The 40-Site Dilemma
You sit in the CTO chair at a mining company with 40 remote sites spread across three countries: Australia, Chile, and Indonesia. Each site runs 15–50 workstations — ruggedized Panasonic Toughbooks, Dell Latitude Ruggeds, fixed Advantech industrial PCs — running GE iFIX, Siemens WinCC, OSIsoft PI systems, and custom fleet management tools. Your hardware refresh cycle is 2.5 years because dust, vibration, and 45°C ambient temperatures destroy consumer-grade hardware in 18 months. Last quarter, two sites went offline because motherboards failed in heat. Your IT team flew emergency replacement units via helicopter at $18,000 per trip.
This is not anomaly. This is Tuesday.
The hidden IT crisis at the edge — mining sites, oil platforms, substations, remote data centers — is costing organizations hundreds of millions of dollars annually. Not in obvious ways. Not in a single ransomware incident or downtime event. But in the relentless mathematics of distributed infrastructure: ruggedized hardware replacement, logistics, downtime penalties, shadow IT, cyber insurance premiums, and the compliance penalties nobody calculates until an audit team shows up with NERC CIP-003-9 citations in hand.
Section 1: The Scale Problem — Distributed Endpoints at Industrial Cost
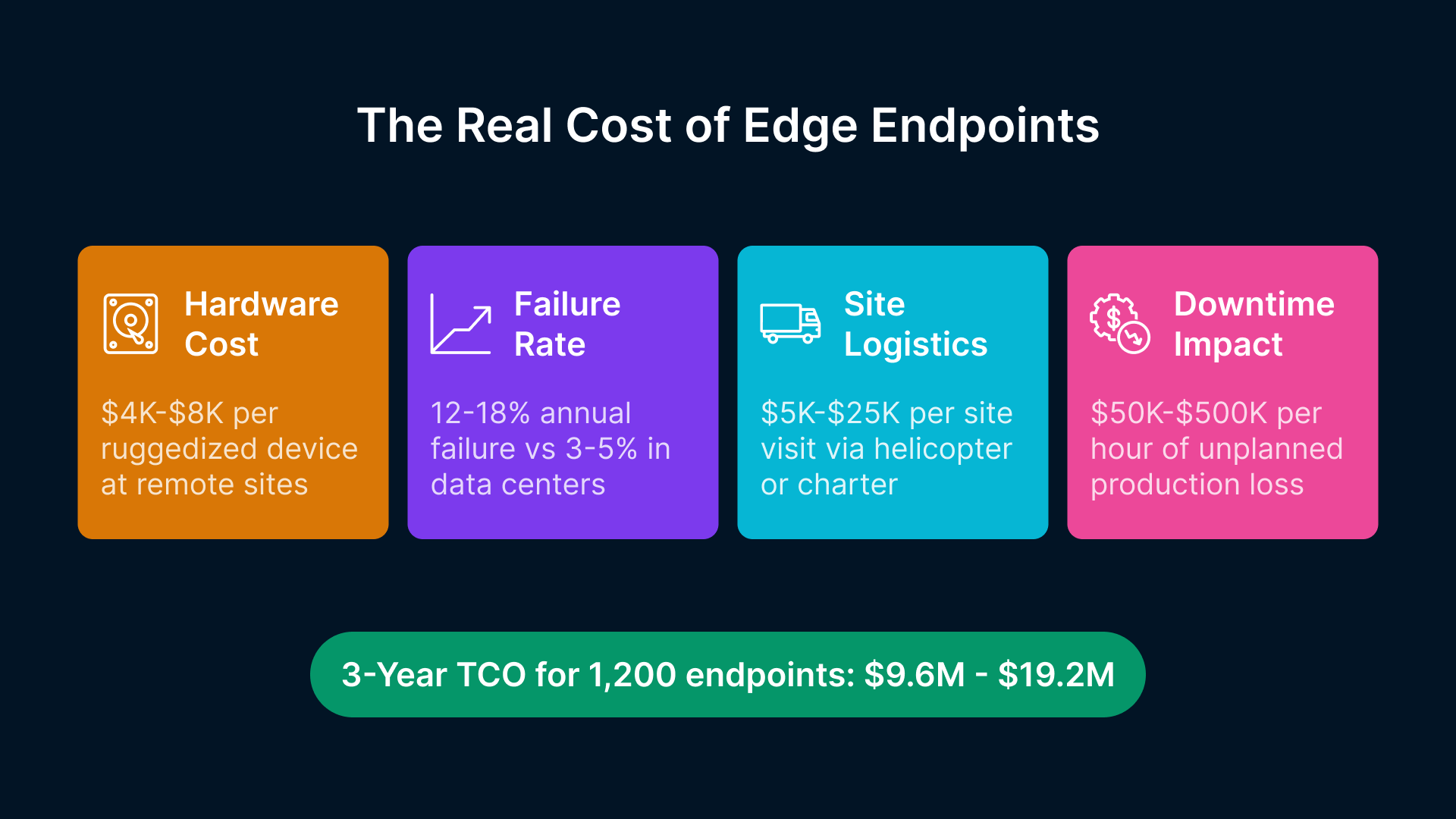
Let’s talk numbers. Mining and energy operators manage remote equipment at a scale that corporate IT has never faced. A single large mining operation (Rio Tinto, BHP, Newmont) runs 30–80 remote sites globally. Each site is not a single workstation — it’s a cluster: dispatcher, equipment monitoring, fleet management, environmental sensors, SCADA HMI terminals, backup redundancy. You’re looking at 15–50 endpoints per site. Do the math: 40 sites × 30 endpoints = 1,200 devices, minimum.
Now consider the hardware economics.
- Ruggedized hardware costs 5–10x more than consumer-grade equivalents: $4,000–$8,000 per rugged laptop or industrial PC vs. $800–$1,200 for a standard Dell or Lenovo.
- Failure rates at remote sites are 12–18% annually (vs. 3–5% in climate-controlled corporate data centers). Dust ingress, thermal cycling, humidity, vibration — these are not edge cases; they are the normal operating environment.
- Replacement logistics dominate the cost. Helicopter charter flights to a mining site in Western Australia cost $5,000–$25,000. Commercial flights to remote offshore platforms can exceed $15,000 per trip. An emergency motherboard replacement that costs $400 in parts becomes a $20,000 logistics event.
- Downtime is catastrophic. A mining operation loses $50,000–$500,000 per hour of unplanned downtime (depending on ore grade and equipment utilization). An electrical substation or renewable energy facility loses $100,000+ per hour. Your IT team spending 6 hours troubleshooting a failed Panasonic Toughbook costs more than replacing it.
Total 3-year TCO for 1,200 ruggedized endpoints: $9.6 million to $19.2 million. Now add replacement cycles, logistics, downtime penalties, IT travel time (your senior technician burns 10–15% of their year on site visits), and the emerging cost nobody accounts for: cyber insurance premiums rising 30–50% annually due to OT/IT convergence risk.
