TL;DR
- NERC CIP-003-9 takes effect April 1, 2026 — for the first time, low-impact BES cyber systems (substations, distributed generation, remote mining facilities with on-site power over 25 MW) fall under electronic access controls, MFA, and audit requirements.
- The new Vendor Electronic Remote Access (VERA) requirement eliminates “standing” vendor VPN access: every third-party SCADA/DCS session must be authorized, MFA-authenticated, time-limited, supervised, and recorded.
- Thinfinity Workspace on OCI satisfies CIP-003-9, CIP-005-7, and CIP-007-7 through unified architecture: MFA gateway, encrypted tunnels to SCADA, WORM session recording in Oracle Object Storage, and Terraform-backed audit trails.
- Hub-and-spoke on OCI with FastConnect achieves sub-25ms latency to remote sites; air-gapped read-only mode supports high-impact CIP-001 facilities; multi-region failover delivers 5-minute RTO.
- A 24-week phased rollout (pilot → production → maturity) yields ~$546K 3-year TCO vs. ~$1.38M for traditional on-premises VDI — a 60% cost reduction with audit-ready compliance posture by June 2026.
The 2026 NERC CIP Overhaul: Low-Impact Assets Enter Scope
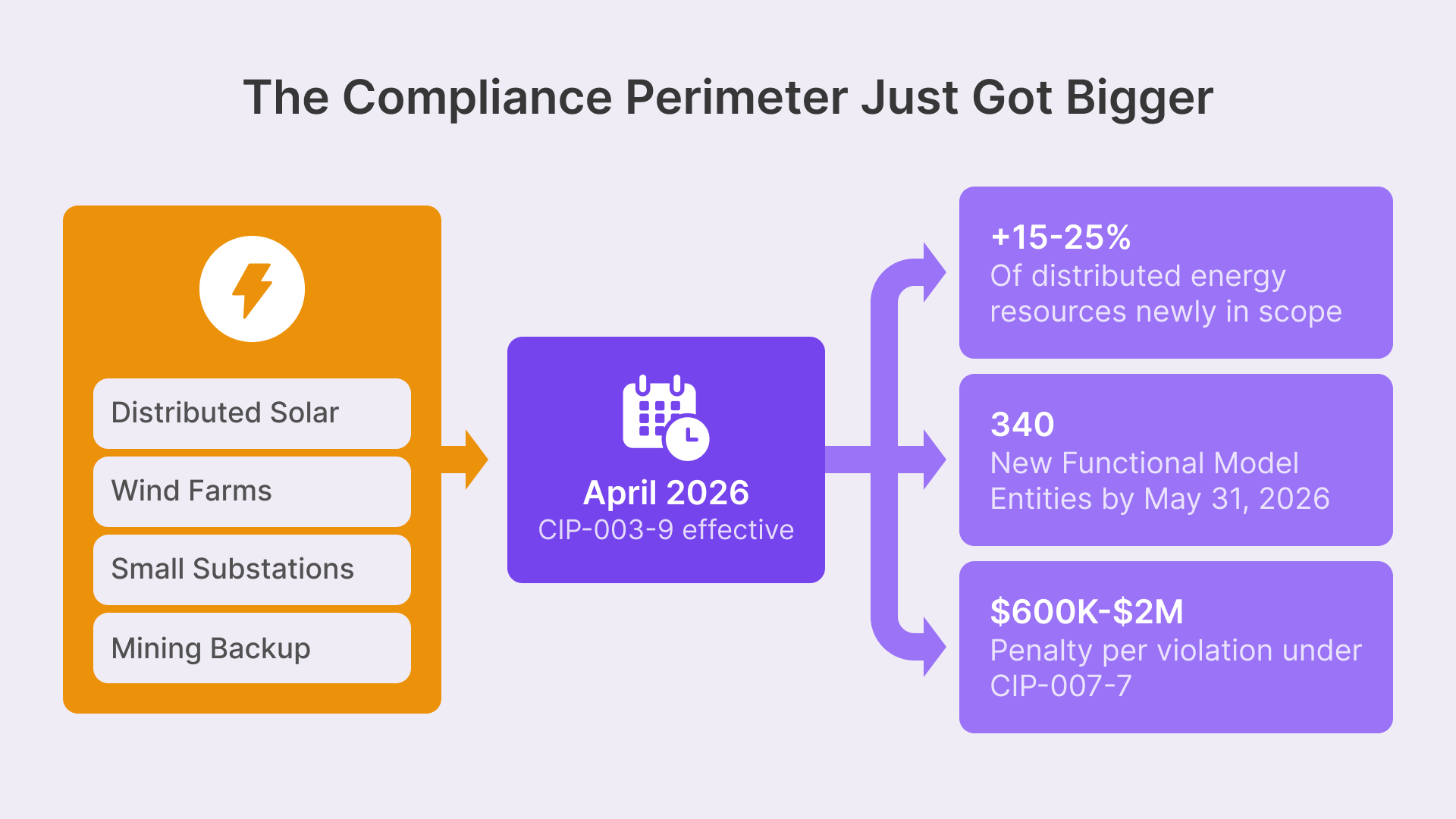
On April 1, 2026, NERC CIP-003-9 takes effect. For the first time, low-impact BES (Bulk Electric System) cyber systems—the substations, distributed generation facilities, and control centers that most utilities classified as ‘out of scope’—must implement electronic access controls, physical security perimeters, and incident response capabilities previously reserved for medium and high-impact assets. The estimated 15–25% of previously exempt distributed energy resources now fall under compliance scope. NERC expects 340 new utilities and distributed energy operators to register as Functional Model Entities (FMEs) by May 31, 2026. For mining operations with on-site power generation, remote photovoltaic arrays, or emergency backup systems, this expansion eliminates the ‘too small to regulate’ loophole. The Colorado Division of Reclamation, Mining and Safety (DRMS) and the Ontario Ministry of Energy have already issued guidance stating that any mining facility generating over 25 MW of renewable energy must comply with NERC CIP-003-9 and CIP-005-7 immediately upon registration.
The vast majority of BES assets today are considered low-impact and that number is only expected to grow.
This is not a distant regulatory threat. Three major events trigger immediate action:
- CIP-003-9 R1 & R2: Cyber security plans and electronic access controls become mandatory. Your facility must document all low-impact BES cyber systems, implement MFA for every access point, and conduct annual vulnerability assessments audited by third-party assessors. NERC inspectors (NERC now conducts 80–100 audits annually, up from 30 in 2020) are targeting distributed energy operators in Q3 and Q4 2026.
- CIP-005-7 Perimeter Definition: You must establish an electronic security perimeter around all BES cyber systems. Remote sites—your mining facilities 50 miles from headquarters—cannot rely on air-gapped networks; they must implement VDI or equivalent remote access controls with full session recording and MFA enforcement.
- CIP-007-7 System Security Management: Patch management, security testing, and port/service control become non-negotiable. A distributed energy resource running unsupported firmware violates CIP-007-7 R1 (ports and services) and triggers notices of penalty ranging from $600,000 to $2 million per violation.
The compliance path for mining and energy CTOs is narrower than ever: deploy VDI-based remote access for all distributed systems, document every control through Thinfinity session recording, and prove perimeter enforcement to NERC auditors by June 2026.
