The 2026 Global Banking Compliance Landscape
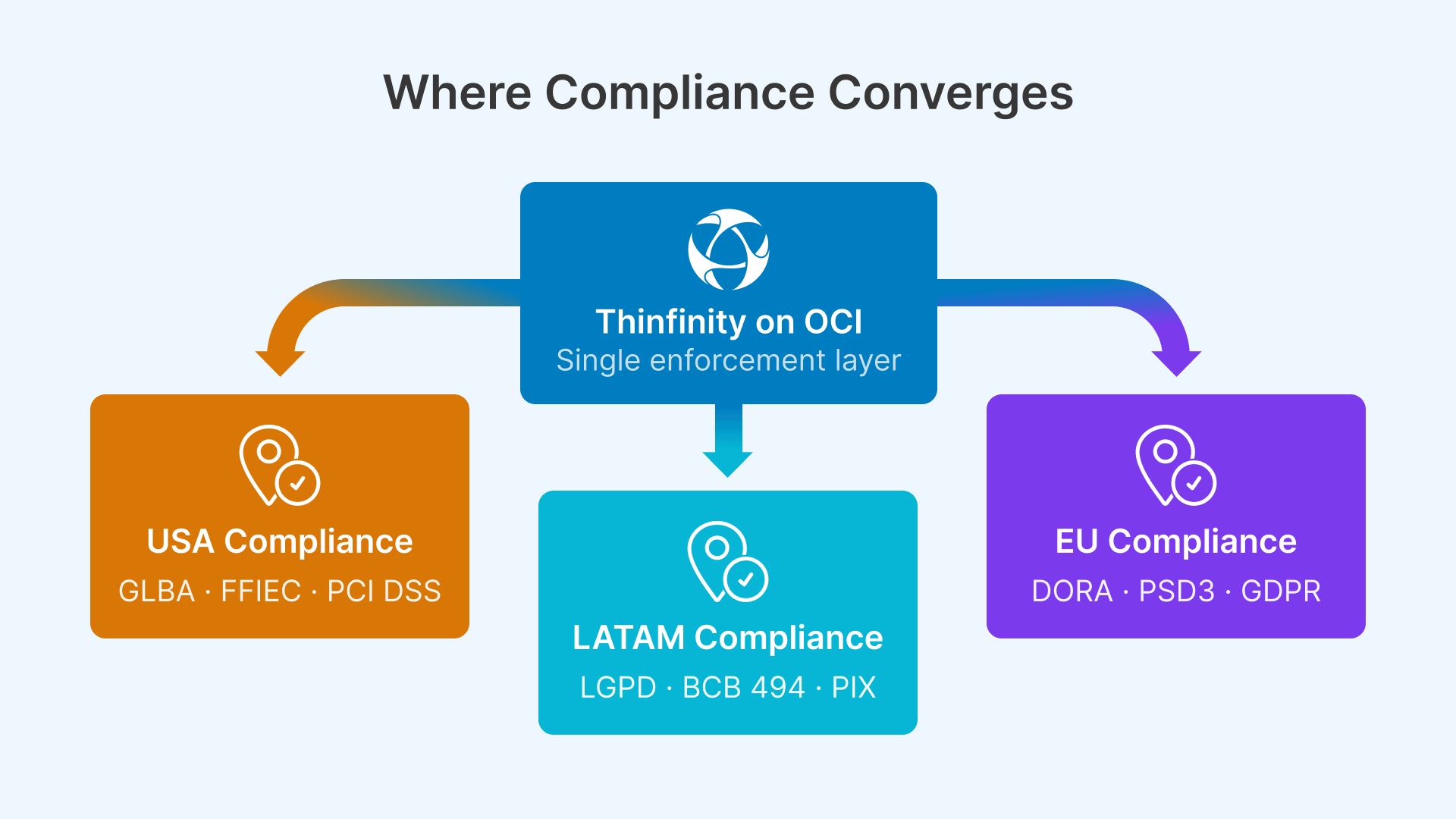
Banking is the world’s most regulated industry for endpoint security, and 2026 marks a critical convergence of new and updated regulatory frameworks across the three largest financial markets: the United States, the European Union, and Latin America.
In the US, the FTC’s 2023 GLBA Safeguards Rule amendments, combined with FFIEC examination expectations and PCI DSS v4.0 enforcement, created a prescriptive mandate for centralized endpoint security controls. In the EU, the Digital Operational Resilience Act (DORA) became effective January 17, 2025, and enforcement audits are intensifying throughout 2026. In Latin America, Brazil’s LGPD and the Brazilian Central Bank’s (BCB) resolution updates are driving a fundamental shift toward data residency and audit trail requirements that only cloud-based, server-side session architectures can satisfy at scale.
For global banks operating across all three regions, this regulatory convergence creates a single, unified imperative: move from distributed endpoint security to centralized, cloud-hosted virtual desktop infrastructure where all data processing, all access control, and all audit trails are enforced at the application layer — not at the device layer. This guide provides a compliance-mapped implementation reference for financial institutions evaluating VDI on Oracle Cloud Infrastructure as a global, examination-ready modernization strategy.
United States: GLBA Safeguards Rule, FFIEC, and PCI DSS v4.0
The US banking regulatory environment is defined by three overlapping frameworks that directly impact endpoint architecture: the FTC’s GLBA Safeguards Rule, the FFIEC IT Examination Handbook expectations, and PCI DSS v4.0 enforcement. All three converged in 2025–2026, creating unprecedented pressure on US banks to modernize endpoint security.