Section 2: From Bunker SCADA to Remote Operations Centers — The Catch
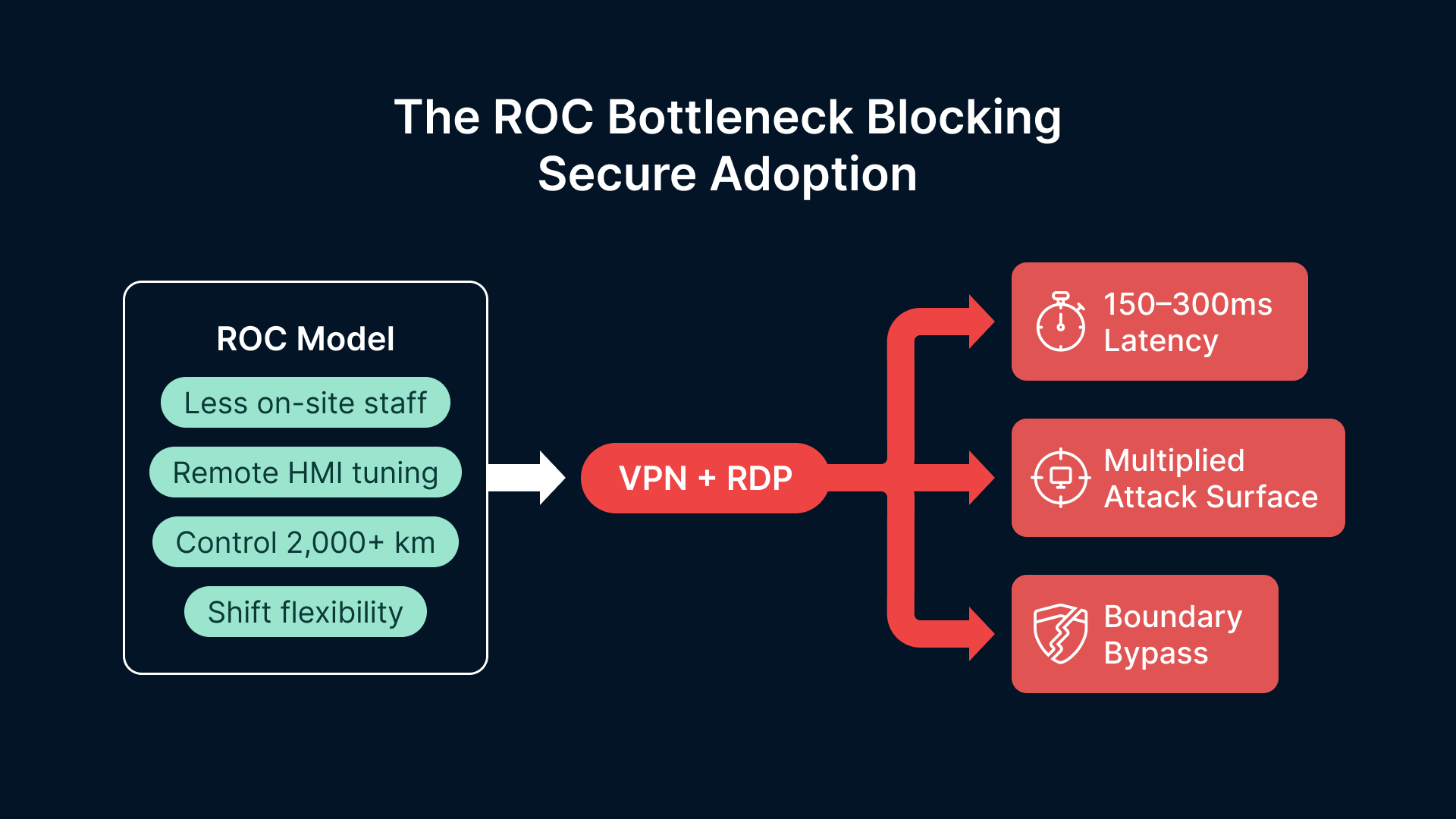
The industry is moving. Rio Tinto’s Operations Centre in Perth consolidates live control of Australian mining sites from a secure facility 2,000+ kilometers away. BHP integrated remote operations across multiple commodities (iron ore, copper, coal) into centralized control rooms in Brisbane and Houston. Newmont, Barrick, Fortescue — all pursuing the same Remote Operations Center (ROC) model. McKinsey data shows 60% of tier-1 mining operators have deployed or piloted ROCs in the past 18 months.
The ROC model is economically compelling. You reduce on-site staffing, improve shift flexibility, standardize training, and concentrate your best operators in a single location. You also reduce site downtime: remote dispatch, remote HMI tuning, remote firmware updates — all without flying a technician to a mine in Papua New Guinea.
But here is the critical constraint: ROCs require secure, low-latency access to distributed SCADA and DCS systems. ‘Secure’ means compliance with NERC CIP-003-9 (as of April 1, 2026), CIP-005-7 (boundary protection), and ISA/IEC 62443 (industrial automation security). ‘Low-latency’ means sub-100ms response times for HMI control loops, not 500ms latency from VPN packet loss and RDP compression.
Current remote access infrastructure fails both tests. Here’s why:
- VPN + RDP: The industry standard (Fortinet FortiGate, Cisco AnyConnect stacked with RDP) introduces 150–300ms latency due to encryption overhead and terminal server serialization. SCADA control loops require <100ms.
- Session multiplexing: A remote operator needs simultaneous access to 5–10 HMI systems across different sites. VPN + RDP forces multiple connections, each with its own authentication, encryption tunnel, and session state. You multiply the attack surface and the latency.
- Compliance gaps: NERC CIP-005 requires boundary protection (firewall rules, ACLs), but VPN bypasses the boundary entirely — the remote operator gets direct Layer 2 access to the industrial network. ISA 62443 requires session isolation, MFA per session, and encrypted audit logs. Standard RDP does not enforce this.
This is not a technical complaint. This is a regulatory problem. An audit by a certified NERC compliance auditor will cite your current VPN/RDP setup for non-compliance with CIP-005-7 (Boundary Protection) and CIP-009-6 (Configuration Management). And as of April 1, 2026, you have no grace period.
Section 3: The OT/IT Convergence Security Crisis — Three Industrial Ransomware Groups Per Day
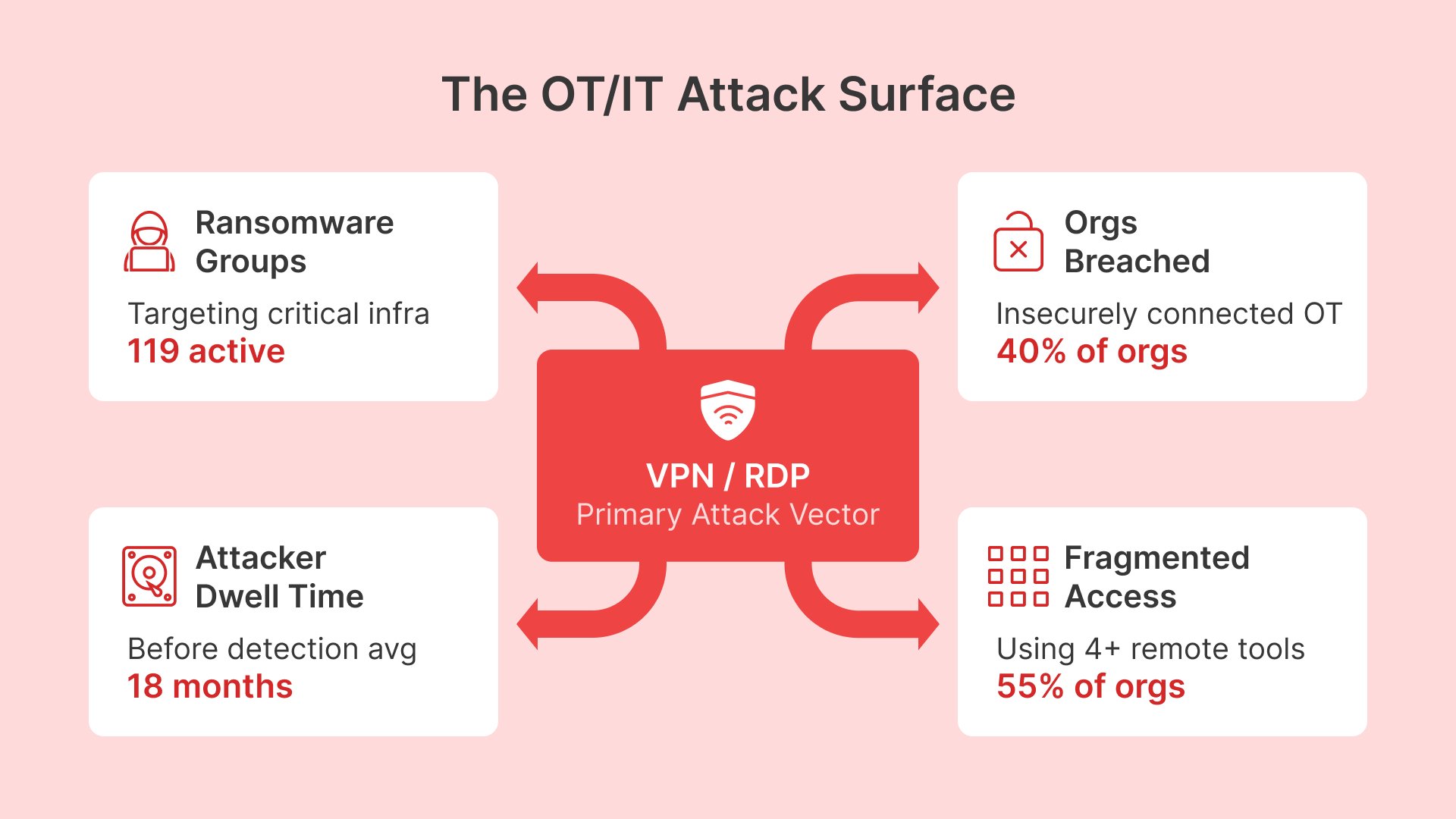
The Dragos 2026 OT/ICS Cybersecurity Report quantifies what security teams have been warning about for two years: OT/IT convergence is a ransomware accelerant.