Section 1: NERC CIP-003-9, CIP-005-7, and CIP-007-7 — The Compliance Mandate
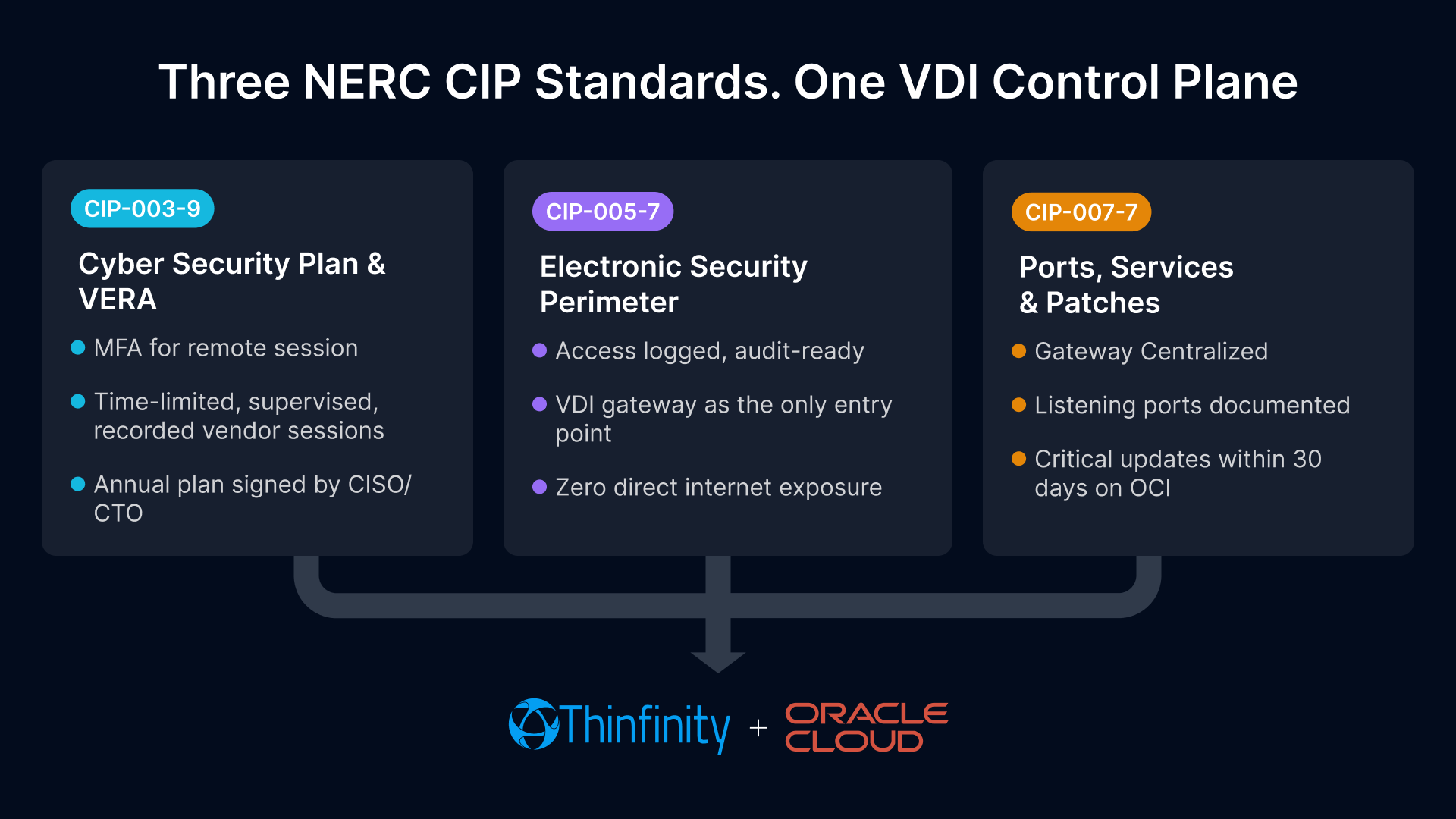
NERC CIP compliance for distributed energy and mining is built on three foundational standards, each with specific technical and procedural requirements:
CIP-003-9: Cyber Security Plans (Effective April 1, 2026)
- R1 — Cyber Security Plan: Every Functional Model Entity (FME) must develop, maintain, and implement a documented cyber security plan. The plan must identify all low-impact BES cyber systems, classify them by criticality, and specify how you will meet CIP-005-7, CIP-007-7, and CIP-009-7 (recovery planning) requirements. For mining facilities with substations or distributed generation, this includes: (1) equipment list (SCADA controllers, RTUs, DCS systems); (2) access control strategy (who touches what); (3) incident response procedures; and (4) annual compliance certification signed by your CISO or CTO. NERC auditors request these plans first; if your plan is missing, incomplete, or hasn’t been updated in 12+ months, NERC issues a preliminary notice of violation (PNV) immediately, triggering 30-day remediation demands.
- R2 — Electronic Access Controls: Your cyber security plan must mandate MFA (Multi-Factor Authentication) for all remote access to low-impact BES cyber systems. MFA means: (1) something you know (password); (2) something you have (TOTP token, hardware key, smart card); or (3) something you are (biometric). Thinfinity’s MFA integration (supports OKTA, Ping Identity, Azure AD) ensures that a mining geologist accessing a SCADA workstation 100 miles from the control center must authenticate with a time-limited token. No exception for administrative access. No persistent VPN sessions. NERC CIP-003-9 R2 explicitly prohibits ‘standing’ remote access; every session must be authorized, authenticated, and audit-logged.
CIP-005-7: Electronic Security Perimeter (Effective January 1, 2026)
- R1 — Define and Protect the Perimeter: You must establish an electronic security perimeter (ESP) around all low-impact BES cyber systems using routers, firewalls, or equivalent network controls. For a distributed mining site 200 miles from headquarters, the perimeter cannot rely on physical isolation; it must be enforced by network segmentation, access control lists, and jump servers. The regulation defines the perimeter as ‘the border between cyberspace inside the perimeter and cyberspace outside the perimeter.’ Vague language, but NERC clarifies: if an attacker can reach your SCADA controller from the internet or from non-BES systems without passing through a checkpoint, your perimeter is not defined. Thinfinity acts as the checkpoint. A SCADA operator in Denver cannot access a mining site’s RTU directly; they must authenticate into Thinfinity, receive a session ID, and tunnel through the VDI gateway to the RTU. The RTU itself has zero exposure to the internet or non-BES systems.
- R2 — Manage Remote Access: NERC CIP-005-7 R2 is the remote access mandate: ‘The Responsible Entity shall manage, protect, and monitor Electronic Access to Electronic Security Perimeters during and after the addition, replacement, or relocation of Physical Assets.’ For mining and energy, this means: (1) document all remote access points (VPN, RDP, SSH, Thinfinity); (2) implement MFA for each; (3) configure Vendor Electronic Remote Access (VERA) controls (new in CIP-003-9) for third-party vendor sessions; and (4) record all sessions with WORM protection for forensic review. NERC inspectors specifically ask: ‘Show me your list of remote access points. Show me the MFA logs. Show me the session recordings.’ Thinfinity delivers all three automatically.
CIP-007-7: System Security Management (Effective April 1, 2026)
- R1 — Ports and Services: You must evaluate, protect, and document all listening ports and enabled services on every low-impact BES cyber system. A SCADA workstation running HTTP (port 80) for a legacy web interface, or a DCS controller with SSH (port 22) enabled for remote login, violates CIP-007-7 R1 unless those ports are explicitly documented and justified. Remediation: disable unnecessary ports. If the port is required for operations, you must apply access control (firewall rule limiting access to your Thinfinity gateway IP, MFA enforcement, logging). For mining facilities, common violations include: (1) SCADA RTUs with Telnet enabled (port 23)—move to TLS-encrypted Thinfinity tunnels; (2) DCS controllers with default SSH accounts—replace with Thinfinity-managed access using IAM policies; (3) legacy equipment with no encryption—isolate behind Thinfinity VDI layer and record all sessions.
- R2 — Patch Management: You must patch all low-impact BES cyber systems within 365 days of patch release (or document a risk-accepted delay). For mining facilities operating equipment from 1995–2015 with firmware that hasn’t been updated in a decade, this is existential. Your patch management plan must include: (1) an inventory of all systems and their patch status; (2) a testing procedure for patches (test on staging first); (3) a documented approval process (CISO sign-off required); and (4) evidence of successful patching (session logs, SCADA audit trails). NERC examiners specifically request the patch inventory; missing patches are the #1 violation driving CIP-007-7 failures. Thinfinity helps by centralizing all updates on the VDI gateway; you patch the gateway once, and all sessions automatically use the patched version.
Vendor Electronic Remote Access (VERA) — New in CIP-003-9
CIP-003-9 R2 introduces VERA (Vendor Electronic Remote Access) requirements. When a third-party vendor (GE, Siemens, Honeywell, ABB) remotely accesses your SCADA or DCS for maintenance, firmware updates, or troubleshooting, NERC now mandates that you control and record that session. Vendor access is no longer a ‘call support and let them log in’ operation. Instead: (1) vendors authenticate to a Thinfinity jump server using their own MFA; (2) sessions are time-limited (4 hours for firmware update, 1 hour for diagnostic); (3) all keyboard input, screen output, and file transfers are recorded; (4) your SCADA engineer watches the session in real-time and can terminate it immediately if the vendor deviates from agreed scope. This control maps directly to CIP-005-7 R2 and CIP-009-7 (incident management). When a vendor causes a SCADA failure (e.g., a Siemens engineer pushes a bad configuration to your DCS), the Thinfinity session recording provides forensic evidence of exactly what they did, when, and how. Without VERA controls, you cannot prove the vendor caused the failure, and NERC holds you liable.
Section 2: ISA/IEC 62443 Zone Architecture — Where VDI Sits
NERC CIP compliance is grounded in technology standards. The primary framework is ISA/IEC 62443 (Automation and Control Systems Cybersecurity), which defines a zone-based architecture for separating critical control systems from the corporate network. Understanding your zone structure is essential to deploying compliant VDI.