GLBA Safeguards Rule 2023 Amendments
The FTC’s December 2023 updates replaced the prior principles-based approach with specific, prescriptive technical requirements. Effective June 2023, these amendments apply to all financial institutions handling nonpublic personal information (NPI). The requirements most directly affecting endpoint architecture are mandatory MFA for any individual accessing NPI, encryption both in transit and at rest, annual penetration testing and semi-annual vulnerability assessments, designation of a Qualified Individual (effectively a CISO), and 30-day breach notification to the FTC for incidents affecting 500+ consumers.
In a traditional thick-client environment where endpoints store financial data, MFA configuration is distributed across hundreds of devices, encryption is inconsistent, and penetration testing scope is massive. In a Thinfinity VDI architecture on OCI, MFA is enforced at a single gateway layer, data never reaches the endpoint in unencrypted form, pentesting scope is reduced to the OCI infrastructure and session hosts, and breach notification timelines are dramatically shortened because all audit evidence exists in a centralized, immutable session log.
FFIEC IT Examination Handbook and NIST CSF 2.0
The FFIEC — comprising the OCC, FDIC, Federal Reserve, and NCUA — evaluates bank cybersecurity programs using the FFIEC IT Examination Handbook. Critically, the FFIEC CAT (Cybersecurity Assessment Tool) was sunset on August 31, 2025. FFIEC examiners now use NIST Cybersecurity Framework 2.0 and CISA Cybersecurity Performance Goals as the primary evaluation standard.
FFIEC CAT Sunset + NIST CSF 2.0 Adoption
US banks no longer use the FFIEC CAT for examination preparation. FFIEC examiners now evaluate cybersecurity programs using NIST Cybersecurity Framework 2.0 and CISA Cybersecurity Performance Goals. Thinfinity VDI on OCI satisfies the Govern, Identify, Protect, Detect, Respond, and Recover functions of NIST CSF 2.0.
NIST CSF 2.0 emphasizes asset management with continuous visibility, access control with role-based least-privilege, encryption and data protection, detection and monitoring of unauthorized activities, and incident response with forensic capability. Thinfinity VDI directly satisfies all five pillars: compute assets are managed centrally on OCI, access is controlled by role and enforced by the Thinfinity Gateway, all data is encrypted at rest on OCI Block Volume and Object Storage, session activity is continuously logged and exported to SIEM platforms, and forensic capability is provided through immutable session recordings accessible to investigators within seconds.
OCC and FDIC Third-Party Risk Management Guidance
The June 2023 joint guidance from the OCC, FDIC, and Federal Reserve on third-party risk management requires institutions to perform due diligence on cloud vendors, establish contracts with specific data handling and audit provisions, define exit strategies, and implement ongoing monitoring of vendor performance. Oracle Cloud Infrastructure maintains current SOC 2 Type II, SOC 1 Type II, and ISO 27001 certifications available for regulatory review under NDA. OCI’s FedRAMP High authorization covers both commercial regions and government cloud regions, providing additional assurance for institutions with government banking relationships.
PCI DSS v4.0 Enforcement (Fully Effective March 31, 2025)
PCI DSS v4.0 became fully enforceable on March 31, 2025, introducing stricter controls for Requirement 2 (secure configurations), Requirement 7 (user access control), Requirement 8 (MFA), and Requirement 12 (policies and program management). For banks processing cardholder data via debit cards, credit cards, or merchant services — which includes virtually all US financial institutions — PCI DSS v4.0 compliance is non-negotiable.
The requirement that most directly impacts endpoint architecture is Requirement 8’s mandate that MFA be required for all users accessing the Cardholder Data Environment (CDE). In a distributed endpoint model, enforcing consistent MFA across hundreds of teller workstations, loan officer desktops, and branch manager computers is operationally complex. In Thinfinity VDI on OCI, MFA is enforced once at the Gateway layer, covering all users accessing any banking application regardless of device or location.
European Union: DORA, PSD3, and GDPR
The European regulatory environment in 2026 is defined by the Digital Operational Resilience Act (DORA), the emerging Payment Services Regulation 3 (PSD3), and the ongoing GDPR data protection framework. Unlike the US prescriptive approach, EU regulation emphasizes resilience testing, third-party risk assessment, and incident response capability.
DORA: Digital Operational Resilience Act
DORA became effective January 17, 2025, and enforcement audits are intensifying throughout 2026. The regulation applies to all financial institutions (banks, insurance companies, investment firms, payment institutions) operating in the EU. Its four core pillars are ICT risk management framework with governance and continuous monitoring, incident classification and breach notification (critical incidents to NCA within 24 hours), third-party provider oversight with due diligence and contractual provisions, and digital resilience testing including scenario analysis and penetration testing.
DORA Enforcement Intensifying in 2026
DORA enforcement actions began in late 2025 and will escalate throughout 2026. The European Banking Authority and national regulators are issuing guidance on incident reporting, third-party risk assessments, and resilience testing. Banks should ensure DORA-relevant evidence — incident logs, third-party audit reports, resilience test results — is documented and audit-ready now.
For VDI deployments, DORA directly impacts endpoint architecture through its third-party risk requirements. If the bank uses OCI as a cloud provider, DORA requires the bank to assess OCI’s cybersecurity posture, obtain certification evidence (SOC 2, ISO 27001), and monitor OCI’s incident response capability. Thinfinity Workspace on OCI satisfies these requirements because OCI provides published security reports covering incident response, forensic capability, and resilience testing. Thinfinity’s session recording capability further supports DORA’s incident classification requirement: when an incident occurs, the bank can retrieve the session recording corresponding to the incident time period, determine the scope of data exposure, and notify European regulators within the 24-hour critical incident window.
