In this quick article, we’ll show you how to secure your current Thinfinity® Desktop environment by using Windows Group Policies to restrict and limit the usage of your users to only what’s necessary.
Group Policy are a series of settings in the Windows registry that concern security and other operational behaviors.
Group Policy lets you prevent users from accessing parts of the system, run specific scripts when the system starts up or shuts down, and forces a particular home page to open for every user in the network. All this being said, let’s start with this tutorial.
First of all, you’ll need to create a GPO.
- Open Start.
- Search for MMC and click the first result to open the Microsoft Management Console.
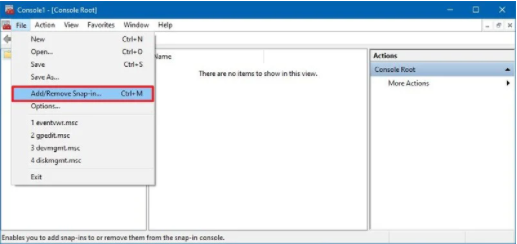
- Click the File menu.
- Select the Add/Remove Snap-in option.
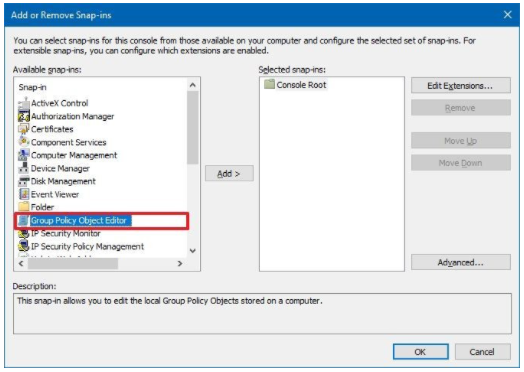
- Under the “Available snaps-ins” section, select the Group Policy Object Editor snap-in.
- Click the Add button.
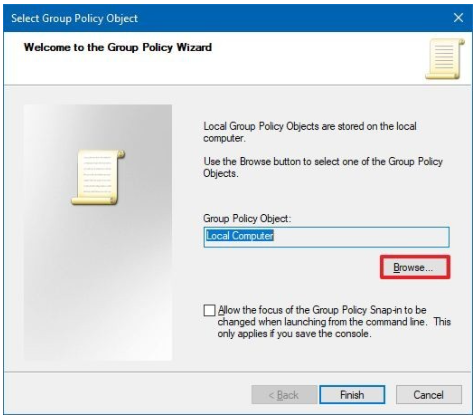
- Click the Browse button.
- Click the Users tab.
- Select the user or group you want to apply a specific set of policies.
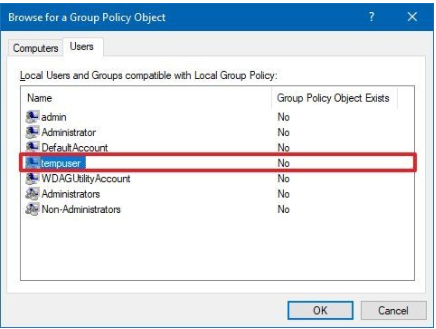
- Click the OK button.
- Click the Finish button.
- Click OK again.
- And now let’s save the changes we did by clicking in the File menu.
- Select the Save As option.
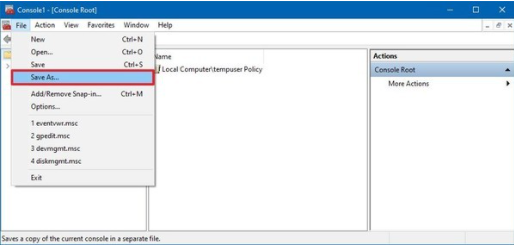
- Now let’s confirm a name for the snap-in.
- Select a location to store the console.
- Click the Save button.
After this final step, we are ready to start restricting a user or even a group of users using Windows Group Policies.