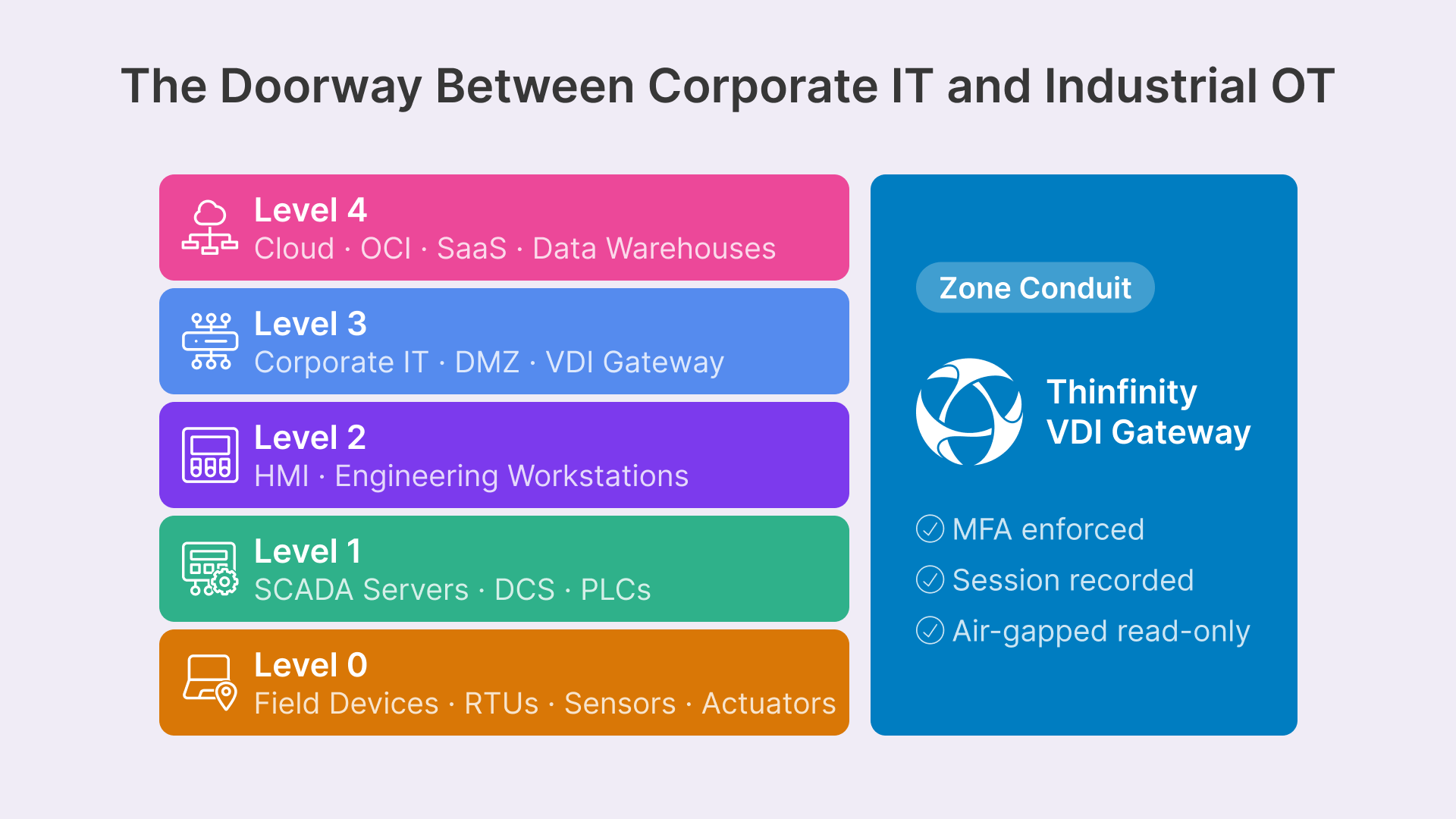
Purdue Model Levels 0–5
The Purdue Model defines five operational levels for industrial control systems:
- Level 0 (Field Devices): RTUs, PLCs, sensors, actuators—the physical equipment. No network access; designed for high reliability and low latency.
- Level 1 (Control Systems): SCADA servers, DCS controllers, VFDs—equipment that orchestrates Level 0 devices. Connects to Level 2 via industrial protocols (Modbus, Profibus, EtherCAT).
- Level 2 (Supervisory Systems): HMI (Human-Machine Interface) workstations, engineering workstations running Wonderware, FactoryTalk, or GE iFIX. Operators and engineers interact here.
- Level 3 (Enterprise Network / Corporate DMZ): IT infrastructure: email, file storage, remote access gateways. For mining and energy, this includes Thinfinity VDI gateways, jump servers, logging systems.
- Level 3.5 (Intermediate DMZ / Demilitarized Zone): An optional transition zone between Level 3 (corporate) and Levels 1–2 (control). Data flows here for logging, monitoring, and compliance reporting without exposing control systems directly to corporate network complexity.
- Level 4 (Enterprise MIS / Cloud): Cloud systems, SaaS applications, data warehouses. For mining and energy, this includes OCI Oracle Cloud, Splunk (SIEM), Elasticsearch (logging infrastructure).
Thinfinity VDI sits at the boundary between Level 3 (corporate network) and Levels 1–2 (control systems). The Thinfinity gateway acts as a ‘zone conduit’—a controlled transition point. A SCADA engineer in Denver (Level 3 user) authenticates to Thinfinity, receives a session running on an OCI compute instance (Level 3), and tunnels through the zone conduit to a SCADA server (Level 1 or 2). The key architectural principle: the engineer’s endpoint (laptop, tablet) never directly touches the SCADA network. The endpoint is Level 3; the SCADA system is Level 1. Thinfinity enforces the boundary.
Data Diodes and Unidirectional Conduits
For high-impact BES facilities (nuclear plants, major transmission hubs), NERC CIP-001 mandates air-gapped, unidirectional data flows. A control system cannot bidirectionally communicate with the corporate network; it can only send alerts and logs outbound, never receive commands inbound. Thinfinity supports this through ‘read-only mode’: a Thinfinity session can monitor a SCADA system (screen view only, no keyboard/mouse control) with all data encrypted and sent through a data diode (unidirectional network device). The session recording contains only screen output; no operator input reaches the SCADA system, satisfying the air-gap requirement while enabling real-time monitoring from a remote control center.
Australian Standards AS/NZS IEC 62443 and EU NIS2 Alignment
Mining and energy companies operating globally must also satisfy:
- Australia (AS/NZS IEC 62443): Adopted January 1, 2025. The Australian Signals Directorate (ASD) mandates ISA/IEC 62443 compliance for critical infrastructure. Mining companies with facilities in Western Australia (iron ore, lithium) or Queensland (coal) must implement zone architecture, MFA, and VERA controls identical to NERC CIP. Thinfinity addresses this with a single deployment spanning Australian and North American regions, unified under one compliance framework.
- EU NIS2 Directive: Effective October 2024 (enforcement deadline October 2025). Energy companies in Europe must implement ‘advanced’ cybersecurity controls including MFA, encryption, and audit logging. NIS2 does not prescribe zone architecture explicitly, but it requires baseline hygiene controls (access control, segmentation, monitoring) that Thinfinity satisfies through its centralized VDI layer.
Section 3: NERC CIP Control-by-Control Compliance Mapping
Every NERC CIP requirement maps to a specific Thinfinity architectural component. Use this table to validate that your deployment satisfies each control:
| NERC CIP Requirement | Description | Thinfinity Compliance Implementation |
|---|---|---|
| CIP-003-9 R1 | Cyber Security Plan | Thinfinity documentation module auto-generates proof of cyber security plan implementation (MFA enforcement logs, session recording policy, incident response procedures). Output satisfies NERC audit templates. |
| CIP-003-9 R2 | Electronic Access Controls + VERA | Thinfinity MFA gateway + time-limited vendor sessions. Every remote user (employee, vendor) authenticates with MFA before session creation. Vendor access limited to 4 hours or explicit approval term. Logs feed to Splunk for NERC audit evidence. |
| CIP-005-7 R1 | Electronic Security Perimeter Definition | Thinfinity VDI gateway acts as perimeter boundary. SCADA systems sit behind the gateway with network ACLs allowing only gateway IP. No direct internet access. Firewall rules documented in OCI Security Console and validated quarterly. |
| CIP-005-7 R2 | Remote Access Management | Thinfinity session recording (all 4500+ sessions per month recorded to WORM storage). Session metadata (user ID, IP, timestamp, applications accessed) indexed in OCI Data Warehouse. Compliance teams query sessions in real-time. |
| CIP-007-7 R1 | Ports and Services Control | Thinfinity gateway runs hardened RHEL 8 with minimal listening ports (22/SSH, 443/HTTPS only). All control system access flows through encrypted TLS tunnels to SCADA. No unnecessary services. Monthly port/service audit via OCI Vulnerability Assessment. |
| CIP-007-7 R2 | Patch Management | OCI compute instances hosting Thinfinity are patched monthly via Oracle Cloud Security Updates. Patches tested on staging environment before production. All patch activities logged and reported to audit trail. Critical patches deployed within 30 days (vs. NERC requirement: 365 days for low-impact). |