PSD3 / Payment Services Regulation 3
PSD3 and the Payment Services Regulation are expected to come into force in Q1–Q2 2026, replacing the current PSD2 framework. PSD3 will strengthen fraud prevention controls, require open banking data sharing with stronger security guarantees, and mandate stronger authentication for payment initiation. For endpoint security, PSD3 will likely reinforce MFA requirements and add new controls for transaction verification and real-time fraud detection. VDI deployments satisfy PSD3 by centralizing payment transaction interfaces on OCI, enabling real-time fraud monitoring at the session layer, and providing complete audit trails of all transaction approvals.
GDPR Data Residency and Cross-Border Compliance
GDPR imposes data residency requirements for personal data processing. Under Articles 32 and 45, personal data of EU residents must be processed within the EU or transferred only to jurisdictions with adequate data protection. For banking data — which includes extensive personal information about customers — GDPR compliance requires that session data remain within the EU. OCI’s Frankfurt, Amsterdam, London, Marseille, Stockholm, and Milan regions (expanded in 2025–2026) enable EU-only data processing without any data egress to non-EU jurisdictions. Thinfinity sessions running on OCI EU regions never transmit banking or personal data outside the EU.
Latin America: LGPD, BCB Resolution 494, and PIX / Real-Time Payments
Latin America presents a uniquely demanding regulatory environment that combines strict data protection laws (LGPD in Brazil), central bank audit trail requirements (BCB Circular 3.909 and Resolution 494), and real-time payment system mandates (PIX in Brazil, CoDi/SPEI in Mexico, Transfiya in Colombia). Only cloud-based, region-localized VDI architectures can satisfy this convergence at scale.
LGPD: Brazil’s Lei Geral de Proteção de Dados
Brazil’s LGPD, enforced by the ANPD since 2020, is functionally equivalent to the EU’s GDPR. All financial institutions processing personal data of Brazilian residents must comply with LGPD’s requirements for data minimization, encryption, access control, breach notification, and right to erasure. LGPD does not mandate strict data sovereignty, but it requires offshore processing to occur only in jurisdictions approved by ANPD. OCI’s São Paulo region is the appropriate choice for Brazilian banks: data is processed within Brazil, and Thinfinity ensures that no customer personal data is stored on endpoint devices — only session streams and keyboard/mouse input traverse the network.
BCB Resolution 494 and Audit Obligations
The Brazilian Central Bank issued Resolution 494 in September 2025 with new requirements for payment institutions and financial technology companies. The resolution reinforces BCB Circular 3.909’s audit trail requirements: all access to core banking and payment systems must be logged with user identity, timestamp, session source, and authentication method. These logs must be retained and made available for BCB examination within 24 hours of request.
BCB Resolution 494: May 2026 Deadline
Payment institutions in Brazil must achieve compliance with BCB Resolution 494 by May 2026. Audit trail requirements and cybersecurity policy documentation should be prepared and validated now. Thinfinity deployments on OCI São Paulo satisfy all BCB audit trail requirements automatically.
Thinfinity Workspace generates this audit trail automatically at the session layer, capturing user identity (federated from Active Directory or LDAP), session timestamps with sub-second precision, source IP, and any policy exceptions. Session logs are exportable to OCI Autonomous Data Warehouse or the bank’s existing SIEM via REST API, enabling rapid response to BCB audit requests.
PIX, CoDi, and Real-Time Payment Latency Constraints
Brazil’s PIX, Mexico’s CoDi, and Colombia’s Transfiya all operate in sub-second latency windows. Real-time payment confirmation and fraud detection workflows cannot tolerate perceptible latency increases. OCI’s regional strategy addresses this through proximity: São Paulo delivers sub-10ms latency to PIX participants; Querétaro provides equivalent latency to Mexico’s CNBV network; and planned Santiago and Bogotá regions serve Chile and Colombia. Thinfinity’s H.264 hardware-encoded session delivery minimizes transcoding latency, ensuring banking applications running in virtual sessions experience responsiveness equivalent to local execution.