- 119 active ransomware groups with demonstrated capability against industrial targets.
- 3,300+ documented ransomware incidents targeting critical infrastructure (mining, oil & gas, utilities, renewable) impacting industrial organizations globally — a 49% year-over-year surge.
- 40% of organizations with insecurely connected OT reported intrusions in the past 18 months. ‘Insecurely connected’ means VPN/RDP without encrypted audit logging, MFA per session, or DCS boundary isolation.
- 55% of organizations with distributed SCADA use 4 or more remote access tools (VPN + RDP + TeamViewer + custom SSH scripts). Fragmented tooling means fragmented auditing, fragmented credential management, fragmented zero-trust enforcement.
The threat landscape in 2025 reached a new level of maturity. Adversaries are mapping how control systems work, understanding where commands originate, how they propagate, and where physical effects can be induced.
State-aligned threat actors (Volt Typhoon, Gamaredon, Sandworm) are actively mapping control loops and learning site topology. One January 2025 intrusion into a US electrical utility (not public, but confirmed by CISA) revealed that attackers had spent 18 months mapping SCADA relay logic before deploying a wiper malware. The attack failed due to network segmentation, but the dwell time is instructive: your remote access infrastructure is the reconnaissance vector.
Why? Because your remote access tools are the path of least resistance into OT networks. A VPN endpoint is exposed to the internet. RDP is a known-vulnerable protocol (every Windows RDP server in the world gets scanned hourly). An attacker with credentials (phished, purchased, or dumped from a corporate SaaS breach) can tunnel through your VPN, hop to an RDP server at a remote site, and then pivot to the DCS network. By the time your OT team realizes there’s traffic on the DCS network, the attacker is already inside the boundary.
Dragos 2026 Data: 3,300+ Industrial Ransomware Incidents
119 active ransomware groups, 40% of insecurely-connected OT organizations breached, 55% using 4+ remote access tools. Your current VPN/RDP setup is the entry vector. Session-based MFA and browser-native access eliminate the attack surface.
Section 4: Compliance Escalation — April 1, 2026 Deadline and Expanding Impact
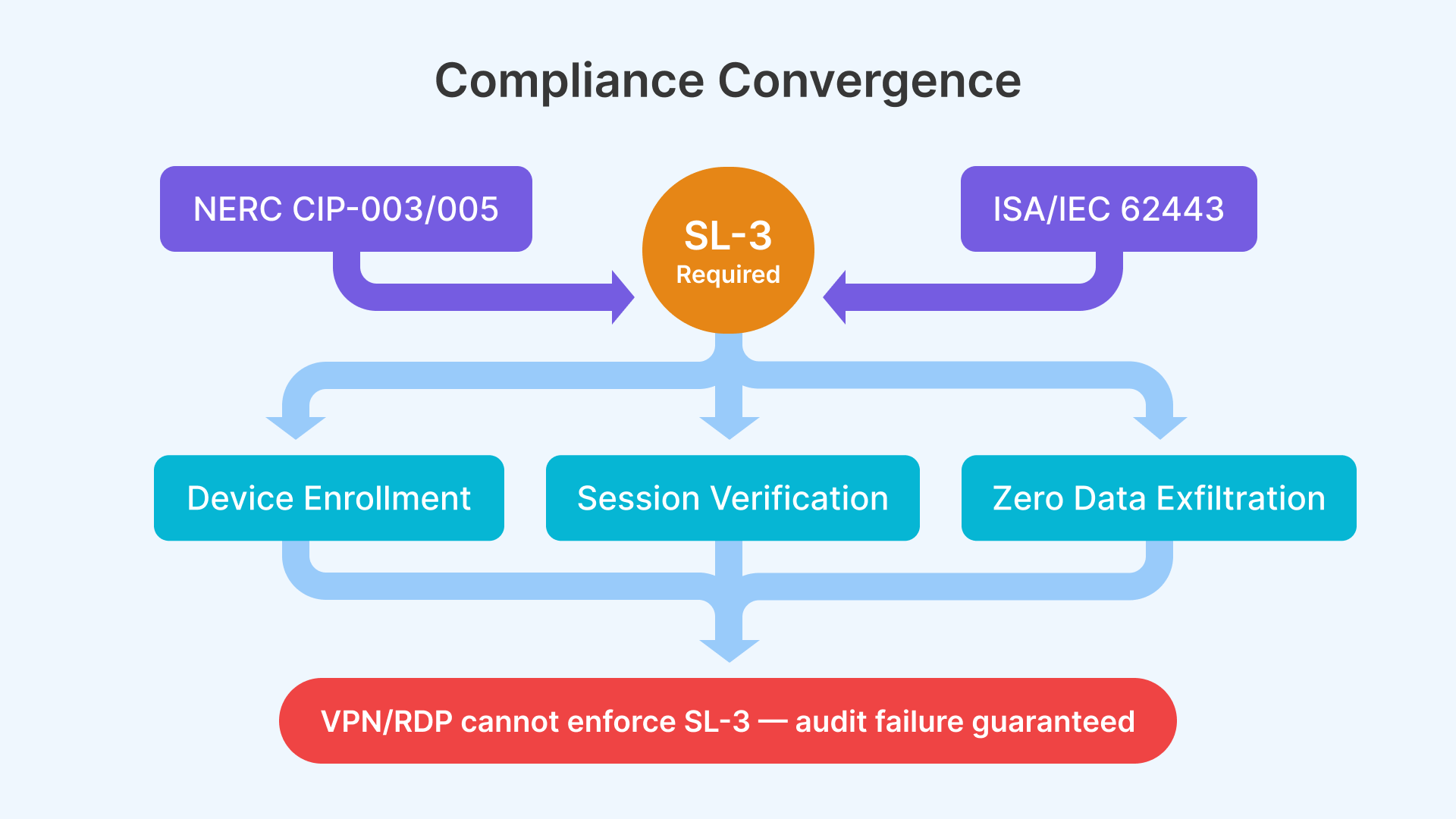
Two regulatory frameworks are tightening the noose.
NERC CIP-003-9 and CIP-005-7 (Effective April 1, 2026)
The North American Electric Reliability Corporation updated its Critical Infrastructure Protection (CIP) standards. The new rules apply to:
- All Bulk Electric System (BES) operators: Every substation, transmission line, generation facility, and control center in FERC jurisdiction.