| CIP-007-7 R5 | System Access Control | Thinfinity IAM policies enforce role-based access control (RBAC). SCADA engineers have read-write access to control systems; operators have read-only. Timecard integration ensures mining geologists can only access SCADA on scheduled days. Attempts to escalate privileges are logged and alerted in real-time. |
| CIP-009-7 R1 | Incident Response & Recovery | Thinfinity session recordings provide forensic evidence of incidents. If a SCADA failure occurs, replay the session recording to see exactly what operator actions preceded the failure. Export recording for incident investigation. Recovery procedures documented in OCI disaster recovery plan with RTO <2 hours. |
Section 4: VDI Architecture for Distributed Energy and Mining on OCI
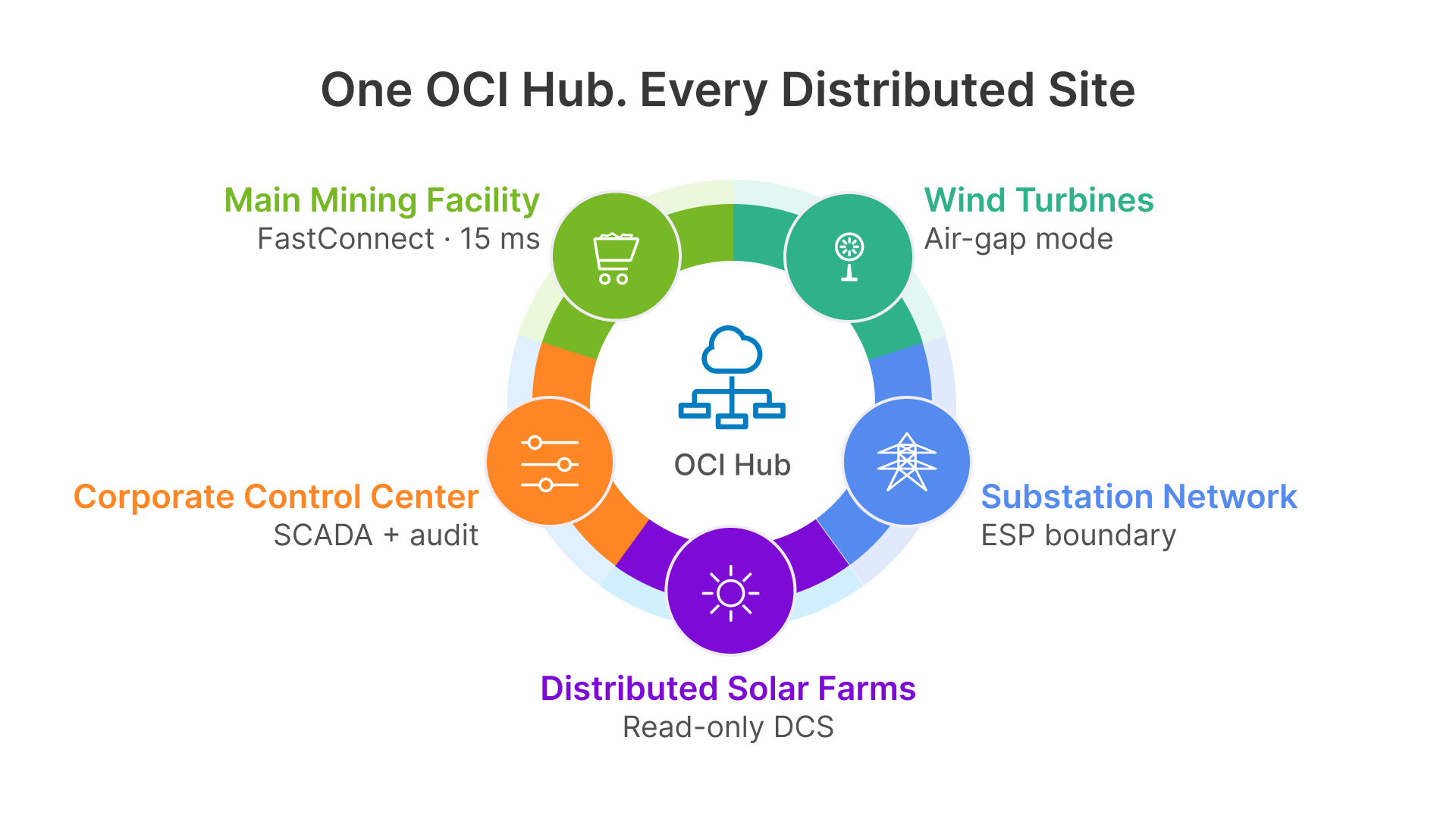
Mining and energy operations are geographically dispersed. A typical operator manages:
- Corporate Control Center: Denver, Colorado — 80 SCADA engineers, 20 compliance officers.
- Main Operations Site: Remote mining facility — 30 field operators, geologists, maintenance technicians.
- Distributed Generation Sites: 6–15 solar/wind/hydro facilities across a state or province — 2–5 operators per site, unattended for 18–22 hours daily.
The challenge: provide secure remote access to all three categories of users, maintain sub-second latency for SCADA operations, document every interaction for NERC auditors, and keep infrastructure costs manageable across low-density remote sites.
Hub-and-Spoke Architecture on OCI
The Thinfinity hub-and-spoke architecture addresses this by centralizing all VDI sessions on OCI and extending low-latency connectivity to remote sites via OCI FastConnect dedicated circuits:
1. Hub (OCI us-phoenix-1 region)
- Thinfinity gateway cluster: 3–5 compute instances (VM.Standard.E5.Flex, 4 OCPUs, 32 GB RAM each) running Thinfinity gateway. Auto-scales from 3 to 8 instances during peak demand (mining shift changes, solar generation monitoring peaks).
- Session recording storage: Oracle Object Storage bucket (trading-sessions-prod) with WORM retention policy: 7-year retention for audit compliance. Cost: ~$180/month for 2,000 sessions × 2 GB each = 4 TB total.
- IAM and logging: OCI IAM managing SCADA engineer roles, miner geologist roles, vendor access. All session metadata (user, timestamp, applications accessed) streamed to OCI Logging and indexed in Splunk.
- Network infrastructure: OCI FastConnect virtual circuit (10 Gbps dedicated private connection) to each remote site. Latency: 15–25 ms between Denver hub and remote mining facility.
2. Spoke 1: Main Mining Facility
- Local network: On-premises SCADA network (10.100.0.0/16) connected to OCI via FastConnect. No internet gateway; all traffic is private.
- SCADA systems: Siemens WinCC SCADA servers, GE iFIX operator workstations, Honeywell Experion DCS for environmental controls. All systems isolated from corporate network by firewall rules (only Thinfinity gateway IP allowed inbound).
- Thinfinity local relay: Optional VM.Standard.A1.Flex instance (2 OCPUs, 12 GB RAM) running Thinfinity relay agent. Caches session recordings locally before sending to OCI (useful during network outages; replay recordings during 2-hour FastConnect downtime if needed). Cost: ~$60/month.
3. Spoke 2–7: Distributed Generation Sites
- Minimal on-premises footprint: Each site has a DCS controller (Honeywell or ABB 800xA) managing local power generation. Unattended most of the time.
- Remote access: Field operators log into Thinfinity hub from the main facility. Latency to DCS: 15–25 ms via FastConnect. No local IT infrastructure.
- Monitoring-only mode: NERC CIP-001 (high-impact) and some CIP-003-9 (low-impact with critical generation) facilities operate in ‘air-gapped monitoring mode’: read-only Thinfinity sessions with data flowing only outbound (no operator input reaching control system). Session recordings provide audit trail.
Compute Sizing by Role
Thinfinity VDI session sizing on OCI depends on the role and application complexity:
| Role / Use Case | VM Sizing | Session Count & Cost Estimate |
|---|---|---|
| SCADA Operator (HMI) | 1 vCPU, 4 GB RAM | GE iFIX, Siemens WinCC, Honeywell HMI (light graphics). 80–120 concurrent sessions per node. Cost: $0.08/hour/session. |
| Control System Engineer | 2 vCPUs, 8 GB RAM | IDE (Visual Studio), PLC programming tools, simulation. 30–50 concurrent sessions per node. Cost: $0.18/hour/session. |
| Mining Geologist / Field Survey | 1 vCPU, 2 GB RAM | Remote desktop for email, mapping tools, reporting. 150–200 concurrent sessions per node. Cost: $0.05/hour/session. |
| Vendor Support Session (VERA) | 2 vCPUs, 8 GB RAM | GE / Siemens / Honeywell service engineer. 20–30 concurrent sessions per node. Cost: $0.18/hour/session. Time-limited to 4 hours. |
For a 200-person operation (80 SCADA, 30 engineers, 60 field staff, 30 seasonal vendors), monthly OCI costs are:
- Compute instances: 8 hub gateways × $600/month = $4,800. 50 concurrency × $100 average session cost = $5,000/month.
- Networking: FastConnect 10 Gbps: $3,000/month. Inter-region replication: $500/month.
- Storage: Object Storage (4 TB sessions): $180/month. Autonomous Data Warehouse (audit logs): $800/month.
- Total monthly cost: ~$14,280/month (~$171,000 annually) vs. traditional architecture (~$280,000 for on-premises VDI servers, 50 engineers to maintain, plus WAN infrastructure). Thinfinity on OCI reduces infrastructure costs by 40%.