Global Regulatory Comparison Matrix
The table below summarizes how Thinfinity VDI on OCI maps to each regional framework’s key requirements:
| Requirement | USA (GLBA / FFIEC / PCI) | EU (DORA / PSD3 / GDPR) | LATAM (LGPD / BCB) | Thinfinity VDI on OCI |
|---|---|---|---|---|
| MFA | Required for all NPI access | Required for PSD3 transaction verification | Required per BCB Resolution 4.893 | Gateway enforces MFA at session initiation. Integrates with SAML, LDAP, Microsoft Authenticator, Duo, Okta, RSA, FIDO2. |
| Encryption | In-transit and at-rest (GLBA, PCI v4.0) | In-transit and at-rest (DORA ICT framework) | In-transit and at-rest (LGPD Art. 32, BCB 3.909) | OCI Block/Object Storage at-rest encryption; TLS 1.3 in-transit. Endpoint never receives plaintext. |
| Audit Trail | FFIEC expectations; 5–7 years retention | Incident logs, 5+ years (DORA) | BCB 3.909; 90+ days minimum | Captures user identity, timestamps, source IP, app interactions. Exportable to SIEM via syslog/REST. |
| Endpoint Security | No sensitive data on endpoints | No sensitive data on endpoints (DORA) | No personal data on endpoints (LGPD) | Endpoints receive screen stream only. Clipboard, USB, file transfer configured per role. |
| Third-Party Risk | Vendor SOC 2 / ISO certs (OCC 2023) | ICT third-party provider oversight (DORA) | Vendor audit capability (LGPD) | OCI: SOC 2 Type II, ISO 27001, FedRAMP High. Thinfinity: audit logs and session recordings. |
| Incident Response | 30-day breach notification (GLBA) | 24-hour critical incident notification (DORA) | 30-day breach notification (LGPD) | Session recordings provide forensic evidence for breach scope analysis. |
| Penetration Testing | Annual pentesting required (GLBA) | Annual scenario analysis (DORA) | Recommended (LGPD), supported by BCB | Scope reduced to OCI infrastructure + Gateway + session hosts. Smaller scope = lower cost. |
| Data Residency | Not mandated; FedRAMP available | EU-only (GDPR Art. 45) | ANPD-approved jurisdiction | OCI regions: Ashburn, Chicago, Phoenix (US); Frankfurt, Amsterdam, London, Marseille, Stockholm, Milan (EU); São Paulo, Querétaro (LATAM). |
Reference Architecture: Banking VDI on OCI — Global Deployment
OCI Region Strategy for Global Banks
Thinfinity VDI on OCI uses a hub-and-spoke regional deployment model optimized for each geographic market. For a global bank operating across all three regions, the architecture is:
United States Deployment
Primary region: Ashburn, VA (US East). Secondary: Chicago, IL (US Midwest). Tertiary: Phoenix, AZ (US West). For community banks with branch networks in specific regions, primary deployment in the nearest commercial region provides <20ms latency to all branches. For institutions with government banking relationships, OCI’s FedRAMP High regions in Ashburn and Chicago provide additional security certifications. Multi-region failover via OCI FastConnect or site-to-site IPSec VPN enables session persistence — active sessions in Ashburn automatically fail over to Chicago with <5 second reconnection.
European Union Deployment
OCI operates six EU regions as of 2026: Frankfurt, Amsterdam, London, Marseille, Stockholm, and Milan. DORA compliance requires EU data to remain within the EU. For multi-country European banks, a hub-and-spoke model deploys a primary Thinfinity Broker and session host pool in Frankfurt, with regional nodes in Amsterdam, London, and Stockholm for branch networks in respective countries. Session persistence across EU regions is enabled via dedicated network backbone, ensuring sub-100ms failover latency.
Latin America Deployment
Primary region: São Paulo, Brazil (OCI GRU). Secondary: Querétaro, Mexico (OCI MX1). Tertiary: Santiago, Chile (planned 2026). For Brazilian banks, São Paulo satisfies LGPD, ANPD, and BCB requirements with data remaining in-country. For Mexican institutions, Querétaro provides in-country processing for CNBV compliance. For multi-country LATAM groups, OCI Cloud Manager enables a unified management console with independent Broker instances per country.
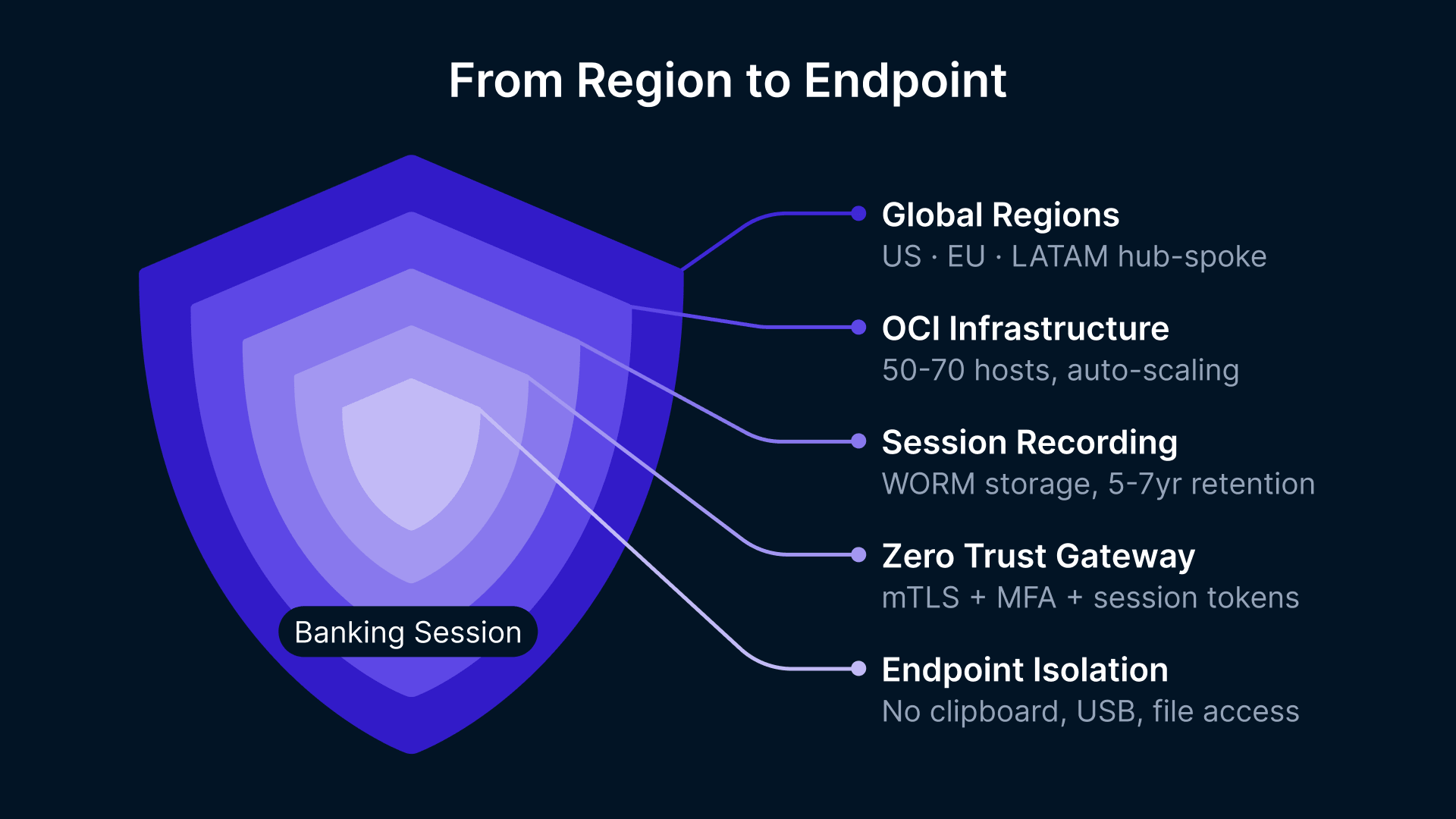
Infrastructure and Security Layer
The following architecture is sized for a 500–2,000 user bank with a distributed branch network.