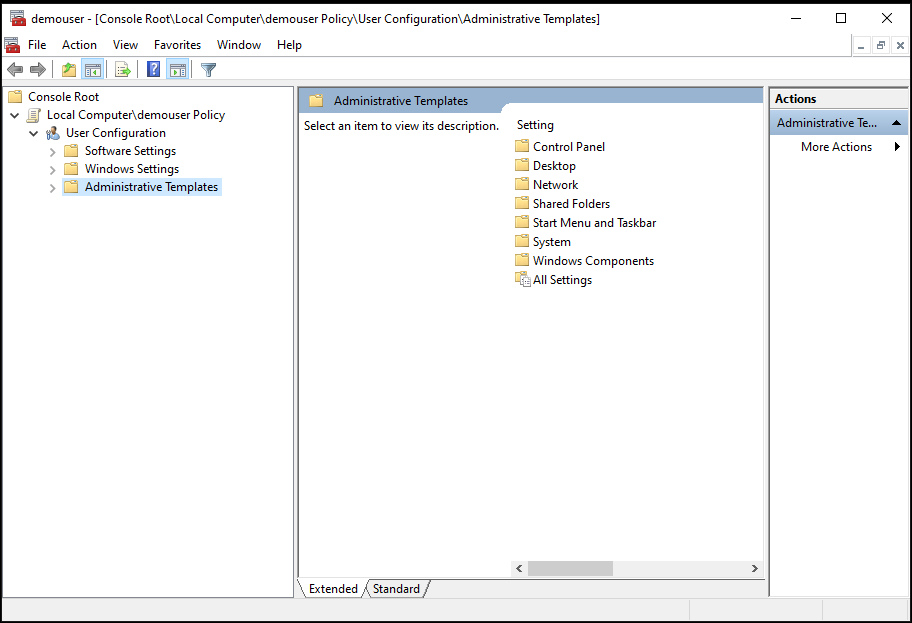
Restrict access to the Command Prompt
The command prompt is very useful for system administrators, but in the wrong hands, it can turn into a nightmare because it gives users the opportunity to run commands that could harm your network. Therefore, it’s best to disable it for regular users. You can do that by using the “Prevent access to the command prompt” policy. You’ll be able to find this policy under -User configuration/Administrative Templates/System- If you enable this policy, the affected user or group of users won’t be able to load Windows command prompt.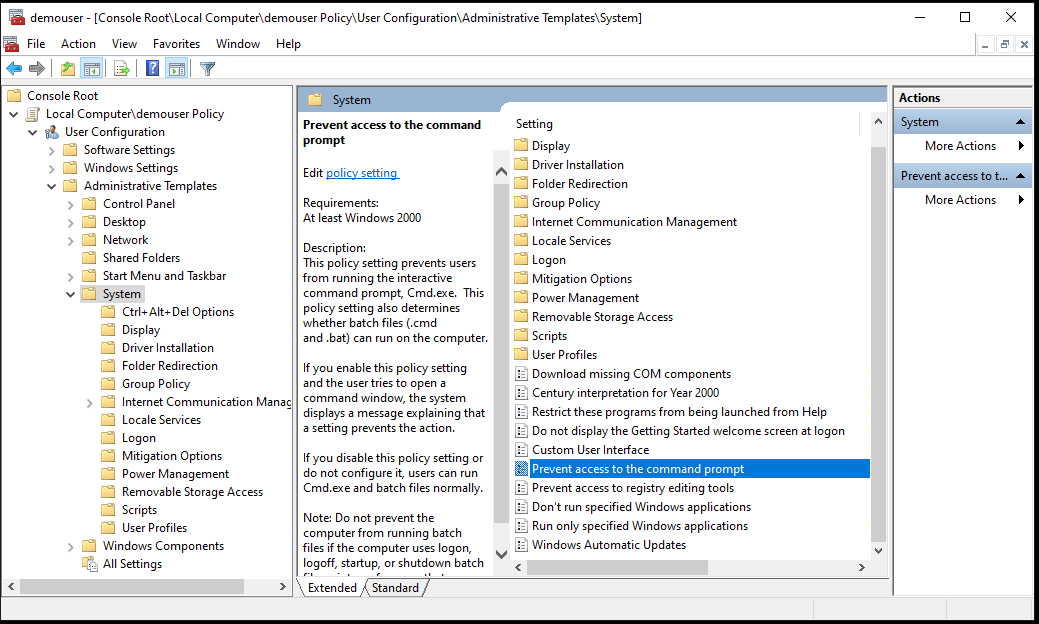
Disable Windows Control Panel
Control Panel restrictions are vital for business networks and school environments. If you want to prevent end-users from changing