Section 5: Vendor Electronic Remote Access (VERA) — Controlled Third-Party Access
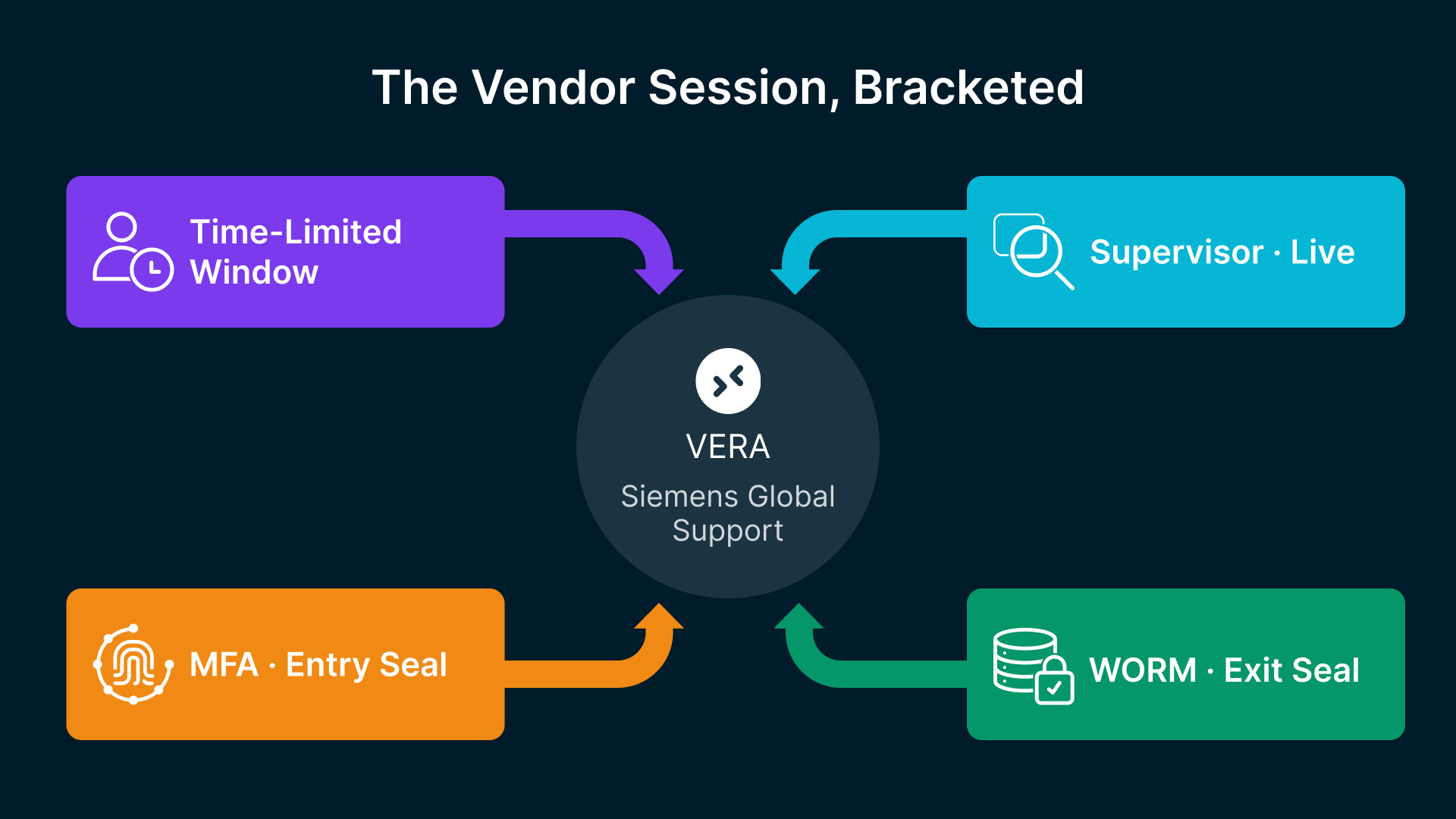
CIP-003-9’s most impactful new requirement is Vendor Electronic Remote Access (VERA) control. When a GE technician remotely accesses your SCADA system to update firmware, or a Siemens engineer troubleshoots a control system failure, NERC now mandates that you control, record, and supervise that session. No longer can vendors get a standing VPN account and log in whenever they want.
VERA Control Requirements
- Time-Limited Access: Vendor sessions are authorized for a specific duration (4 hours for scheduled maintenance, 1 hour for emergency support, 30 minutes for diagnostic inquiry). Thinfinity automatically terminates sessions when the timer expires.
- MFA Enforcement: Vendors authenticate with their own corporate credentials (GE, Siemens) plus a time-based one-time password (TOTP) token. No shared passwords. No ‘support credentials’ passed via email.
- Session Monitoring & Recording: Your SCADA engineer watches the vendor session in real-time on a secondary Thinfinity client. If the vendor deviates from the agreed scope (e.g., starts accessing customer data instead of just the firmware), the engineer can pause or terminate the session immediately.
- Keyboard & Mouse Logging: All keystrokes and mouse movements are recorded. File transfers are logged by source and destination. If a vendor’s session attempts to download your proprietary SCADA configuration or PLC code, the transfer is blocked and logged.
- Forensic Evidence: Session recording is stored in WORM Oracle Object Storage. If the vendor’s actions cause a control system failure, you can replay the session and provide NERC auditors with a forensic artifact proving exactly what the vendor did.
Jump Server Pattern for VERA
The recommended architecture uses a jump server pattern:
Step 1: Vendor Requests Access
GE field engineer opens a support ticket: ‘Need to update firmware on your Profibe gateway in the Denver mining control center. Request 2-hour access window on Tuesday 3–5 PM MST.’
Step 2: SCADA Manager Approves
Your SCADA manager (or delegated technician) logs into OCI IAM and creates a temporary VERA token valid for 2 hours on Tuesday 3–5 PM. The token is sent to GE via encrypted email (AES-256, no plaintext passwords).
Step 3: Vendor Authenticates & Supervisor Watches
At Tuesday 3 PM, the GE engineer pastes the VERA token into the Thinfinity gateway. Thinfinity validates the token, creates a session, and notifies your SCADA supervisor. The supervisor logs into a second Thinfinity session with ‘observer’ role and watches in real-time. The GE engineer’s mouse, keyboard, and screen are visible to the supervisor.
Step 4: Work Performed & Session Recording
GE engineer connects to the Profibe gateway, uploads firmware version 4.2.1, validates device reboot, and disconnects. Session recording captures: keystrokes, screen output, file transfer details (firmware filename, checksum, size), commands executed, and timestamps. At 5 PM, Thinfinity auto-terminates the session. Recording is sent to Oracle Object Storage with WORM protection.
Step 5: Audit Trail & Incident Investigation
24 hours later, the Profibe gateway fails. Your SCADA team logs into OCI Object Storage, locates the VERA session recording from Step 4, and replays it. Evidence: The firmware upload succeeded, device rebooted cleanly, and no errors occurred during the session. Either the device failed after the vendor disconnected (not the vendor’s fault), or the firmware itself has a bug. You provide this forensic artifact to GE’s support team and to NERC auditors, proving your organization’s due diligence in vendor oversight.
This level of control is non-negotiable under CIP-003-9 R2 and was the primary driver of the standard update. NERC auditors specifically request VERA session recordings; without them, your facility fails CIP-003-9 R2 automatically.
Section 6: Advanced Compliance Topics — Forensics, SRAS, and Evidence Collection
NERC Audit Readiness: Evidence Collection for Inspectors
NERC conducts triennial audits of registered Functional Model Entities (FMEs). Auditors examine:
- Cyber Security Plan Compliance: Is your plan documented, approved, and signed? Does it address all CIP-005-7, CIP-007-7, CIP-009-7 requirements? Is it reviewed and updated annually?
- Electronic Access Control Logs: Provide MFA authentication logs for the past 24 months. NERC samples 30–50 sessions and validates that each session has: (1) timestamp, (2) user identity, (3) MFA token used, (4) session duration, (5) systems accessed. Missing any element = violation.
- Session Recording Evidence: NERC inspectors request 5–10 random session recordings and review them for completeness: Are all keystrokes captured? Is screen output clear? Are file transfers logged? Does the recording have tamper-proof timestamps?
- Remote Access Perimeter Documentation: Firewall rules, network ACLs, and security group configurations showing that SCADA systems are isolated from the internet and corporate networks, accessible only via the Thinfinity gateway.
- Patch Management Records: Proof that all low-impact BES cyber systems have been patched within 365 days of patch release (or documented as risk-accepted if delay is justified).
Thinfinity and OCI automate this evidence collection:
- Cyber Security Plan Module: Thinfinity’s documentation generator creates an audit-ready cyber security plan document (20–30 pages) populated with your actual configuration: MFA policy, session recording retention, VERA procedures, incident response contact info. Output is formatted to NERC audit templates.
- OCI Audit Logs API: All OCI actions (IAM policy updates, compute instance launches, Object Storage bucket configuration) are logged in OCI Audit (formerly Cloud Guard). Export these logs as evidence of infrastructure hardening and compliance controls.
- Session Recording Reports: Thinfinity dashboard generates reports: ‘Total sessions recorded: 4,500 in Q1 2026. Average session duration: 45 minutes. VERA sessions: 87 (all completed within time limits). Recording storage: 4.2 TB (zero deletions or overwrites—WORM integrity verified).’ This report satisfies NERC’s evidence collection requirements.
Synchronous Remedial Action Schemes (SRAS) and NERC CIP-001 High-Impact Assets
For energy companies operating transmission facilities classified as ‘medium’ or ‘high’ impact under NERC CIP-001, Synchronous Remedial Action Schemes (SRAS) introduce additional complexity. SRAS are automated, network-triggered actions (e.g., ‘if frequency drops below 59.5 Hz, shed 500 MW of load within 200 milliseconds’). These schemes require sub-second latency, deterministic control, and zero packet loss.
Thinfinity’s hub-and-spoke architecture supports SRAS by:
- Low-Latency SCADA Tunnels: OCI FastConnect provides sub-5ms latency from Thinfinity gateway to SCADA controllers. SRAS schemes can trigger at this latency.
- Dedicated Circuit Reservation: FastConnect allows QoS (Quality of Service) policies ensuring that SRAS traffic never gets blocked by heavy session recording traffic or operator file transfers.
- Session Recording Isolation: Recording streams are sent through separate network paths (different vNIC on OCI compute instances), ensuring SRAS traffic is never contended by recording overhead.
- Audit Trail for Forensic Analysis: If an SRAS triggers, session recordings from the preceding 5 minutes provide context: What operator actions, network events, or system alarms preceded the SRAS trigger? This evidence is invaluable for post-incident analysis and regulatory investigation.