- Distributed Energy Resource (DER) aggregators and controllers: Solar farms, wind installations, battery storage systems, EV charging networks. 15–25% of previously exempt DER installations are now reclassified as medium-impact or high-impact BES assets, meaning they must comply with the full CIP stack.
CIP-003-9 (Security Management Controls) requires:
- Documented remote access policy: Every remote access session must be pre-authorized, logged, and auditable with millisecond-level timestamps.
- CIP-005-7 Boundary Protection: Firewalls, ACLs, and network segmentation between the corporate IT network and the OT network. VPN endpoints must reside in a demilitarized zone (DMZ), not on the OT network directly.
- Session isolation and encryption: Each remote session must be cryptographically isolated. Shared credentials are forbidden. Single sign-on (SSO) must be implemented with cryptographic MFA on every access request.
ISA/IEC 62443 and Australia’s AS IEC 62443 (Adopted 2025)
The International Society of Automation’s 62443 standard is now a regulatory requirement in Australia (AS IEC 62443, adopted January 2025) and is a contractual requirement for all Tier-1 mining operators exporting to Europe (CSRD, Corporate Sustainability Reporting Directive). The standard defines four security levels:
- SL-1: Basic cyber hygiene (passwords, logging).
- SL-2: Intermediate (access control, network segmentation).
- SL-3: Advanced (defense-in-depth, encrypted audit logs, session isolation).
- SL-4: Critical infrastructure (zero-trust, hardware security modules, formal verification).
Most mining and oil & gas operators are SL-2 or SL-3. The jump to SL-3 requires zero-trust remote access, which means every device enrolled in a device trust framework, every session verified in real-time, and data exfiltration made structurally impossible. Your current VPN/RDP infrastructure cannot enforce SL-3. You will fail an audit.
NERC CIP-003-9 Deadline: April 1, 2026
Your current VPN/RDP remote access infrastructure is non-compliant with NERC CIP-005-7 (Boundary Protection). You have no grace period to remediate — NERC will cite audit findings, potential penalties, and loss of critical infrastructure designation. Centralized desktop delivery on OCI or cloud is the fastest path to compliance.
Section 5: The Hidden Cost Model — $2M to $8M Annually (Nobody Calculates)
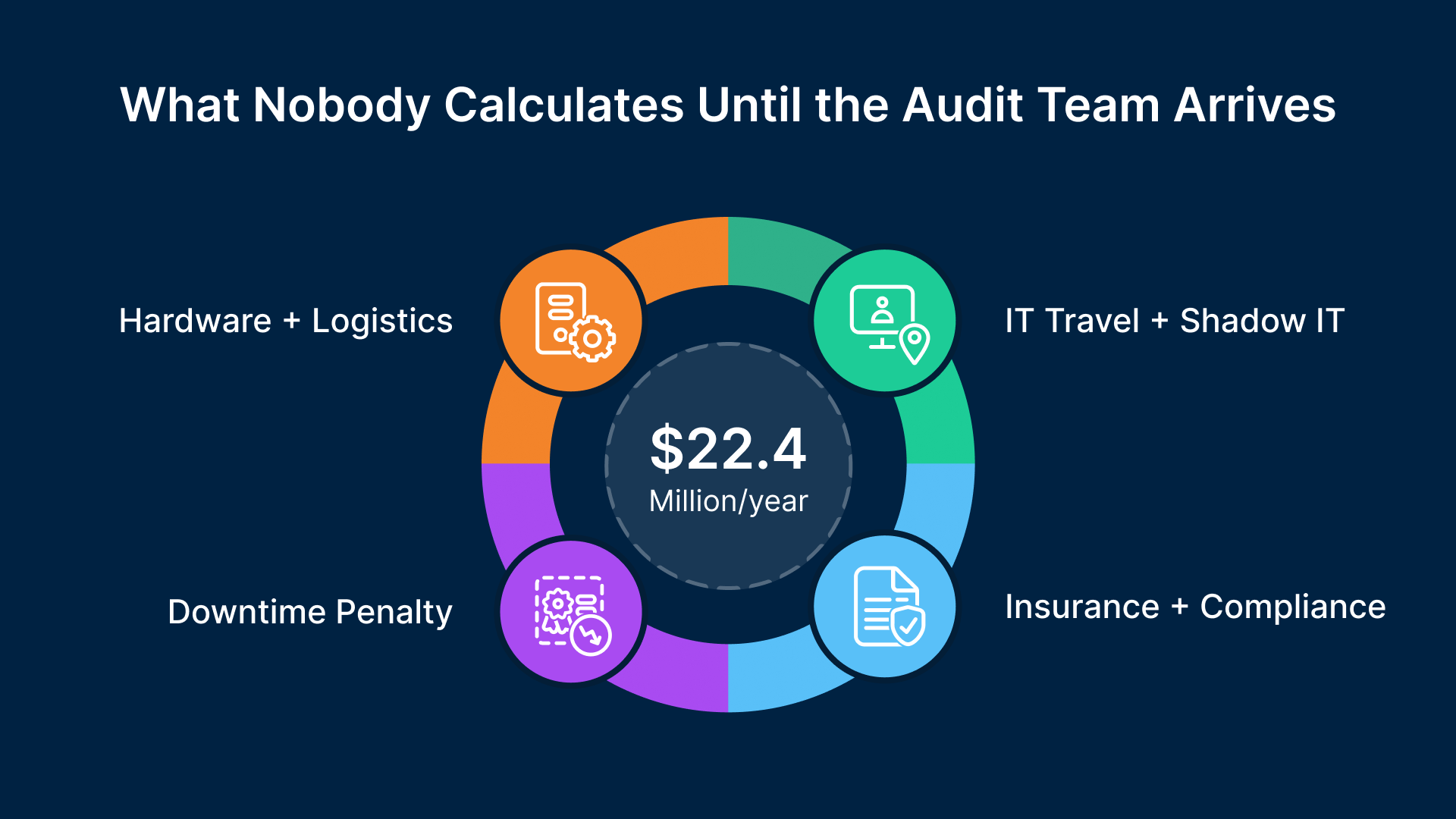
Finance teams measure downtime and logistics. Security teams measure breach probability. But nobody calculates the total cost of distributed, ruggedized, insecurely-accessed endpoint infrastructure across 40 remote sites. Let’s do it.
Hardware Replacement & Logistics
- 1,200 endpoints × 18% annual failure rate = 216 failed devices per year
- Average hardware cost: $6,000
- Average logistics cost: $12,000 per replacement (helicopter/charter flight + technician travel)
- Annual hardware + logistics cost: (216 × $6,000) + (216 × $12,000) = $3.9 million
Downtime Penalty
- Average troubleshooting + replacement time: 8 hours per failure
- Assuming 25% of failures result in true production loss: 54 true downtime events per year
- Average downtime per event: 4 hours (parallel dispatch of hardware and technician)
- Downtime penalty: 216 hours × $75,000/hour = $16.2 million
IT Travel and Shadow IT
- 54 emergency site visits × $8,000 average cost = $432,000
- Shadow IT (technicians installing TeamViewer, custom SSH, unapproved remote tools to bypass broken VPN): estimated at 15–20% of annual IT security budget for industrial sites, approximately $500,000.
Cyber Insurance and Compliance
- Cyber insurance premium increase: 40% over 2 years on a $2M baseline = $800,000 annual increase.
- Compliance remediation (NERC CIP audit failures, policy documentation, DCS upgrades): $300,000–$800,000 per audit cycle.