settings, this is a good step to take. You’ll be able to find this policy under -Administrative Templates/Control Panel- and then enable ‘Prohibit Access to Control Panel and PC settings’.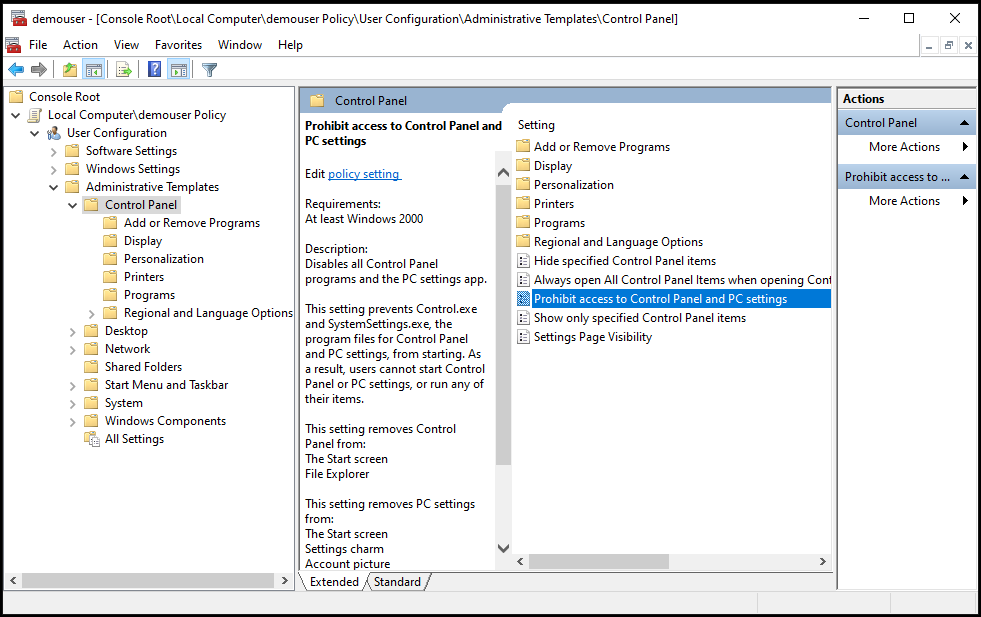
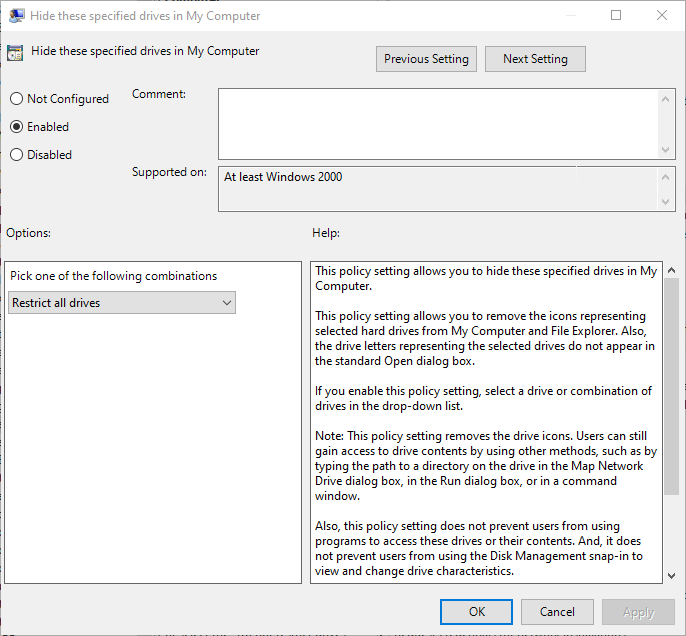
Hide Specified Drives in ‘My Computer’
With Windows Policies, you can also restrict access to any drives. In this case, we are going to disable access to all drives, but you can as well restrict only one drive (the C:// drive for example)
You can find this policy under – User configuration/Administrative Templates/Windows Components/File Explorer – and then search for the ‘Hide these specified drives in My Computer’ option and enable that. Once you enable that option, you’ll be able to restrict which drives you want to restrict.