Historical Data Preservation for Forensic Investigation
Mining and energy operators often encounter incidents weeks or months after they occur: ‘We discovered yesterday that someone accessed the DCS controller on March 15. Who accessed it? What did they do?’ Without historical data, incident investigation is impossible. Thinfinity preserves this data through:
- 7-Year WORM Retention: All session recordings are stored in Oracle Object Storage with WORM retention for 7 years (per NERC CIP-009-7 incident retention requirements). You can query any session from 2019 onwards.
- Session Metadata Index: OCI Autonomous Data Warehouse indexes session metadata (user, timestamp, applications accessed, files transferred). Queries like ‘Show me all sessions by user SMITH between Jan 1 and March 31, 2026 where they accessed SCADA’ return results in milliseconds.
- Blockchain-Style Chain of Evidence: Each session recording is cryptographically signed by Oracle’s HSM. The signature proves the recording has not been altered, modified, or tampered with since capture. This evidence chain is critical for litigation, regulatory investigation, and incident remediation.
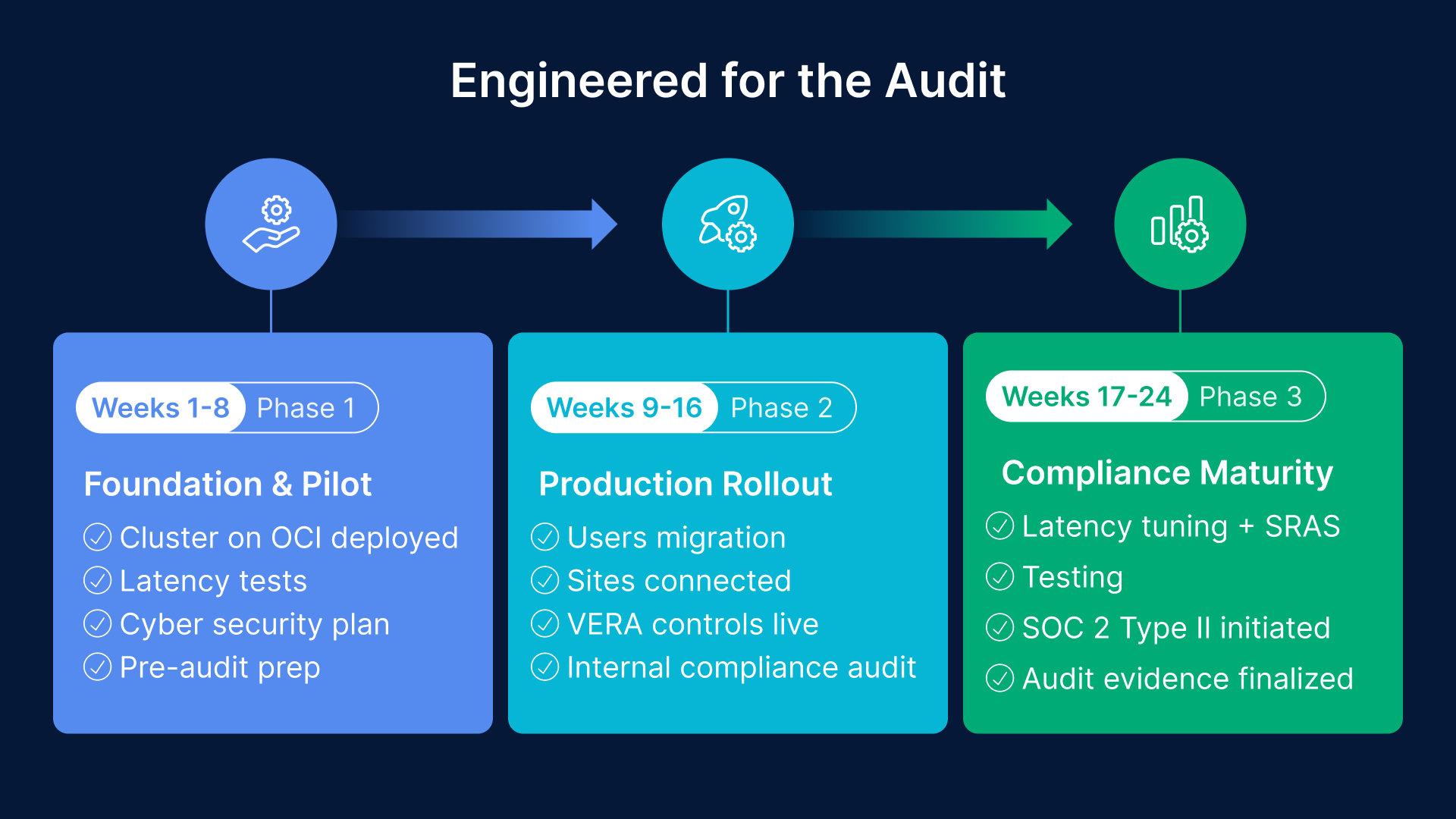
Section 7: 24-Week Deployment Roadmap — NERC Compliance by June 2026}
With NERC CIP-003-9 taking effect April 1, 2026, and NERC audits beginning in Q2 2026, time is critical. This 24-week roadmap (8 weeks to full production, 16 weeks to full compliance maturity) ensures you are NERC-ready by June 1, 2026.
Phase 1: Foundation & Pilot (Weeks 1–8)
- Week 1–2: Requirements Gathering & OCI Account Setup. Meet with SCADA engineers, compliance, and procurement. Define SCADA system inventory, document remote access points, and identify low-impact BES assets that fall under CIP-003-9. Create OCI account, subscribe to FastConnect circuits for main facility and 3–4 remote sites. Estimated cost: $5,000 (FastConnect setup).
- Week 3–4: Thinfinity Gateway Deployment on OCI. Deploy Thinfinity cluster on OCI us-phoenix-1: 3 compute instances (VM.Standard.E5.Flex, 4 OCPUs, 32 GB each). Configure OKTA / Azure AD for MFA. Set up Oracle Object Storage bucket for session recording with WORM retention (7-year policy). Configure OCI IAM roles for SCADA engineer, operator, and vendor access levels. Estimated cost: $2,500.
- Week 5–6: Pilot Testing with 20 SCADA Engineers. Recruit a pilot group of 20 engineers from your main mining facility. Provide 4 hours of training on Thinfinity client authentication, basic session operations, and reporting. Test latency: measure p50, p95, p99 latencies from Denver hub to mining site SCADA via FastConnect. Target: <25 ms p99 latency. Collect feedback on usability, performance, and SCADA application compatibility (GE iFIX, Siemens WinCC, Honeywell Experion). Estimated cost: $1,000 (training, consulting).
- Week 7–8: Compliance Documentation & Audit Preparation. Work with OCI solutions architect to document compliance posture: cyber security plan, MFA policy, VERA procedures, incident response plan. Generate Thinfinity audit reports (session recording statistics, MFA logs, VERA session recordings). Schedule pre-audit consultation with NERC compliance partner (Deloitte, CohnReznick, or equivalent). Prepare evidence package for Q2 2026 NERC audit. Estimated cost: $3,000 (consulting).
Phase 1 Deliverables: Fully functional Thinfinity VDI environment on OCI, pilot user group with positive feedback, documented cyber security plan, initial audit evidence package. Infrastructure cost: ~$8,500. Time investment: 4 FTE-weeks.
Phase 2: Production Rollout (Weeks 9–16)
- Week 9–10: Capacity Planning & Infrastructure Scaling. Based on pilot feedback, size production cluster. Expected user base: 80 SCADA engineers + 30 field operators + 30 seasonal vendors = 140 concurrent users. Compute: 8 hub gateway instances. Auto-scaling configured to add instances when CPU >70%. Multi-region failover: replicate Thinfinity configuration to OCI us-ashburn-1 (Virginia) for US East Coast presence. Estimated cost: $5,000.
- Week 11–12: Production Rollout Wave 1 (100 SCADA Engineers). Migrate main mining facility SCADA team to Thinfinity. Deploy local Thinfinity relay agent on-premises for session recording cache. Integrate with main facility’s SCADA network (firewall rules, network ACLs, FastConnect circuit validation). Monitor performance: latency, session stability, recording completeness. Conduct daily standup with SCADA team to address issues. Estimated cost: $2,000 (infrastructure, support).
- Week 13–14: Rollout Wave 2 (Distributed Generation Sites + Field Operations). Connect all 6–15 distributed generation sites to Thinfinity hub via FastConnect. Deploy VERA controls for vendor access: create VERA approval workflow, train site supervisors on vendor session monitoring. Migrate field operations team (geologists, surveying crew) to Thinfinity VDI for remote email, mapping tools, and reporting. Test emergency failover: simulate FastConnect circuit outage, validate 2-hour recovery plan. Estimated cost: $3,000.
- Week 15–16: Compliance Validation & NERC Readiness. Conduct internal audit of all Thinfinity sessions and configurations. Validate: (1) All SCADA systems are behind Thinfinity firewall (zero direct access from internet). (2) MFA is enforced for 100% of sessions. (3) Session recordings are being written to WORM storage (spot-check 20 random recordings). (4) VERA vendor sessions are complete and recorded. (5) Patch management logs show no critical vulnerabilities. Prepare formal audit evidence package for NERC (cyber security plan, control mapping, session recording samples). Estimated cost: $2,000.