Compute Sizing by Role
Thinfinity session hosts are deployed on OCI VM.Standard.E4.Flex shapes, with resource allocation by role:
- Teller workstations: 1 vCPU, 4 GB RAM per session (10–15 tellers per session host).
- Loan officer / branch manager: 2 vCPU, 8 GB RAM per session (8–10 per session host).
- Back-office analysts: 2 vCPU, 8 GB RAM per session (8–10 per session host).
- Treasury / FX trading: 2 vCPU, 8 GB RAM per session (higher memory for market data feeds).
For a 1,000-user deployment, approximately 50–70 session host VMs are required. Auto-scaling policies adjust host pool size based on concurrent session demand, reducing infrastructure cost during off-peak hours.
Zero Trust Session Initiation
Thinfinity Gateway acts as a reverse proxy for all inbound connections. No RDP or direct session access is exposed. All connections flow through the Gateway, which enforces certificate-based mTLS authentication, MFA via SAML/LDAP, rate limiting and DDoS protection, and session token generation with automatic expiration (default 8 hours, configurable per role). Session tokens are short-lived and unique per session, preventing hijacking or token reuse.
Session Recording and Immutable Storage
Every session is recorded in real-time to OCI Object Storage. Recording is configurable by role: full recording for tellers and loan officers (high customer data exposure), light recording for back-office staff. All recordings are stored in a WORM-enabled bucket with retention policies: 5–7 years for tellers, 2–3 years for back-office. Recording metadata is indexed in OCI Autonomous Data Warehouse, enabling queries like “Show all sessions by user X on date Y accessing customer PII.”
Endpoint Isolation Policies
Session policies enforce data-exfiltration controls by role. Clipboard redirection is disabled for tellers and loan officers accessing customer data; enabled for back-office staff performing administrative functions. USB device access is blocked by default and enabled only for IT staff with explicit approval. File transfer is restricted to OCI File Storage mounted in the session. Printer access is restricted to approved network printers only.
Core Banking Application Compatibility
Thinfinity VDI supports all major core banking platforms used in the US, EU, and LATAM. All platforms listed below run as standard Windows or Java applications on OCI session hosts without modification or containerization.
| Platform | Provider | Region | Compatibility |
|---|---|---|---|
| SilverLake System | Jack Henry & Associates | USA | Windows client — fully compatible. |
| Episys | Jack Henry & Associates | USA | Browser-based — fully compatible via Thinfinity RBI. |
| Premier / Precision / Signature | Fiserv | USA | Windows client — fully compatible. |
| IBS / Profile | FIS | USA | Windows and browser — fully compatible. |
| D3 Banking | NCR Voyix | USA | Browser-based — fully compatible via Thinfinity RBI. |
| nCino | nCino (Salesforce) | USA | Browser application — fully compatible. |
| Temenos T24 | Temenos | EU / LATAM | Windows / Java client — fully compatible. |
| Finastra | Finastra | EU | Windows client — fully compatible. |
| SAP Banking | SAP | EU | Windows client — fully compatible. |
| Avaloq | Avaloq | EU | Java client — fully compatible. |
| Cobis Core | Cobis | LATAM | Windows client — fully compatible. |
| Topaz Banking | Topaz | LATAM | Windows client — fully compatible. |
| Totvs Protheus | Totvs | LATAM | Windows client — fully compatible. |