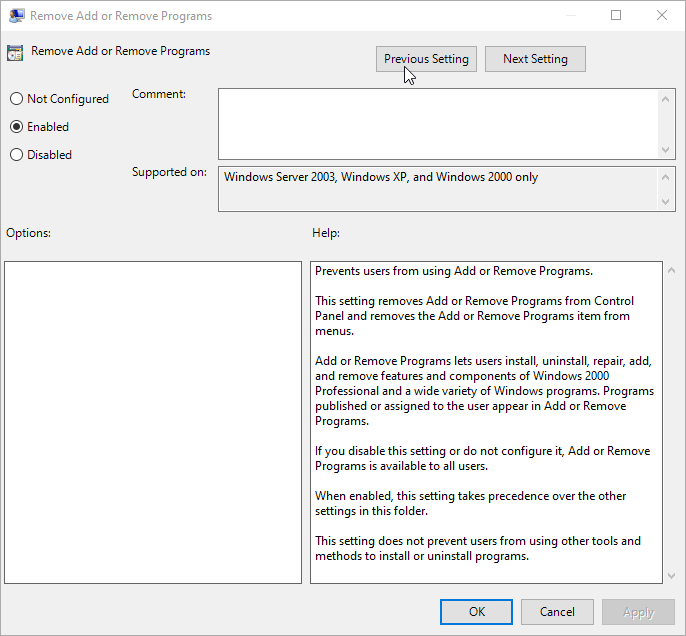
Disable “add or remove programs”
Disable the ability to add or remove programs is definitely on our list. Imagine giving the end-user the ability to add or remove programs at will… You can imagine the downsized on that. So let’s review how to easily disable this option.
In this case, you can find this policy under – User Configuration/Administrative Templates/Control Panel/Add or Remove Programs – And enable the policy called ‘Remove Add or Remove Programs’.
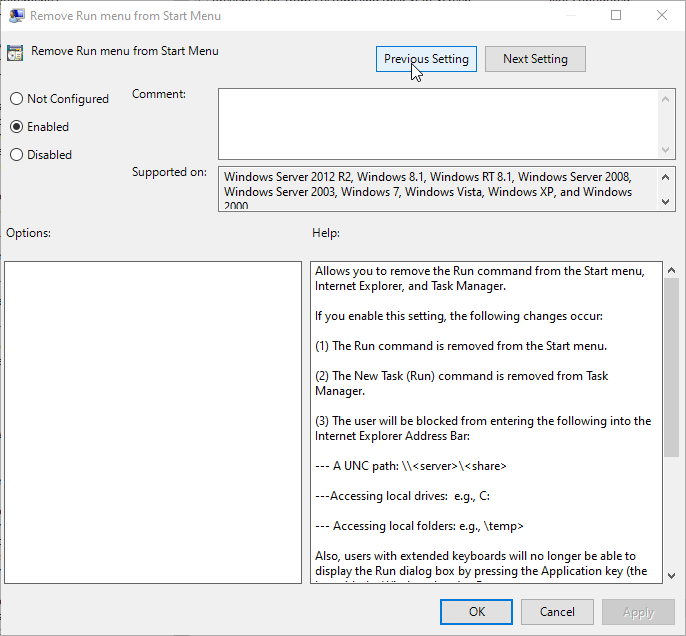
Remove ‘Run’ from the start menu
The run dialog is one of the oldest Windows features and allows users to manually execute any application or script by calling the full path of the .exe or script you want to call. Disabling the Run button in the start menu is often done as a prevention from users running unauthorized software or batch scripts.
You can find this policy under – User Configuration/Administrative Templates/Start Menu and Taskbar – and now enable the policy called ‘Remove Run menu from Start Menu’.
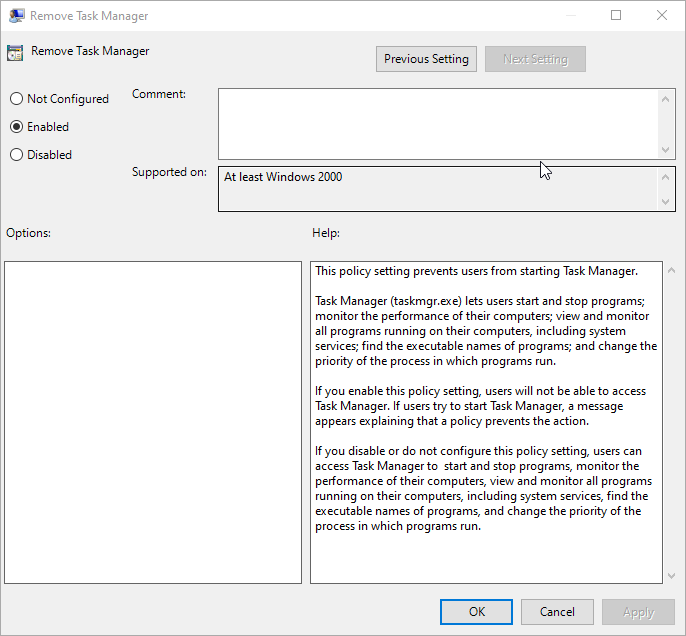
Remove access to Windows Task Manager
The Windows Task Manager is an advanced feature that gives you access to tools to start and stop applications, monitor system performance, running apps and servers and much more. Although it is a handy tool, sometimes you may want to disable access to prevent users from restarting specific programs, changing processes priorities, or because you need to comply with your organization’s policies. In any case, we have the solution for you.You can find this GPO under – User Configuration/Administrative Templates/System/Ctrl+Alt+Del Options – Here you can find a policy called ‘Remove Task Manager’ If you enable this setting, your end-users won’t be able to load the task manager.