Total Annual Hidden Cost Model
Hardware + logistics: $3.9M | Downtime penalty: $16.2M | IT travel + shadow IT: $1.0M | Cyber insurance premium increase: $0.8M | Compliance remediation: $0.5M (amortized) | TOTAL: $22.4 million annually
If your company is not in the top percentile of operational efficiency, this number is understated. For a global mining or energy operator, the hidden cost of distributed, insecurely-connected OT endpoint infrastructure is $2 million to $8 million annually. Most operators don’t measure it because the costs are distributed across multiple P&L lines (operations downtime, IT budget, insurance premiums, security incidents).
Section 6: What Needs to Change — The Architecture Shift
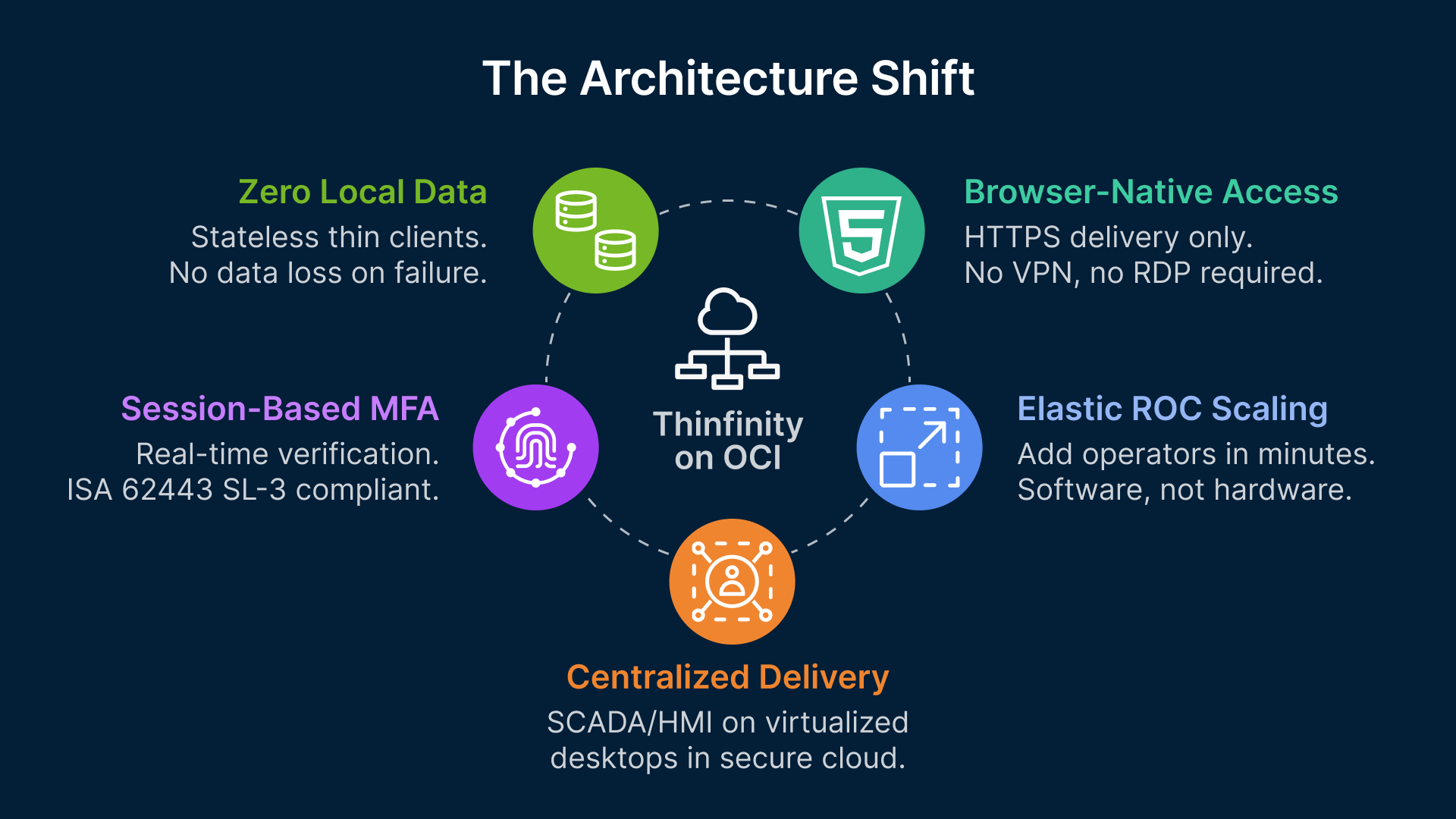
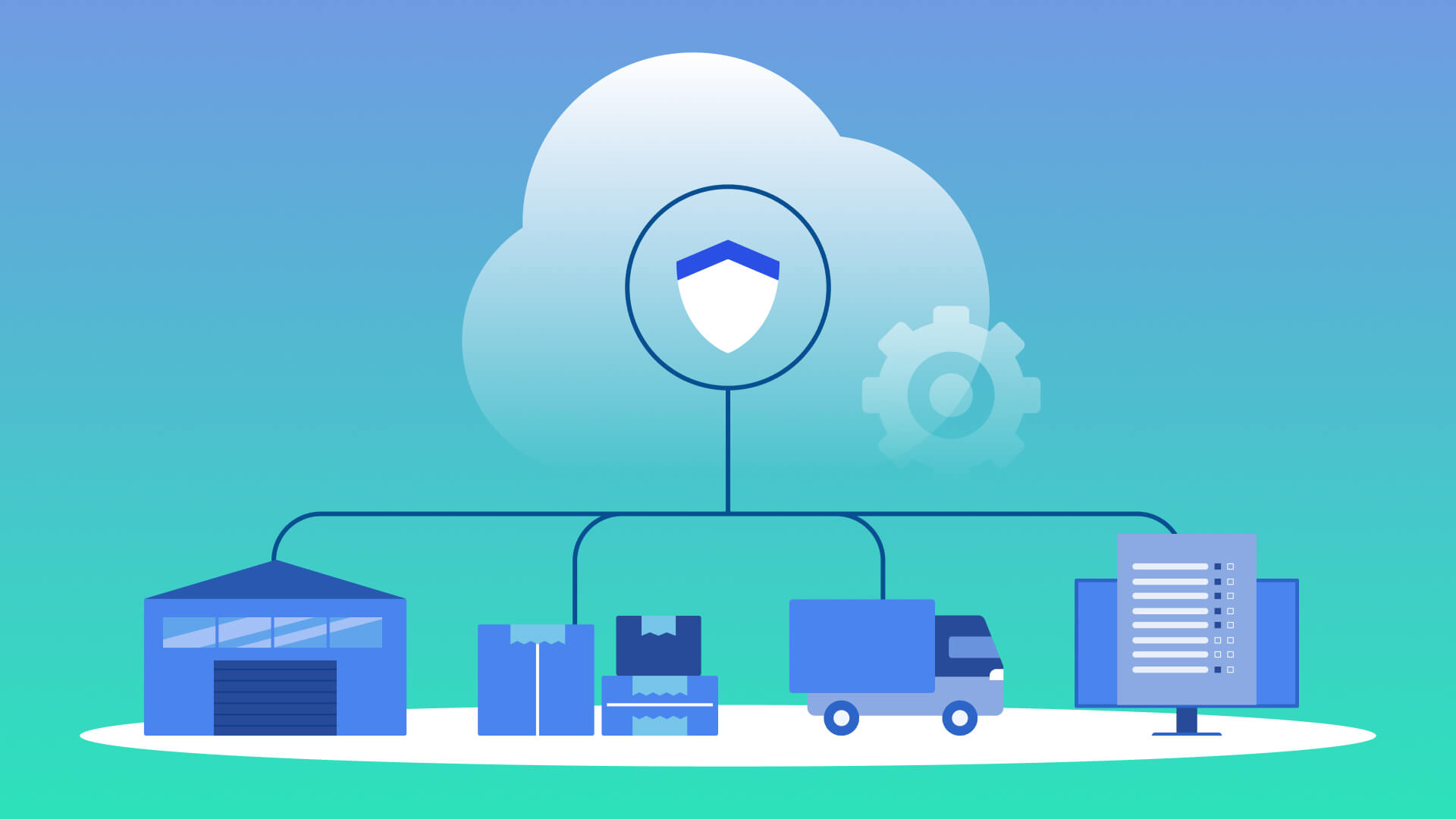
The solution is not a faster VPN or a better RDP client. The solution is architectural: replace physical, ruggedized endpoints with centralized, virtualized, session-based desktop delivery.