Deployment Model: Phased Rollout for Regulated Environments
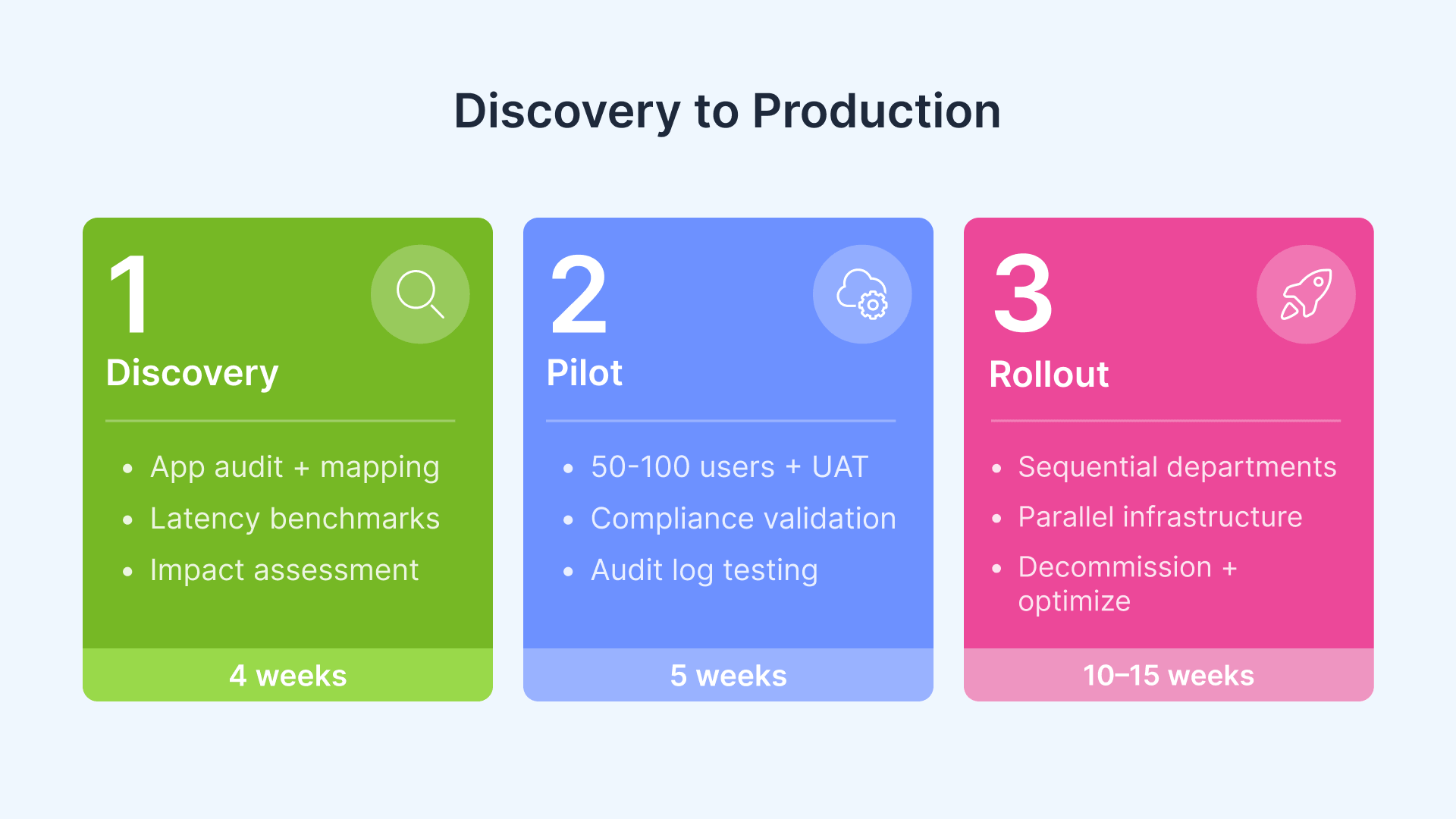
Banking VDI migrations carry elevated risk: core banking systems process customer deposits, execute payments, and maintain fiduciary relationships. A phased approach mitigates risk and ensures regulatory compliance validation at each stage.
Phase 1: Discovery and Regulatory Impact Assessment (4 weeks)
- Application inventory audit: Catalog all core banking, middleware, and auxiliary applications per user role. Identify legacy ActiveX controls, Citrix-specific delivery mechanisms, or local installation dependencies.
- GLBA / DORA / LGPD compliance mapping: Map each control requirement to the VDI architecture layer — Gateway, session, or OCI infrastructure.
- Data flow analysis: Identify any applications that write banking data to local %Temp% or %AppData% paths. Determine whether data can be redirected to OCI File Storage or blocked by policy.
- OCC / BCB notification assessment: Determine whether VDI migration qualifies as a material change requiring regulatory notification. Most deployments qualify as infrastructure modernization rather than core system change.
- Latency benchmarking: Establish baseline latency from the OCI region to each branch, remote office, and major user location.
Phase 2: Pilot with Compliance Validation (5 weeks)
Deploy a production-equivalent environment on OCI targeting 50–100 users from a representative department (back-office, branch, treasury).
- Technical UAT: Core banking application performance, session reconnection, profile loading (FSLogix), and MFA integration tested by pilot users for minimum 4 weeks.
- GLBA / DORA compliance validation: Generate GLBA control mapping documentation for Qualified Individual review. For DORA-subject institutions, compile incident logging evidence and third-party audit materials.
- LGPD data flow review: For LATAM deployments, DPO reviews session architecture to confirm no personal data traverses to endpoint devices.
- Audit log testing: Generate 30-day sample of session logs. Verify format and completeness meet FFIEC, EBA, and BCB examination expectations. Test export to SIEM.
- Regulatory readiness review: Conduct compliance review with legal and risk teams. Address any examination or audit concerns identified during pilot.
Phase 3: Department Rollout with Change Management (10–15 weeks)
Sequential department-by-department rollout, maintaining parallel physical and virtual desktops throughout the transition:
| Phase | Weeks | Scope | Compliance Deliverable |
|---|---|---|---|
| 3A — Non-critical | 10–14 | Back-office, treasury, risk, operations | None (internal functions) |
| 3B — Front-office | 15–18 | Tellers, loan officers, branch managers | Change management comms + support SLA |
| 3C — Decommission | 18–24 | Physical endpoint retirement + data wipe | Decommission register + asset disposal certification |
| 3D — Optimization | 24+ | Auto-scaling tuning, session recording archive compression, regional failover testing | Operational runbook + SLA review |
Map Your Bank’s Compliance to OCI
Thinfinity’s delivery team works with banking IT architects and CISOs across the Americas, Europe, and LATAM to design regulatory-compliant VDI deployments. Schedule a 30-minute architecture walkthrough tailored to your institution’s compliance requirements, regulatory jurisdiction, and technical stack. We provide GLBA, DORA, and LGPD compliance mapping documents and OCI cost modeling for your deployment profile.
