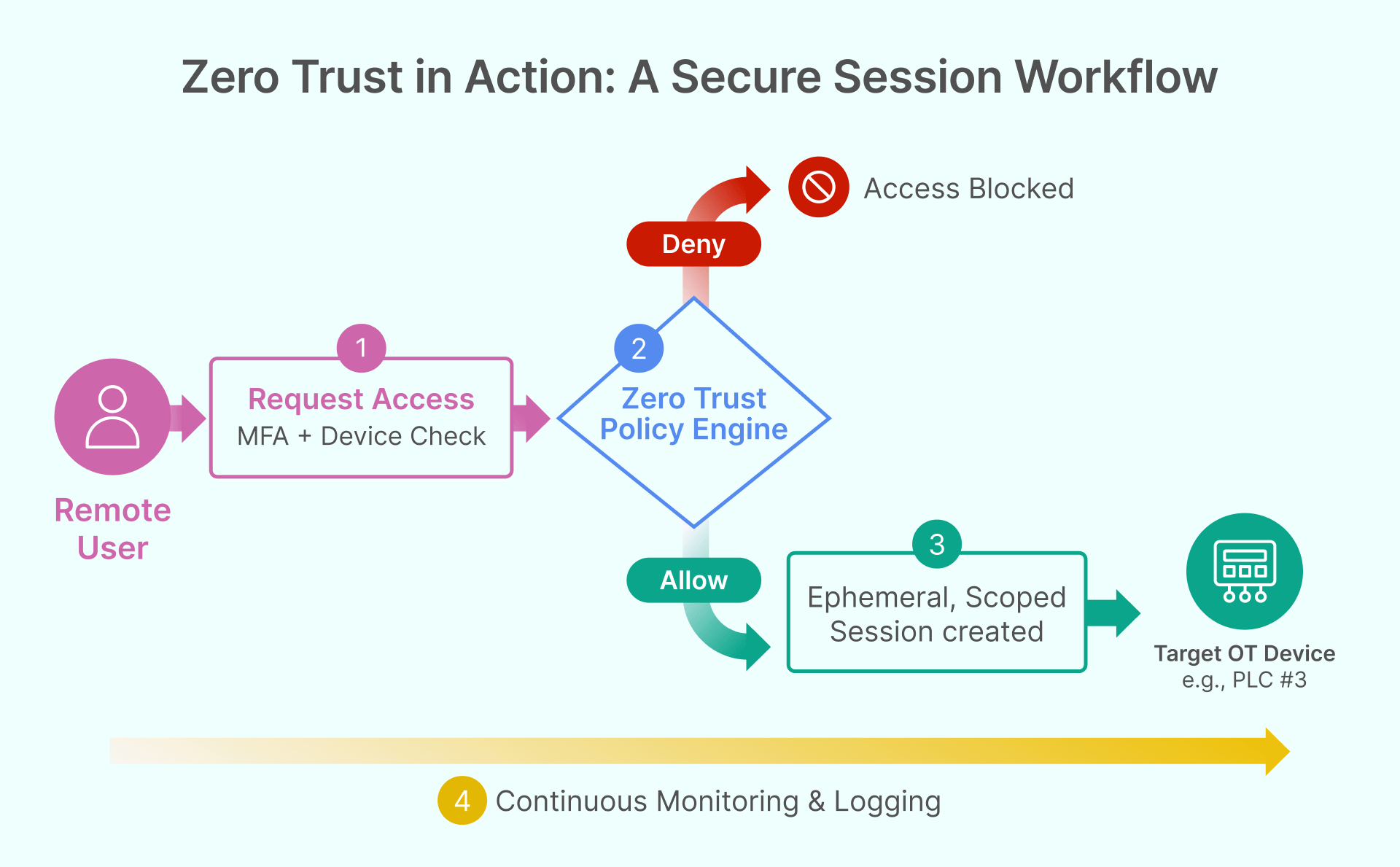
Zero Trust is frequently misunderstood as a specific technology or a single product purchase. It is neither. Zero Trust is a security philosophy built on one foundational principle: never trust, always verify. No user, device, or network location is inherently trusted — every access request must be authenticated, authorized, and continuously validated based on identity, device posture, and context.