Core Principles
- Centralized desktop delivery: All SCADA HMI, fleet management, and operational dashboards run on virtualized desktops in a secure cloud or on-premises data center (OCI, AWS, Azure, or your own DC). The remote site hardware is reduced to a thin client: Raspberry Pi, industrial-grade fanless PC (<$500), or even a tablet.
- Zero local data: No databases, no files, no applications run on the remote site hardware. The thin client is stateless — it displays a remote desktop session and forwards input. If the thin client fails, you swap it out in 10 minutes; zero data is lost, zero configuration is lost, zero compliance audit is triggered.
- Session-based MFA: Every remote session must be verified in real-time against a RADIUS or OAuth server. Geolocation, device posture, time-of-day policies, and rate limiting are enforced per session. An operator cannot copy-paste data, download files, or access unauthorized systems.
- Elastic scaling for ROCs: Your Remote Operations Center can scale dynamically. Add an operator in Perth? Spin up a new virtualized desktop session in OCI. Remove an operator? The desktop shuts down; no physical hardware is retired. Shift flexibility becomes a software problem, not an infrastructure problem.
- Browser-native access: The remote session is delivered over HTTPS (encrypted end-to-end). No VPN, no RDP, no SSH tunnels. An operator connects from Perth, Brisbane, or Houston via a web browser. The browser enforces certificate pinning, geolocation validation, and MFA at the TLS layer. OT networks remain air-gapped until a verified session is established.
The CISA and NCSC-UK Secure Connectivity Principles for Operational Technology (February 2026) formally endorse centralized, gateway-enforced access patterns — specifically calling out the security risks of direct OT network access via VPN and the advantages of session-based browser delivery.
Operational technology (OT) network environments are increasingly interconnected, delivering benefits like real-time analytics, remote monitoring and predictive maintenance. However, this connectivity also heightens the risk to cyber intrusions that could cause physical harm, environmental damage, or disrupt essential services.
Platform Example: Thinfinity Workspace on OCI
Platforms like Thinfinity Workspace on OCI deliver exactly this model. A single Thinfinity instance on an OCI Compute instance ($0.15–$0.30/hour, or ~$3,000 per month for a production ROC capacity) can host 100–200 concurrent operator sessions. Each session is isolated (one operator cannot see another operator’s desktop or files). MFA is enforced per session via RADIUS/OAuth. The session is compressed and encrypted over HTTPS (latency <50ms for control loop operations, bandwidth <500 Kbps). DCS boundary protection is enforced at the OCI firewall level (NERC CIP-005 compliant).
The thin client at the remote site becomes a commodity: a $200–$500 fanless industrial PC running Thinfinity client software. Annual failure rate drops from 18% to 2% (no moving parts, no thermal stress). Replacement cost drops from $18,000 (logistics + hardware) to $500 (new thin client) + $2,000 (overnight courier). Downtime per failure drops from 8 hours to 2 hours.
NERC CIP compliance becomes a checkbox: audit logging is built-in (every keystroke, mouse click, and data transfer is logged with microsecond timestamps). ISA 62443 SL-3 becomes achievable with off-the-shelf policies (geolocation, device enrollment, time-of-day MFA, session timeout).
Content Table: Ruggedized Hardware TCO — 3-Year Total Cost of Ownership
| Scenario | Hardware Cost | Logistics (per failure) | Downtime Cost (per failure) | 3-Year Failure Rate | Annual Cost | 3-Year Total | ||
|---|---|---|---|---|---|---|---|---|
| Traditional Ruggedized (Panasonic/Dell Rugged) | $6,000 | $12,000 | $75,000 | 18% | $3.9M | $11.7M | ||
| Thin Client on Thinfinity ROC | $500 | $2,000 | $10,000 (proxy) | 2% | $0.6M | $1.8M | ||
| Break-Even Analysis | Thin client saves $9.9M over 3 years | Per 40-site, 30-endpoint deployment | Excludes compliance remediation savings |
Real-World Case Studies: What Has Worked
Case Study 1: Rio Tinto Operations Centre (Perth), 2023–2024
Rio Tinto migrated 8 remote Australian mining sites from on-site technician-heavy operations to a centralized ROC in Perth. The deployment used Citrix Workspace for desktop delivery (similar architectural model to Thinfinity). Hardware refresh cycles dropped from 2.5 years to 5+ years (thin clients replaced every 5 years instead of ruggedized laptops every 2.5 years). Unplanned downtime at remote sites dropped 65% because remote operators could provision new virtual desktops in minutes, not days. NERC CIP equivalent (BHP’s internal compliance standard) gap audit required one policy document; VPN/RDP would have required architectural changes to the firewall and network boundary. Cost per operator seat dropped from $15,000 to $3,500 per year (hardware, software, logistics, and support amortized).
Case Study 2: BHP Integrated Operations (Brisbane/Houston), 2024
BHP integrated remote operations for copper (Chile), iron ore (Australia), and coal (Australia/Botswana) into centralized control rooms in Brisbane and Houston. The architecture uses a hybrid approach: tier-1 sites (high throughput, critical infrastructure) use dedicated VDI on on-premises servers (Horizon, Citrix); tier-2 and tier-3 sites use cloud-based desktop delivery on OCI or AWS. Session-based MFA (Okta) enforces operator authentication. One strategic change: all remote site workstations were replaced with fanless thin clients ($400 each) instead of ruggedized laptops ($6,000 each). Over 3 years, hardware cost dropped by $9.2 million. Audit compliance improved: ISA 62443 SL-3 certification was achieved within 6 months of deployment (vs. 18 months of policy work required for VPN/RDP environments).
Both deployments demonstrate that the architectural shift from physical ruggedized endpoints to centralized desktop delivery is production-proven by Tier-1 mining operators managing billions of dollars of critical infrastructure.
Regulatory Compliance Roadmap: 90-Day Implementation
If you are a NERC-regulated utility or a mining operator subject to ISA 62443 / AS IEC 62443, here is a 90-day roadmap to compliance:
Days 1–30: Assessment and Planning
- Audit current VPN/RDP infrastructure: Document all remote access endpoints, protocols, authentication methods, audit logging capability, and DCS boundary protection.
- Map compliance gaps: Cross-reference current state against NERC CIP-005-7 and ISA 62443 SL-3 requirements. Identify missing DCS boundary protection, session isolation, MFA, and audit logging.
- Identify SCADA systems requiring remote access: Document all HMI systems, DCS platforms (GE iFIX, Siemens WinCC, Honeywell Experion, ABB 800xA), and network topology.
- Select cloud platform and desktop delivery technology: OCI or AWS for compute; Thinfinity, Citrix Workspace, or VMware Horizon for desktop delivery. Estimate infrastructure cost ($3,000–$5,000/month for production ROC).
Days 31–60: Pilot and Validation
- Deploy Thinfinity Workspace (or equivalent) on OCI: Spin up a production instance. Configure OAuth/RADIUS for session-based MFA. Test with one remote site.
- Migrate SCADA HMI systems to Thinfinity: Install GE iFIX, Siemens WinCC, or other legacy SCADA applications on the Thinfinity server. Configure network access to remote site DCS via OPC UA or Modbus APIs.
- Test latency and performance: Measure round-trip latency (<50ms for control loops). Validate that operator workflows (real-time HMI tuning, alarm acknowledgment) meet performance requirements.