Thinfinity Advantages for Global Banking: Online and Air-Gapped Resilience
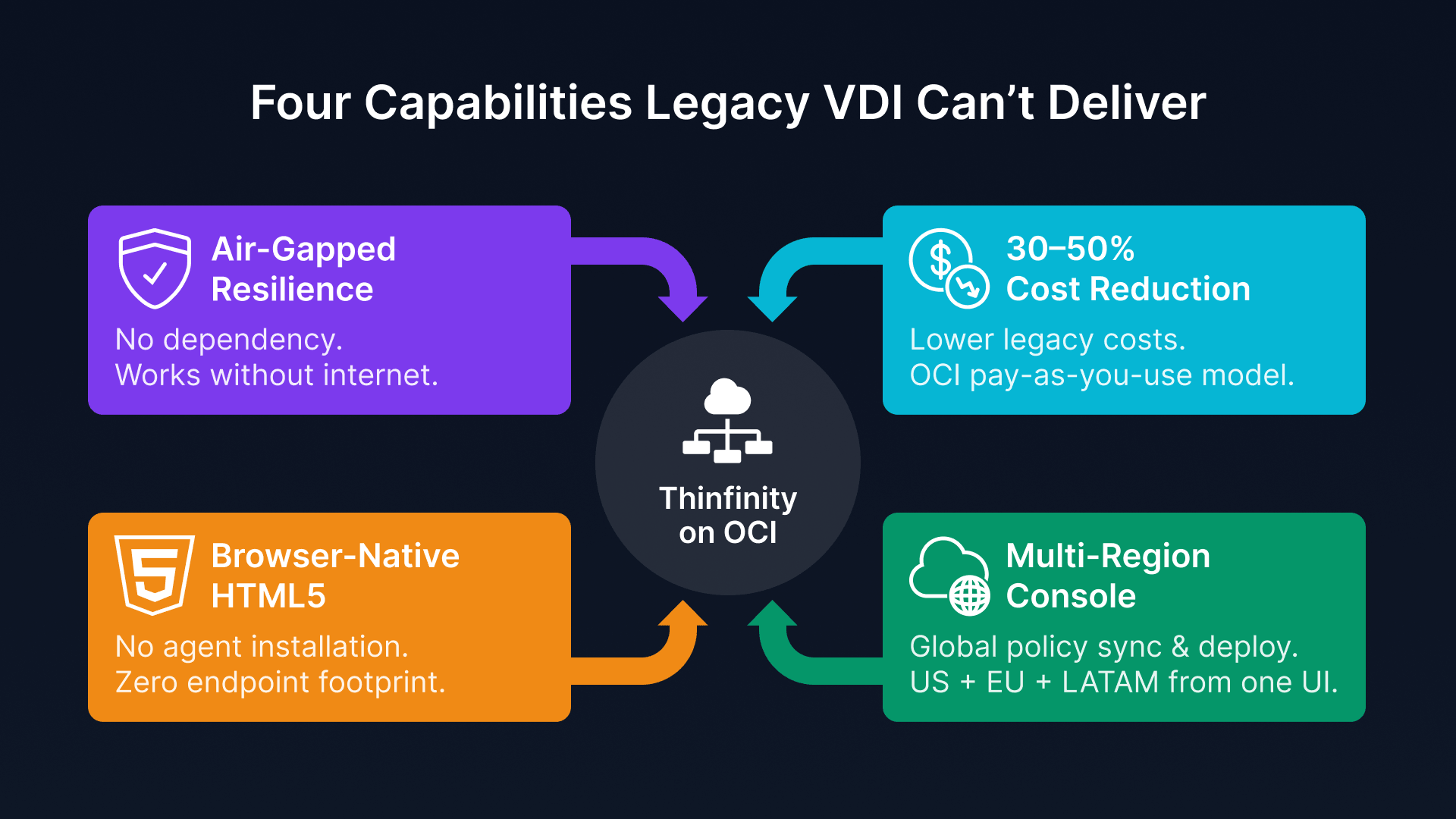
A critical advantage of Thinfinity Workspace for banking deployments is its ability to operate fully offline or in air-gapped environments. Many banking institutions operate secure zones where sessions must run without cloud licensing dependencies or internet connectivity to third-party services.
Offline Session Delivery
Thinfinity Workspace brokers can run in air-gapped mode, issuing session tokens and managing desktop pools without internet connectivity. If a bank’s OCI tenancy experiences a DDoS attack or if connectivity to OCI is briefly unavailable, active user sessions continue running. Session reconnection and new session initiation are queued and processed once connectivity is restored. For banking, this resilience is critical: tellers cannot serve customers if their virtual desktop session fails due to transient network issues.
Browser-Native HTML5 (No Agent Installation)
Thinfinity clients are delivered as HTML5 applications accessed through any standard browser (Chrome, Firefox, Safari, Edge). No client software installation is required on endpoints. This eliminates software deployment complexity across branch networks, reduces patching overhead, and enables secure-by-design: endpoints running Thinfinity have no persistent applications, no local configuration, and no attack surface.