For manufacturing, this is transformative. It means a vendor’s session is scoped to exactly the device they need and nothing else. It means a technician’s credentials, even if stolen, cannot be used from an unrecognized device. It means an attacker who compromises one segment of the network cannot move laterally to another.
The Five Core Zero Trust Principles Applied to the Plant Floor
- Verify Explicitly: Every user and device must authenticate before any session is established — including OT vendors, contractors, and internal maintenance teams.
- Least-Privilege Access: Users can only reach the specific resource they are authorized for. A PLC maintenance vendor sees only the PLC they are scheduled to service, not the rest of the OT network.
- Assume Breach: Design every access flow as if an attacker is already inside the network. Micro-segment OT assets so that compromise of one device cannot cascade to others.
- Continuous Validation: Authentication is not a one-time event. Sessions are continuously monitored, and anomalous behavior triggers re-authentication or session termination.
- Comprehensive Visibility: Every access attempt, session action, and system change is logged for audit, compliance, and forensic purposes.
A Practical Zero Trust Roadmap for Manufacturing CISOs
Zero Trust is not a big-bang transformation. The most successful implementations follow a phased approach that delivers immediate risk reduction at each stage while building toward a mature architecture.
Phase 1 — Eliminate VPN for Remote and Vendor Access
Replace broad VPN access with a clientless, Zero Trust Network Access (ZTNA) solution that grants session-based, device-specific access. Start with third-party vendor access to OT assets — this is typically the highest-risk exposure and the fastest win. ZTNA solutions like Thinfinity Workspace establish sessions without exposing network ports, require MFA at every login, and record all session activity for audit.
For a deeper look at the vendor access challenge specifically, see our companion article: Securing Third-Party Vendor Access to Manufacturing OT Networks (Article 6 in this series).
Phase 2 — Segment IT from OT Without Disrupting Operations
True IT/OT segmentation does not mean cutting off connectivity — it means brokering all access through a controlled access plane. A well-designed architecture places a ZTNA gateway in the DMZ that acts as the sole conduit between IT users and OT assets. The OT network has no direct internet exposure; all traffic flows through the gateway, where policies are enforced.
Phase 3 — Apply Privileged Access Management to OT Systems
Not all access is equal. Engineers, administrators, and executives who can modify SCADA configurations or PLC parameters represent a privileged access risk that requires stronger controls: session recording, just-in-time access provisioning, and credential vaulting. Privileged access management (PAM) for OT is a distinct discipline from traditional enterprise PAM — it requires understanding of industrial protocols and the operational constraints of the plant floor.
Phase 4 — Secure Internal Web Applications and Portals
Most manufacturing environments have a collection of internal web applications — MES dashboards, ERP portals, quality management systems, maintenance intranets — that are either only accessible on-site or require a VPN to reach remotely. A Zero Trust web application gateway publishes these applications to authorized users from any device, with MFA enforcement, without exposing the underlying infrastructure. This eliminates the attack surface created by VPN-dependent internal web access.
Phase 5 — Continuous Monitoring and Compliance Reporting
Zero Trust generates rich audit data. Every session is authenticated, every access request is logged, and every policy decision is recorded. This data becomes the foundation for compliance reporting under NIS2, IEC 62443, and NIST CSF — and for threat detection when behavior deviates from baseline. At this stage, the Zero Trust architecture is not just a security control; it is a continuous compliance engine.
How Thinfinity Workspace Accelerates the Zero Trust Journey in Manufacturing
Thinfinity Workspace is a single platform that addresses all five phases of the Zero Trust roadmap described above. It is browser-based, clientless, and designed to operate in both IT and isolated OT environments — including air-gapped networks with no internet access.
- ZTNA Gateway: No open inbound ports, no VPN, no exposed attack surface. All sessions are brokered through the Thinfinity Gateway, authenticated via MFA and RBAC.