Phase 2 Deliverables: Full production Thinfinity environment with 140+ concurrent users, all SCADA and field teams migrated, NERC CIP-003-9 controls validated, audit-ready evidence package. Infrastructure cost: ~$12,000. Time investment: 6 FTE-weeks.
Phase 3: Compliance Maturity & Optimization (Weeks 17–24)
- Week 17–18: Latency Optimization & Performance Tuning. Review latency benchmarks from Phases 1–2. Identify any sites or user groups experiencing >30 ms latency. Work with OCI FastConnect team to optimize circuit placement, dedicate bandwidth to critical SCADA traffic, and enable QoS policies. For high-impact facilities with SRAS (Synchronous Remedial Action Schemes), ensure sub-5ms latency via placement groups and dedicated instances. Estimated cost: $1,500 (OCI optimization consulting).
- Week 19–20: Advanced Compliance Features. Enable insider threat detection in Thinfinity: flag unusual access patterns (access outside normal shift hours, access to unexpected SCADA systems, rapid clipboard copies). Integrate with Splunk for real-time alerting. Test air-gapped read-only mode for high-impact BES facilities: operators can view SCADA screens but not send commands (data flows outbound only, no inbound control signals). Document these controls in compliance audit trail. Estimated cost: $1,000.
- Week 21–22: Penetration Testing & SOC 2 Audit. Hire independent security firm (Mandiant, CrowdStrike, or equivalent) to conduct penetration testing of Thinfinity gateway and OCI infrastructure. Test: Can an attacker gain access to Thinfinity sessions without valid credentials? Can an attacker modify session recordings stored in WORM bucket (should fail)? Can lateral movement occur between SCADA systems (should be blocked by network ACLs)? Remediate any findings. Simultaneously, begin SOC 2 Type II audit of Thinfinity + OCI deployment; requires 6 months of operational data, so initiate now. Estimated cost: $8,000.
- Week 23–24: NERC Audit Preparation & Post-Go-Live Optimization. Final audit evidence package: compile all session recording statistics, MFA logs, VERA recordings, patch management records, and incident response documentation. Schedule formal NERC audit for Q2 2026 (NERC typically provides 30-day notice). Conduct post-go-live retrospective: gather feedback from SCADA engineers, operators, and field teams. Identify process improvements (e.g., faster VERA approval workflow, better session search tools). Plan for ongoing operational excellence (monthly patching, quarterly security reviews, annual compliance certification). Estimated cost: $2,000.
Phase 3 Deliverables: Optimized, hardened, and audit-ready Thinfinity environment. Full SOC 2 compliance roadmap initiated. NERC CIP-003-9 demonstrated through independent testing and forensic evidence. Infrastructure cost: ~$12,500 total for Phase 3. Time investment: 6 FTE-weeks.
Total 24-Week Cost Estimate:
- Phase 1 (Foundation): $8,500
- Phase 2 (Production): $12,000
- Phase 3 (Maturity): $12,500
- Ongoing Monthly OCI Cost: $14,280 (compute, networking, storage, logging)
- Total 24-week capital cost: $33,000. Ongoing annual cost: $171,360.
Section 8: Real-World Operational Scenarios
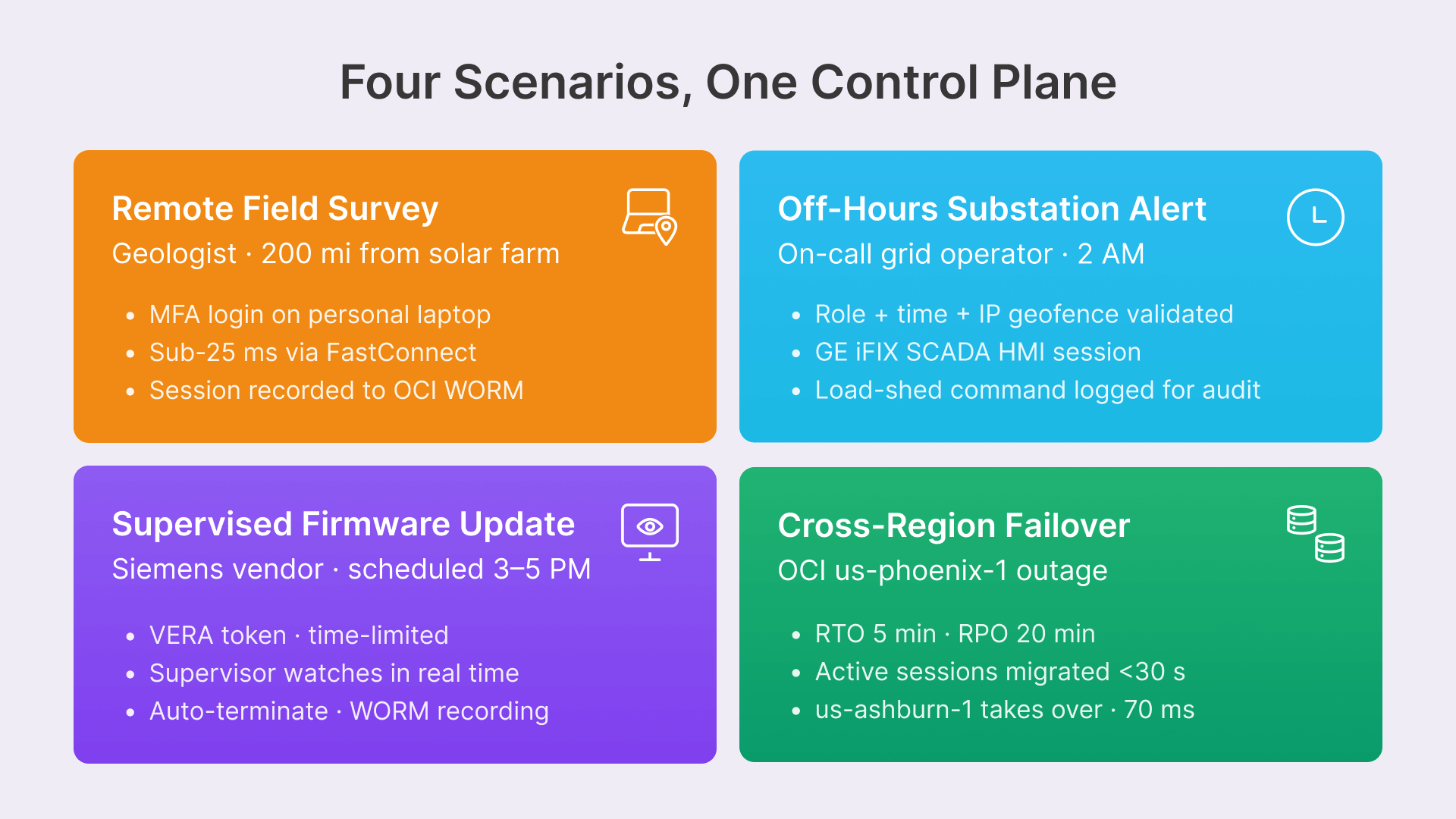
Four scenarios demonstrate how Thinfinity VDI handles typical mining and energy operations while maintaining NERC compliance:
Scenario 1: Remote Geologist Surveys a Solar Farm 200 Miles Away
Context: Your company operates a 50 MW solar farm in rural Nevada. A geologist needs to visit the site, inspect panels for degradation, and update field notes. The site has a DCS controller managing inverters and grid interconnection.
Traditional approach: Geologist takes a laptop to the site, connects via cellular hotspot (unreliable), attempts to access company email and mapping software over slow connection.
Thinfinity approach:
- The geologist logs into Thinfinity on her laptop using MFA (authenticates with her corporate Azure AD credentials + TOTP token).: Connection is established to the Thinfinity hub in Denver (sub-25 ms latency via FastConnect).
- Thinfinity launches a lightweight VDI session (1 vCPU, 2 GB RAM) running RHEL desktop, ArcGIS Pro (mapping software), and Slack.: All applications run on OCI, not on the geologist’s laptop. The laptop is just a thin HTML5 browser—no sensitive data is stored locally.
- The geologist accesses her company email, views high-resolution geological survey maps (500 MB files), and updates field notes in a shared OneDrive folder.: All network traffic flows through the Thinfinity tunnel, encrypted and logged. Even if her cellular connection is intercepted, attackers cannot access company data or credentials (stored only on OCI).
- For compliance: The entire session is recorded to Oracle Object Storage (1.2 hours × 45 Mbps video = 300 MB recording). Metadata: ‘GEOLOGIST-A’, ‘2026-03-31 08:00–09:12 UTC’, ‘accessed: email, mapping tools, OneDrive’. This recording satisfies NERC CIP-005-7 R2 evidence requirement for remote work auditing.:
Scenario 2: SCADA Grid Operator Monitors 6 Substations from Home During Off-Hours
Context: Your company operates 6 distribution substations in Colorado and Utah. An on-call SCADA operator receives an alert at 2 AM: ‘Substation-4 frequency dropping.’ She needs to investigate immediately from her home.
Thinfinity approach:
- Operator opens Thinfinity client on her home laptop, authenticates with MFA (corporate username + TOTP).: Thinfinity validates: (1) Her role is ‘grid operator’ (IAM policy allows access); (2) Time is 2 AM (her on-call schedule permits access); (3) Source IP is her home (registered in IAM geofence list).