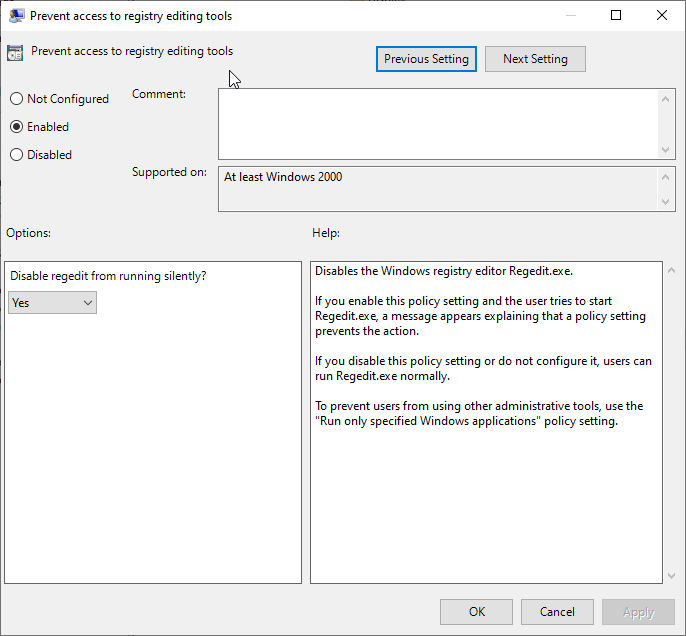
Disable access to the Windows Registry
Improper changes to the Windows Registry may make your computer run abnormally or prevent it from booting properly. Definitely messing around in the Windows Registry can cause all kinds of problems if you’re not careful. So this is an important policy to disable. You can find this policy under – User Configuration/Administrative Templates/System – Under this section you’ll find the policy called ‘Prevent access to registry editing tools’ If you enable this setting, users won’t be able to load Windows Registry by searching for the regedit.msc reference.
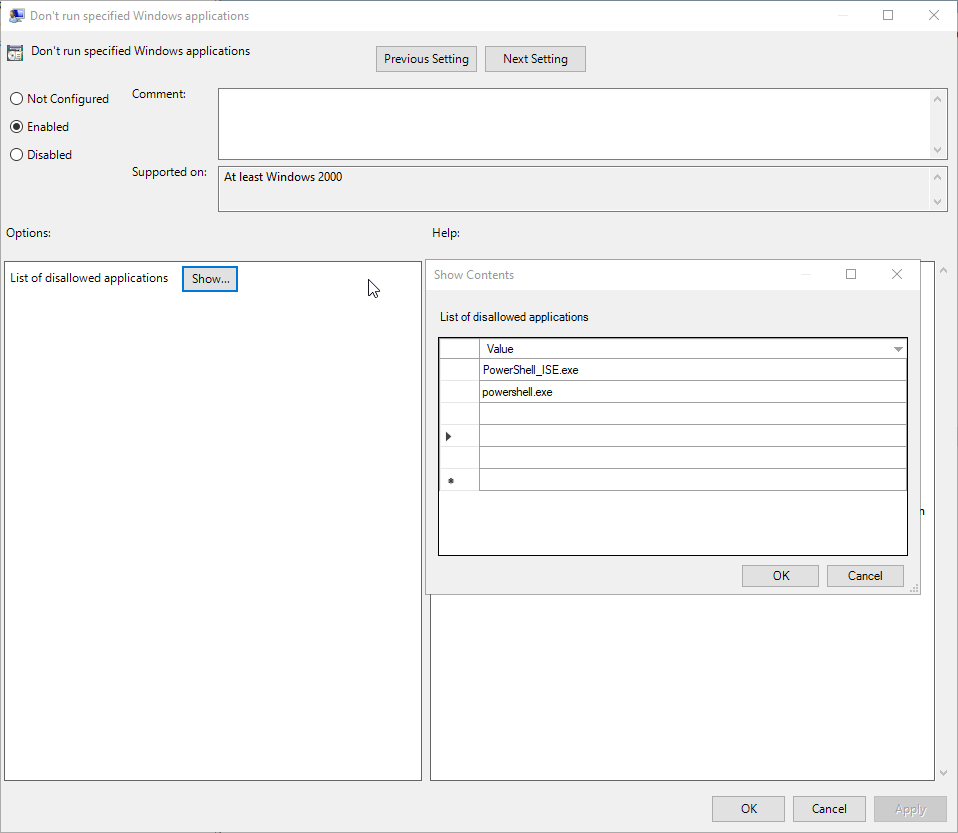
Prevent running specific Windows applications
This is by far one of the most useful policies for a Windows Administrator. A computer used by multiple users will always require some restrictions for better use. Some applications may not be suitable for some group of users, or you may not want to share with other users. In certain situations, you might want to restrict some of the programs on your computer. The reason can be privacy-related for the users or to be safe from issues caused by misuse of the programs.
To disable this policy, go to – User Configuration/Administrative Templates/System – Here you can find the policy called ‘Don’t run specified Windows applications’ In this case, you just need to enable the policy and open the list of disallowed applications and start typing the .exe you want to disallow. As you can see, in this case, we have disabled the use of Powershell and Powershell_ISE applications.