- OT Network Access: Thinfinity’s secondary broker architecture allows deployment inside isolated OT networks, providing controlled, monitored access to PLCs, SCADA, and HMI systems without IT/OT bridging.
- Session Recording and Audit: Every session is fully recorded and logged, providing the audit trail required for IEC 62443 and NIS2 compliance.
- Privileged Access Management (RPAM): Built-in PAM capabilities manage privileged sessions, credential vaulting, and just-in-time access provisioning for OT administrators.
- Internal Web Application Gateway (WebBridge): Publish MES portals, ERP interfaces, and internal web apps with Zero Trust enforcement, without modifying the applications themselves.
- Legacy Application Support: Thinfinity VNC and VirtualUI deliver legacy HMI and Windows applications through the browser, extending Zero Trust coverage to systems that cannot be modernized.
Continue Reading — Manufacturing Series
Secure IT/OT Network Integration with Thinfinity — A Technical Deep Dive
FAQ
What makes manufacturing more vulnerable than other industries?
Manufacturing environments combine three factors that create exceptional cybersecurity risk: legacy OT systems that were never designed with security in mind, increasing IT/OT connectivity driven by Industry 4.0 initiatives, and a production-critical operational model where downtime has immediate, quantifiable financial impact. Ransomware operators deliberately target manufacturers because the cost of downtime often exceeds the ransom demand — making payment the path of least resistance for many organizations.
Is Zero Trust implementation feasible for an OT environment where uptime is critical?
Yes — and modern ZTNA solutions are specifically designed to avoid introducing latency or instability into OT environments. Solutions like Thinfinity Workspace use a brokered, browser-based access model that overlays the existing OT network without modifying device configurations or industrial protocols. The security layer is in the access path, not on the OT devices themselves, which means legacy PLCs and SCADA systems require no changes. Phased rollouts, starting with vendor access rather than operational systems, allow organizations to build confidence before extending Zero Trust coverage to more sensitive parts of the plant.
What is the difference between IT security and OT security in a manufacturing context?
IT security prioritizes confidentiality, integrity, and availability (the CIA triad) — in that order. OT security in manufacturing inverts this: availability comes first, because a stopped production line is often a more immediate risk than a data breach. This means security controls in OT environments must be non-disruptive, must not introduce latency into real-time control systems, and must be designed around the operational constraints of the plant rather than the convenience of IT administrators. It also means that patching — the cornerstone of IT security — is often not possible in OT, since many PLC and SCADA vendors prohibit unauthorized software changes.
How does Zero Trust address the third-party vendor access problem?
Zero Trust replaces the broad network access granted by traditional VPNs with session-based, device-specific access that is scoped to exactly the resource a vendor needs — and nothing else. Access is granted per session, requires MFA at every login, is time-limited, and is fully recorded for audit. Vendors never see network-layer access; they connect to a specific machine through a brokered session, and the session is terminated as soon as the maintenance window closes. Even if a vendor’s credentials are compromised, they cannot be used from an unrecognized device or outside the authorized time window.
What compliance frameworks require Zero Trust for manufacturing?
Several major frameworks now either require or strongly recommend Zero Trust principles for manufacturing environments. The NIS2 Directive (EU) requires access control, incident detection, and supply chain security measures that align with Zero Trust for any manufacturer of critical products. IEC 62443 defines security levels for ICS/SCADA environments that require micro-segmentation, access control, and continuous monitoring. NIST CSF 2.0 explicitly addresses OT environments and includes identity management, access control, and continuous monitoring as required capabilities. Additionally, automotive manufacturers supplying to major OEMs are increasingly subject to VDA ISA / TISAX requirements that specify similar controls.
What is the first step a manufacturing CISO should take toward Zero Trust?
The highest-impact, lowest-disruption starting point is securing third-party vendor access to OT systems. This addresses the most commonly exploited attack vector in manufacturing, requires no changes to OT device configurations, and delivers immediate audit and compliance benefits. Replace any always-on VPN or remote desktop access used by machine vendors and integrators with a ZTNA solution that enforces MFA, scopes access to specific devices, and records all session activity. This single change closes the door on the most common ransomware entry point in manufacturing environments.