- Session is created: 2 vCPU, 8 GB RAM compute instance on OCI running GE iFIX SCADA HMI and monitoring dashboards.: She can see real-time grid frequency, voltage, reactive power across all 6 substations. Latency: 12 ms from her home (via residential internet) to OCI hub.
- Substation-4 frequency is confirmed at 59.2 Hz (too low). She manually commands a 100 MW load shedding action.: The command flows through Thinfinity to the DCS controller at Substation-4. DCS executes the load shed; frequency recovers to 60.0 Hz.
- For compliance: The entire session is recorded—her authentication, her monitoring of the 6 substations, her load shedding command, and the DCS response. NERC auditors can replay the 15-minute session and confirm: (1) Operator was properly authenticated; (2) Her actions were appropriate for the grid condition; (3) The command was successfully executed. This forensic artifact satisfies CIP-009-7 (incident management) documentation requirements.:
Scenario 3: Siemens Vendor Updates SCADA Firmware During Scheduled Maintenance Window
Context: Your main mining facility’s Siemens SCADA controller (WinCC version 7.5) needs firmware update to 8.0. Siemens field engineer will remotely perform the update on Tuesday 3–5 PM EST.
Traditional approach: IT grants Siemens a VPN account with standing credentials. Engineer logs in Tuesday and performs the update. No supervision, no recording, no audit trail.
Thinfinity VERA approach:
- Your IT manager approves the update and creates a VERA token in OCI IAM, valid only for Tuesday 3–5 PM EST, scoped to the Siemens engineer’s account, with access limited to WinCC controller IP.: Token is sent to Siemens via encrypted email.
- Tuesday 3 PM: Siemens engineer pastes the VERA token into Thinfinity client. Thinfinity validates the token (correct user, correct time window, correct scope).: Session is created: 2 vCPU, 8 GB VM running a hardened RHEL desktop with SSH and SCP (secure copy) tools only. No web browser, no email, no terminal access.
- Your SCADA supervisor logs into a second Thinfinity session as ‘observer’ role. The supervisor can view the engineer’s screen and keyboard input in real-time but cannot interact.: The engineer uploads firmware file (300 MB) via SCP. Transfer is logged: ‘firmware-8.0-release.tar.gz’, checksum, timestamp. The engineer executes the WinCC upgrade script. Screen shows: ‘Upgrade starting… 5% complete… 50%… 100% complete. Services restarted successfully.’
- At 5 PM, Thinfinity auto-terminates the VERA session. No manual disconnection required; token expires automatically.: Session recording (2 hours, 750 MB) is sent to Oracle Object Storage with WORM protection.
- For compliance: When NERC auditors ask, ‘Describe how you supervise vendor access,’ you show the VERA session recording, the supervisor’s monitoring logs, and the MFA token validation. Evidence is irrefutable: the vendor accessed only the WinCC controller, made changes only to the firmware version, and was observed and recorded throughout. If the firmware update causes a failure 48 hours later, you can replay the recording and determine whether the failure was due to the vendor’s actions or a pre-existing system issue.:
Scenario 4: Emergency Failover to Secondary OCI Region After Primary Region Network Outage
Context: OCI us-phoenix-1 region (primary Thinfinity hub) experiences a major network outage affecting FastConnect circuits. Your mining operations have a 20-minute RPO (recovery point objective). Backup site in OCI us-ashburn-1 (Virginia) is pre-configured and on standby.
Thinfinity approach:
- OCI monitoring detects: FastConnect latency exceeds 500 ms (normal: 15 ms). Within 2 minutes, automated failover is triggered.: Thinfinity DNS entries are updated: thinfinity.company.com now resolves to us-ashburn-1 load balancer instead of us-phoenix-1.
- SCADA operators’ active sessions are NOT interrupted. Thinfinity implements session migration: active sessions on us-phoenix-1 instances are gracefully migrated to us-ashburn-1 instances. Migration takes <30 seconds; operator experiences only a brief network hiccup, then resumes work.:
- Newly authenticating users (new sessions) connect directly to us-ashburn-1. Latency increases to 70 ms (transcontinental), but SCADA monitoring remains functional.: Critical DCS controllers are accessed via the backup region; command latency increases to 70 ms, but this is still acceptable for DCS operations (typical polling interval is 500+ ms).
- Session recordings continue: us-ashburn-1 sessions are recorded to its local Oracle Object Storage bucket. If the outage lasts >2 hours and primary region is still unavailable, recordings are replicated asynchronously to us-phoenix-1 (eventual consistency).:
- For compliance: RTO (recovery time objective) = 5 minutes (automated failover). RPO = 20 minutes (session data loss acceptable; mining operators accept brief recording gaps during disasters). NERC CIP-009-7 (incident management) requires documented recovery procedures; this automated failover is documented and tested quarterly via disaster recovery drills.:
This article focuses on NERC CIP compliance architecture. For the complete ROC deployment playbook — including SCADA/DCS integration patterns for GE iFIX, Siemens WinCC, and Honeywell Experion; satellite bandwidth optimization; 5-year TCO models for 500 and 2,000-endpoint operations; and a 24-week phased rollout plan — read: “Remote Operations Center VDI: How Mining and Energy Companies Are Replacing Ruggedized Endpoints with Browser-Based Desktops on OCI.”
Frequently Asked Questions
What exactly changes on April 1, 2026? Do I need to comply immediately?
Yes. NERC CIP-003-9 takes effect April 1, 2026, and any low-impact BES facility (including distributed energy resources over 25 MW) must begin compliance immediately. NERC audits begin in Q2 2026, giving you roughly 9 weeks from April 1 to June 1 to demonstrate compliance. Thinfinity VDI deployment runs 8–12 weeks; starting in March 2026 is the minimum to be ready.
Is VDI mandatory for NERC CIP-003-9 compliance, or are there alternatives?
VDI is not explicitly mandated, but it is the most comprehensive solution for CIP-005-7 R2 (remote access management) and CIP-003-9 R2 (VERA control). Alternatives like air-gapped networks, jump servers with SSH tunneling, or industrial remote access appliances (Fortinet, Palo Alto) lack the session recording, audit trail, and supervisor monitoring capabilities NERC auditors specifically request. Thinfinity is audit-optimized; it was built with NERC compliance as a core design principle.
How does Thinfinity VDI guarantee that session recordings cannot be deleted or tampered with?
Thinfinity streams sessions to Oracle Object Storage buckets configured with WORM (Write-Once-Read-Many) retention policies, enforced at the OCI API level — no API call, administrative override, or credential compromise can modify or delete a WORM-protected object. The bucket configuration itself is immutable and cannot be disabled without OCI support intervention. Sessions are also cryptographically signed by Oracle’s HSM, creating a chain of custody whose deletion would require breaking AES-256.
Can Thinfinity VDI work with legacy SCADA equipment (15+ years old) that doesn't support modern protocols?
Yes. The operator’s laptop connects to Thinfinity, and Thinfinity tunnels to the SCADA system using whatever protocol it supports — Modbus, Profibus, OPC, Modbus TCP, or older serial protocols via serial-over-TCP adapters. The legacy SCADA system sees the Thinfinity gateway as just another workstation; no firmware updates or configuration changes required. This is critical for mining and energy operators who cannot afford to replace 20-year-old DCS systems.
What are the latency implications of VDI? Will monitoring SCADA from 200 miles away add unacceptable lag?
With OCI FastConnect (10 Gbps dedicated private circuit), latency from Thinfinity hub to remote SCADA is 15–25 ms (vs. 40–80 ms on VPN) — acceptable for SCADA monitoring and control given typical polling intervals of 500+ ms. For Synchronous Remedial Action Schemes (SRAS) requiring sub-100 ms response, FastConnect with placement groups delivers <5 ms latency. Fiber propagation over 200 miles introduces ~1 ms; Thinfinity adds 15–25 ms, well within SCADA tolerances.
How are MFA tokens managed? If a SCADA engineer loses her TOTP authenticator device, how does she regain access?
MFA token management is handled by your Identity Provider (Azure AD, Okta, Ping Identity). If an engineer loses her TOTP device, IT issues a new one via the IdP’s self-service portal or admin override; recovery codes generated during initial MFA setup should be stored securely. Emergency access requires a temporary 4-hour token issued by your CISO with dual approval, fully logged and audited. NERC auditors review MFA recovery procedures, so a documented dual-approval process satisfies CIP-003-9 R2.
For air-gapped, high-impact facilities (nuclear plants, critical transmission hubs), can Thinfinity operate in read-only mode?
Yes. Thinfinity supports ‘monitoring-only’ sessions where operators can view SCADA screens and system data but cannot send commands or input keystrokes. Data flows outward via a data diode (hardware-enforced unidirectional network device), so no operator input ever reaches the control system — satisfying NERC CIP-001 (high-impact) air-gap requirements. Session recordings still capture screen output and operator mouse movements for behavioral analytics.
What is the estimated cost to deploy Thinfinity VDI on OCI for a 200-person mining/energy operation?
Capital costs for the 24-week deployment run ~$33,000 (infrastructure, FastConnect, license, consulting, testing); ongoing OCI costs are ~$14,280/month or ~$171,360 annually. 3-year total cost of ownership: ~$546,000. Compared to traditional on-premises VDI ($280K servers + 5 FTE × $120K + $24K WAN annually = ~$1.384M over 3 years), Thinfinity on OCI is 60% cheaper long-term and audit-ready.