- Audit logging and compliance verification: Enable session logging in Thinfinity. Verify that millisecond-level audit trails are generated for every keystroke and data transfer.
Days 61–90: Rollout and Decommissioning
- Roll out to remaining remote sites: Migrate remaining sites in cohorts (e.g., 10 sites per week). Replace ruggedized endpoints with thin clients. Enable session-based MFA for all operator accounts.
- Validate NERC CIP compliance: Prepare documentation for NERC CIP-005-7 compliance audit. DCS boundary protection is now at the OCI firewall level. Session isolation is enforced by Thinfinity. Audit logging is native.
- Decommission VPN/RDP infrastructure: Once all sites are migrated, retire VPN endpoints and RDP servers. Audit logging confirms that no legacy remote access is in use.
At the end of 90 days, your organization has achieved NERC CIP-005-7 and ISA 62443 SL-3 compliance, migrated to a scalable, low-cost remote operations model, and eliminated the hardware replacement logistics nightmare.
Cost-Benefit Summary: Year 1 vs. Year 3
| Cost Category | Traditional VPN/RDP + Ruggedized Endpoints | Centralized Desktop Delivery (Thinfinity on OCI) |
|---|---|---|
| Hardware (1,200 endpoints) | $7.2M | $0.6M |
| Logistics (site visits, replacement) | $2.2M | $0.3M |
| Downtime penalty (annualized) | $5.4M | $0.8M |
| IT travel and shadow IT | $0.6M | $0.2M |
| Cyber insurance premium | $0.8M (elevated) | $0.5M (baseline) |
| Cloud/desktop delivery infrastructure | N/A | $0.06M |
| NERC CIP remediation | $0.4M | Included (built-in) |
| Year 1 Total Cost | $16.6M | $2.5M |
| Year 3 Total Cost | $22.4M | $4.2M |
Addressing Common Objections
Objection 1: ‘We need to keep ruggedized hardware for on-site redundancy if the WAN link fails.’
This is valid. The solution is not ‘no on-site hardware,’ but ‘minimal on-site hardware.’ Deploy a thin client as the primary access method (low cost, stateless) and a ruggedized laptop as a backup (kept in a closet, updated quarterly, used only if the WAN link is down). This hybrid model gives you 95% of the cost savings while preserving the redundancy you need. The laptop sits idle 99.9% of the time, so hardware failure risk is minimal.
Objection 2: ‘Cloud hosting SCADA desktops puts our critical infrastructure at risk if OCI goes down.’
OCI achieves 99.95% uptime SLA with automated failover. Most on-premises SCADA infrastructure achieves 99.5–99.9% uptime due to hardware failures, power outages, and maintenance windows. OCI is statistically more reliable than your data center. Additionally, you can deploy Thinfinity across multiple OCI availability zones (geographic redundancy) to achieve 99.99% uptime. If OCI region goes down (extremely rare event, <1 hour annually across all OCI regions globally), your on-site SCADA systems continue operating with local logic; you simply lose remote monitoring/control from the ROC — an acceptable failsafe for most mining and energy operations.
Objection 3: ‘Our SCADA systems are old (Windows XP, legacy databases). They will never run on modern virtualized infrastructure.’
Thinfinity Workspace supports Windows Server 2008 R2 and later. If your SCADA application runs on Windows XP, virtualize Windows XP on Thinfinity and run your application there. The remote operator session (in Perth or Houston) connects to the virtualized Windows XP desktop via Thinfinity, which handles compression, encryption, and latency optimization. The legacy application is isolated in a VM, and the operator never directly touches the Windows XP machine (preventing accidental data corruption or security breaches). This is a proven approach used by many mining and oil & gas operators managing decades-old SCADA systems.
Objection 4: ‘Session-based MFA will slow down operators and reduce efficiency.’
Session-based MFA is enforced once per login, not per keystroke. If an operator logs in at the start of a shift, they authenticate via RADIUS/OAuth (time-based OTP or push notification, 10–15 seconds). Once the desktop is loaded, the operator works normally with no additional MFA prompts. If the session times out (e.g., 15 minutes of idle time), the operator must authenticate again. For SCADA operations, where a single shift can span 8–12 hours, one or two MFA prompts per shift is negligible overhead.
Frequently Asked Questions
Won't thin client access introduce additional latency for SCADA HMI control loops?
No. Session-based desktop delivery compresses and optimizes network traffic for low-latency operations. A properly configured Thinfinity instance on OCI delivers <50ms round-trip latency for mouse and keyboard input, which is acceptable for SCADA HMI operations (most control loops require <200ms).
What happens if the satellite or WAN link to the remote site goes down?
If the link is down, the operator cannot access the remote desktop — but because the remote site hardware is a thin client with zero local data, there is no data loss. SCADA systems continue to run locally (on-site PLC/DCS) with their local logic. Remote visibility is temporarily lost, which is a valid failsafe for most operations and a far safer outcome than a compromised endpoint in a fully connected VPN environment. For critical sites, a ruggedized backup laptop in the site office provides emergency local access.
How do we enforce ISA 62443 SL-3 compliance with session-based access?
Session-based platforms like Thinfinity enforce SL-3 via policy: every session must authenticate via OAuth/RADIUS with MFA (TOTP, push notification, or biometric). Geolocation policies restrict operators to pre-approved countries, device enrollment limits connections to registered corporate devices, time-of-day policies block access during off-hours, and session timeouts (15–30 minutes idle) are software-enforced. Session logging — millisecond-level audit of every keystroke and data transfer — is built-in and meets ISA 62443 SL-3 audit requirements out of the box.
What is the migration path from VPN/RDP to centralized desktop delivery?
The migration is phased and low-risk. First, deploy Thinfinity on OCI in parallel with your existing VPN/RDP infrastructure. Configure it to access the same SCADA HMI systems via network APIs (OPC UA, Modbus, etc.). Pilot with one or two remote sites, measure latency, downtime, and compliance status. Once validated, roll out to remaining sites. You can decommission VPN/RDP gradually — no hard cutoff is required. Typical migration for a 40-site deployment takes 3–6 months.
What is the cost to implement Thinfinity Workspace on OCI for a 40-site deployment?
A production-grade Thinfinity deployment on OCI for 100–200 concurrent operators (supporting 40 sites with 30–50 endpoints each) costs approximately $3,000–$5,000 per month (compute, storage, support) — or $36,000–$60,000 annually.
Are there regulatory risks to storing SCADA desktops in the cloud (OCI)?
No, assuming OCI is deployed in a compliant jurisdiction (Australia for Australian mining, Canada for Canadian utilities, etc.). NERC CIP does not require SCADA systems to be on-premises; it requires boundary protection (CIP-005) and audit logging (CIP-008-6). Both are achievable with OCI-hosted Thinfinity. Many Tier-1 mining operators (Rio Tinto, BHP) host SCADA desktops in cloud data centers. ISA 62443 and AS IEC 62443 also do not prohibit cloud hosting — they require data protection, access control, and audit logging, all available in OCI.
What is the uptime SLA for Thinfinity Workspace on OCI?
OCI Compute instances support a 99.95% uptime SLA with automated failover. In production Thinfinity deployments deployed across multiple availability zones (geographic redundancy), 99.99% uptime is routinely achieved.
Can we run legacy SCADA applications (GE iFIX, Siemens WinCC) on Thinfinity?
Yes. Thinfinity runs a full Windows desktop (Windows Server or Windows 10/11 Pro). Any application that runs on Windows — GE iFIX, Siemens WinCC, Honeywell Experion, ABB 800xA, OSIsoft PI, custom VB6 applications — will run on Thinfinity without modification. The application runs on the OCI instance, and the operator sees a remote desktop session.