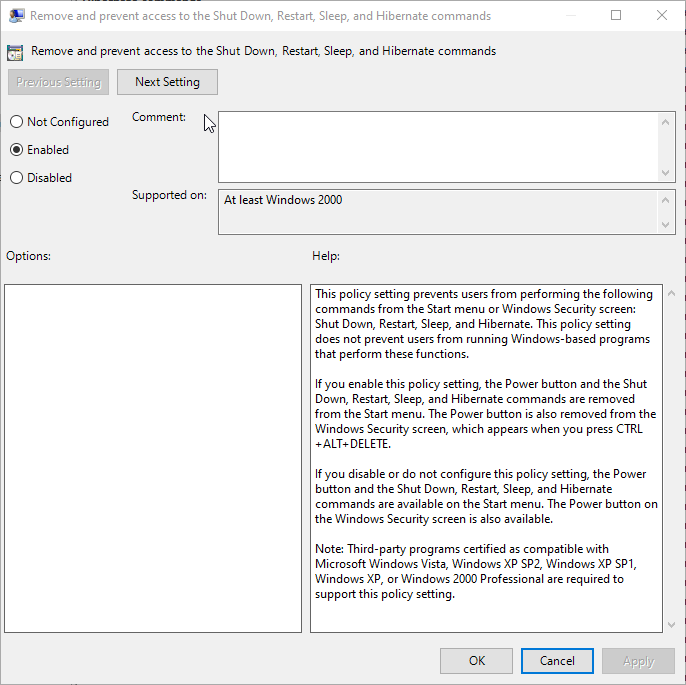
Some personal computers or servers should be running all the time for specific tasks. Servers are commonly used to deliver services that are constantly required, which is why they are never turned off. Similarly, some personal computers will be running certain processes that take a long time and the computer should be running for it.
However, someone can accidentally click on one of the power options which results in terminating the processes on your system. If used by multiple users, then another user can also use the power option without knowing that it should be running.
In this case, you can find this policy under – User Configuration/Administrative Templates/Start Menu and Taskbar – In this section, you’ll find a policy called ‘Remove and prevent access to the Shut-Down, Restart, Sleep and Hibernate commands’ and if you enable this policy, end-users won’t be able to Shut Down, Restart, Sleep or Hibernate your servers.
 Now you know how to manage Group Policies to make your Windows environments safer. If you have any questions, please email us at [email protected].
Now you know how to manage Group Policies to make your Windows environments safer. If you have any questions, please email us at [email protected]. 