OCI Cost Advantage vs. Legacy VDI
Thinfinity on OCI delivers better cost efficiency than traditional VDI (Citrix, VMware) or legacy on-premises deployments. OCI’s flexible compute pricing, lack of perpetual licensing fees, and consumption-based model reduce total cost of ownership by 30–50% compared to legacy on-premises infrastructure. For community banks and regional institutions, this cost advantage enables VDI adoption that would not be justified under legacy licensing models.
Multi-Region Management from a Single Console
Thinfinity Cloud Manager provides unified management across all regional deployments. A bank with OCI session host pools in Ashburn, Frankfurt, and São Paulo manages all three from a single Thinfinity console. User provisioning, session policy updates, and application deployments are synchronized across regions. Security updates and patches are deployed globally within a defined maintenance window.
Conclusion: The 2026 Banking Imperative
By 2026, global banks operating across the US, Europe, and Latin America face a unified regulatory imperative: centralize endpoint security, eliminate data stored on devices, and provide immutable audit trails of all banking operations. GLBA Safeguards Rule, FFIEC NIST CSF 2.0 expectations, DORA resilience requirements, LGPD data protection obligations, and BCB audit trail mandates all converge on the same technical solution — Virtual Desktop Infrastructure on a certified, audited cloud provider.
Thinfinity Workspace on Oracle Cloud Infrastructure delivers this solution with examination-ready compliance evidence, reduced operational overhead, and cost advantages compared to legacy VDI or distributed thick-client architectures. For CIOs and CISOs evaluating modernization strategies in 2026, a Thinfinity-on-OCI deployment is not a competitive advantage — it is a regulatory requirement becoming table stakes. The question is not whether to modernize; it is whether to move now or face examination findings and enforcement action.
Frequently Asked Questions
Does Thinfinity VDI satisfy the GLBA Safeguards Rule MFA requirement?
Yes. The Thinfinity Gateway enforces MFA at session initiation for all users accessing banking applications, integrating natively with Microsoft Authenticator, Duo, Okta, RSA SecurID, and FIDO2 tokens. This satisfies GLBA Safeguards Rule MFA at a single enforcement point — covering branch workstations, remote laptops, and mobile devices without per-device configuration.
How does FFIEC examine a Thinfinity VDI deployment under NIST CSF 2.0?
Examiners evaluate VDI deployments using NIST CSF 2.0’s Govern, Identify, Protect, Detect, Respond, and Recover functions. Key evidence requested: role-based access control policies, session activity logs exported to SIEM, MFA configuration documentation, and vendor risk assessment documentation for OCI. Thinfinity on OCI provides examination-ready evidence across all NIST CSF 2.0 functions.
Is OCI FedRAMP authorized for regulated banking workloads?
Yes. OCI holds FedRAMP High authorization for its US Government cloud regions (Ashburn, VA and Chicago, IL). Commercial OCI regions are used by numerous federally regulated institutions and are covered by OCI’s SOC 2 Type II and ISO 27001 certifications, which satisfy OCC 2023 third-party risk management documentation requirements.
How does DORA enforcement work for Thinfinity deployments on OCI?
DORA requires banks to assess third-party providers through due diligence (SOC 2 reports), contractual provisions (DPAs), and ongoing monitoring. Evidence includes OCI’s SOC 2 Type II and ISO 27001 certifications, the OCI data processing agreement, and incident notification procedures allowing the bank to retrieve session recordings within DORA’s 24-hour critical incident window.
Does LGPD require banking data to remain in Brazil?
LGPD does not mandate strict data sovereignty, but it requires offshore processing to occur in jurisdictions approved by ANPD. OCI’s São Paulo region is the appropriate choice for Brazilian banks. Under Thinfinity’s server-side session model, all banking data remains on OCI São Paulo compute — remote users receive only encoded screen streams and send keyboard/mouse input.
How does Thinfinity address BCB Circular 3.909 audit trail requirements?
Thinfinity automatically logs all session events: user identity, timestamps, source IP, session duration, and policy exceptions. Logs are exportable to the bank’s SIEM via syslog or REST API. Session recording provides the visual audit record required by BCB examination procedures, retained in OCI Object Storage with configurable retention policies.
Are PCI DSS v4.0 MFA and endpoint isolation controls sufficient for CDE compliance?
Yes. Requirement 8 MFA is enforced by the Thinfinity Gateway at session initiation. Requirement 1 network segmentation and Requirement 2 secure configuration are satisfied through OCI’s network ACLs isolating CDE session hosts. Requirement 7 access control is enforced via session policies restricting clipboard and USB access. Annual PCI DSS pentest scope is reduced to the OCI VCN and Thinfinity Gateway.
What is the migration timeline for a global bank with operations in US, EU, and LATAM?
A single-region deployment for 500–1,000 users typically requires 18–24 weeks. For a fully global rollout across all three regions running in parallel, total timeline is 24–30 weeks with staggered regional launches. Regional launches can overlap (US and EU pilots in parallel, EU and LATAM rollouts in parallel), accelerating the overall timeline.
How does Thinfinity handle multi-region failover and session persistence?
Thinfinity Cloud Manager supports session persistence across regional deployments. When a user connects to a Thinfinity Broker in Region A and Region A experiences an outage, the Broker initiates automatic failover to Region B. Active user sessions are migrated to session hosts in Region B with automatic reconnection, typically within 5 seconds.
Which core banking platforms are fully compatible with Thinfinity on OCI?
All major core banking platforms used in US, EU, and LATAM are fully compatible: Jack Henry SilverLake and Episys, Fiserv Premier, FIS IBS, Temenos T24, SAP Banking, Finastra, Avaloq, Cobis, Topaz Banking, and Totvs. All run as standard Windows or Java applications on OCI session hosts without modification.