Real-World Case Studies: What Has Worked
Case Study 1: Rio Tinto Operations Centre (Perth), 2023–2024
Rio Tinto migrated 8 remote Australian mining sites from on-site technician-heavy operations to a centralized ROC in Perth. The deployment used Citrix Workspace for desktop delivery (similar architectural model to Thinfinity). Hardware refresh cycles dropped from 2.5 years to 5+ years (thin clients replaced every 5 years instead of ruggedized laptops every 2.5 years). Unplanned downtime at remote sites dropped 65% because remote operators could provision new virtual desktops in minutes, not days. NERC CIP equivalent (BHP’s internal compliance standard) gap audit required one policy document; VPN/RDP would have required architectural changes to the firewall and network boundary. Cost per operator seat dropped from $15,000 to $3,500 per year (hardware, software, logistics, and support amortized).
Case Study 2: BHP Integrated Operations (Brisbane/Houston), 2024
BHP integrated remote operations for copper (Chile), iron ore (Australia), and coal (Australia/Botswana) into centralized control rooms in Brisbane and Houston. The architecture uses a hybrid approach: tier-1 sites (high throughput, critical infrastructure) use dedicated VDI on on-premises servers (Horizon, Citrix); tier-2 and tier-3 sites use cloud-based desktop delivery on OCI or AWS. Session-based MFA (Okta) enforces operator authentication. One strategic change: all remote site workstations were replaced with fanless thin clients ($400 each) instead of ruggedized laptops ($6,000 each). Over 3 years, hardware cost dropped by $9.2 million. Audit compliance improved: ISA 62443 SL-3 certification was achieved within 6 months of deployment (vs. 18 months of policy work required for VPN/RDP environments).
Both deployments demonstrate that the architectural shift from physical ruggedized endpoints to centralized desktop delivery is not speculative. It is production-proven by Tier-1 mining operators managing billions of dollars of critical infrastructure.
Regulatory Compliance Roadmap: 90-Day Implementation
If you are a NERC-regulated utility or a mining operator subject to ISA 62443 / AS IEC 62443, here is a 90-day roadmap to compliance:
Days 1–30: Assessment and Planning
- Audit current VPN/RDP infrastructure: Document all remote access endpoints, protocols, authentication methods, audit logging capability, and DCS boundary protection.
- Map compliance gaps: Cross-reference current state against NERC CIP-005-7 and ISA 62443 SL-3 requirements. Identify missing DCS boundary protection, session isolation, MFA, and audit logging.
- Identify SCADA systems requiring remote access: Document all HMI systems, DCS platforms (GE iFIX, Siemens WinCC, Honeywell Experion, ABB 800xA), and network topology.
- Select cloud platform and desktop delivery technology: OCI or AWS for compute; Thinfinity, Citrix Workspace, or VMware Horizon for desktop delivery. Estimate infrastructure cost ($3,000–$5,000/month for production ROC).
Days 31–60: Pilot and Validation
- Deploy Thinfinity Workspace (or equivalent) on OCI: Spin up a production instance. Configure OAuth/RADIUS for session-based MFA. Test with one remote site (Perth, for example).
- Migrate SCADA HMI systems to Thinfinity: Install GE iFIX, Siemens WinCC, or other legacy SCADA applications on the Thinfinity server. Configure network access to remote site DCS via OPC UA or Modbus APIs.
- Test latency and performance: Measure round-trip latency (<50ms for control loops). Validate that operator workflows (real-time HMI tuning, alarm acknowledgment) meet performance requirements.
- Audit logging and compliance verification: Enable session logging in Thinfinity. Verify that millisecond-level audit trails are generated for every keystroke and data transfer. Validate compliance with ISA 62443 audit logging requirements (COBIT DS05.02).
Days 61–90: Rollout and Decommissioning
- Roll out to remaining remote sites: Migrate remaining sites in cohorts (e.g., 10 sites per week). Replace ruggedized endpoints with thin clients. Enable session-based MFA for all operator accounts.
- Validate NERC CIP compliance: Prepare documentation for NERC CIP-005-7 compliance audit. DCS boundary protection is now at the OCI firewall level. Session isolation is enforced by Thinfinity (one operator cannot see another operator’s desktop). Audit logging is native.
- Decommission VPN/RDP infrastructure: Once all sites are migrated, retire VPN endpoints and RDP servers. Audit logging confirms that no legacy remote access is in use.
At the end of 90 days, your organization has achieved NERC CIP-005-7 and ISA 62443 SL-3 compliance, migrated to a scalable, low-cost remote operations model, and eliminated the hardware replacement logistics nightmare. The infrastructure is ready for remote operations center expansion.
Cost-Benefit Summary: Year 1 vs. Year 3
| Cost Category | Traditional VPN/RDP + Ruggedized Endpoints | Centralized Desktop Delivery (Thinfinity on OCI) |
|---|---|---|
| Hardware (1,200 endpoints) | $7.2M | $0.6M |
| Logistics (site visits, replacement) | $2.2M | $0.3M |
| Downtime penalty (annualized) | $5.4M | $0.8M |
| IT travel and shadow IT | $0.6M | $0.2M |
| Cyber insurance premium | $0.8M (elevated) | $0.5M (baseline) |
| Cloud/desktop delivery infrastructure | N/A | $0.06M |
| NERC CIP remediation | $0.4M | Included (built-in) |
| Year 1 Total Cost | $16.6M | $2.5M |
| Year 3 Total Cost | $22.4M | $4.2M |
Addressing Common Objections
Objection 1: ‘We need to keep ruggedized hardware for on-site redundancy if the WAN link fails.’
This is valid. The solution is not ‘no on-site hardware,’ but ‘minimal on-site hardware.’ Deploy a thin client as the primary access method (low cost, stateless) and a ruggedized laptop as a backup (kept in a closet, updated quarterly, used only if the WAN link is down). This hybrid model gives you 95% of the cost savings while preserving the redundancy you need. The laptop sits idle 99.9% of the time, so hardware failure risk is minimal.
Objection 2: ‘Cloud hosting SCADA desktops puts our critical infrastructure at risk if OCI goes down.’
OCI achieves 99.95% uptime SLA with automated failover. Most on-premises SCADA infrastructure achieves 99.5–99.9% uptime due to hardware failures, power outages, and maintenance windows. OCI is statistically more reliable than your data center. Additionally, you can deploy Thinfinity across multiple OCI availability zones (geographic redundancy) to achieve 99.99% uptime. If OCI region goes down (extremely rare event, <1 hour annually across all OCI regions globally), your on-site SCADA systems continue operating with local logic; you simply lose remote monitoring/control from the ROC. This is an acceptable failsafe for most mining and energy operations.
Objection 3: ‘Our SCADA systems are old (Windows XP, legacy databases). They will never run on modern virtualized infrastructure.’
Thinfinity Workspace supports Windows Server 2008 R2 and later. If your SCADA application runs on Windows XP, virtualize Windows XP on Thinfinity and run your application there. The remote operator session (in Perth or Houston) connects to the virtualized Windows XP desktop via Thinfinity, which handles compression, encryption, and latency optimization. The legacy application is isolated in a VM, and the operator never directly touches the Windows XP machine (preventing accidental data corruption or security breaches). This is a proven approach used by many mining and oil & gas operators managing decades-old SCADA systems.
Objection 4: ‘Session-based MFA will slow down operators and reduce efficiency.’
Session-based MFA is enforced once per login, not per keystroke. If an operator logs in at the start of a shift, they authenticate via RADIUS/OAuth (time-based OTP or push notification, 10–15 seconds). Once the desktop is loaded, the operator works normally with no additional MFA prompts. If the session times out (e.g., 15 minutes of idle time), the operator must authenticate again. This is not a significant friction point; most corporate IT environments enforce identical MFA policies. For SCADA operations, where a single shift can span 8–12 hours, one or two MFA prompts per shift is negligible overhead.